Earlier this month Equifax, one of the largest consumer credit reporting agency in the world, declared that their systems where breached between mid-May and July. The breach involved attackers gaining access to sensitive customer data which included social security numbers of approximately 143 million US citizens. Apart from this, the breach has also compromised data relating to customers based out of other operational regions of Equifax such as the United Kingdom and Canada. Further elaborating on the issue Brian Kerbs, an American information security blogger has highlighted the sloppy security practices of Equifax Argentina in an sloppy security practices of Equifax Argentina in an article posted last week. He also sheds light on the fact that the company failed to secure vital information regarding its employees based out of the Latin American country.
Understanding Equifax’s Business Operations
Equifax is actively involved in collection and aggregation of information of about 800 million consumers and more than 88 million companies across the globe. A huge chuck of its business operations includes maintaining records of the ability of consumers to pay back their financial debts to banks. The company rates individuals using credit points which are referred to by financial institutions to understand the risk factor involved while lending loans. The credit points that Equifax rewards an individual determines his/her credit limits and on whether it should be increased or decreased.
The Vulnerability Exploited by Attackers to Gain Access to Equifax Database
There are reports that attackers exploited the Apache Struts vulnerability to gain access to the Equifax database. The Apache Struts is widely used framework that has extensive abilities to cater to the growing requirements of enterprises. A lot of companies use the Apache Struts framework to create enterprise-ready Java web applications. In the case of Equifax the Apache Struts framework was used to create publicly accessible web applications which are used by consumers to inquire about their credit report.
There are two Apache Struts vulnerabilities tracked as CVE-2017-9805 and CVE-2017-5638, which attackers must have exploited for the data theft cyber crime.
CVE-2017-9805
This vulnerability was reported on July 17 and was patched with the release of Apache Struts 2.5.13 and 2.3.34. The disclosure of this vulnerability has resulted to all versions of struts released after 2008 exposed to a flaw in its framework’s REST plugin.
The vulnerability tracked as CVE-2017-9805 could allow attackers to remotely execute arbitrary code on any server that runs an application created with the help of the struts framework and the REST communication plugin.
The security team that discovered this flaw in the Apache Struts framework has concluded that, “The weakness is caused by the way Struts deserializes untrusted data”. The team also intends to publish a simple working of the vulnerability at a later stage.
CVE-2017-5638
This vulnerability is a bug that causes remote code execution when performing file upload with the help of Jakarta Multipart parser. The vulnerability tracked as CVE-2017-5638 has been reportedly been exploited by attackers using simple Linux commands ‘whoami’ in order to gain information about the user the server is running. Commands such as ‘ipconfig’ are used to gather information regarding network configuration of a server.
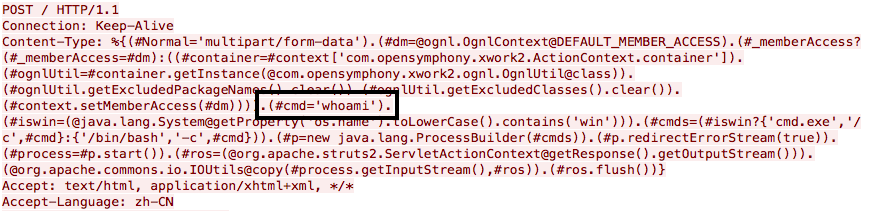
The CVE-2017-5638 flaw was also mentioned in a security advisory released by Apache on March 7, 2017. The affected versions of Apache are 2.3.5 – 2.3.31 and Apache Struts 2.5 – 2.5.10.
It is still not clear which of these vulnerabilities must have been used by the attackers to breach Equifax but, according to an article on Apache Struts Vulnerability Exploited in the Wild written by Eduard Kovacs (international correspondent of SecurityWeek) it is more likely that the attackers must have used CVE-2017-5638 vulnerability as it was disclosed back in March this year.
Click here to download the latest version of Apache Struts.
