CRYSTAL EYE XDR
eXtended Detection and Response
It usually takes 277 days for organisations to identify and contain a security breach *
Crystal Eye can achieve this in as little as 24 minutes **
Crystal Eye XDR protects, detects and responds to threats across your whole organisation, all from a single unified platform. It secures your organisation from the cloud to the endpoint with a range of integrated security controls.

Problems
- Security incidents are becoming more complex while compliance obligations are becoming harder to meet.
- Organisations are struggling with too many products from different vendors which aren’t integrated together.
- Companies need to be able to quickly identify real threats from all the noise and then initiate rapid response procedures to minimise business impact.
Solution
- XDR solves these problems by avoiding the complexity of configuring and monitoring separate security systems.
- XDR offers a single unified platform that delivers security protection, threat detection and incident response across your whole organisation.
Benefits
- Reduce risk of a security incident.
- Reduce time to detect and respond to an event.
- Reduce cost of securing your business.
CRYSTAL EYE XDR ARCHITECTURE
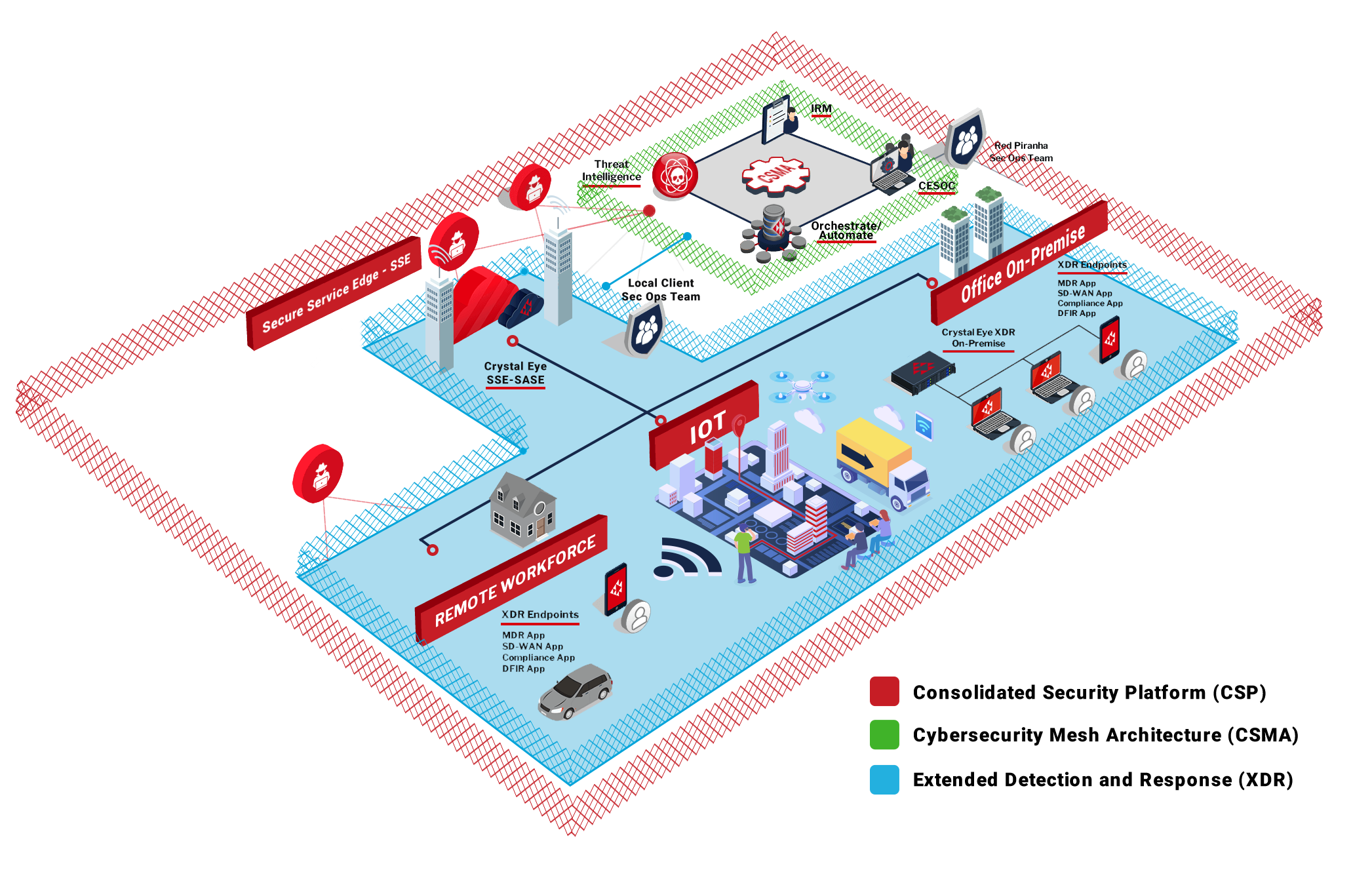
Deployment Options
Crystal Eye XDR is available in the following flexible deployment options:
XDR – eXtended Detection and Response
- XDR involves the collection and correlation of event data from endpoint, network and cloud sensors to identify real threats anywhere in your environment and automatically trigger a coordinated response to secure your business.
- The first fully-integrated detection and response platform is ready to go out-of-the-box, so it delivers a consistent level of security without the complexity of integrating products from multiple vendors.
- Our network-based and cloud-based sensors (Crystal Eye XDR) deliver Network Detection & Response (NDR), in combination with our host-based sensors (Crystal Eye XDR Endpoints) deliver Endpoint Detection and Response (EDR) which all work together to deliver eXtended Detection and Response (XDR). Best NDR and Threat Detection and Incident Response in the market with 5 times more visibility across your Network, Endpoints and cloud infrastructure.
- Crystal Eye Orchestrate is our centralised management console which takes care of the service delivery and also acts as a data lake to collect all the data for correlation and response coordination. This is a significantly simpler process due to the standard data format and shared data storage used across the Crystal Eye products, which avoids the labourious task of normalising and correlating data from different technologies.
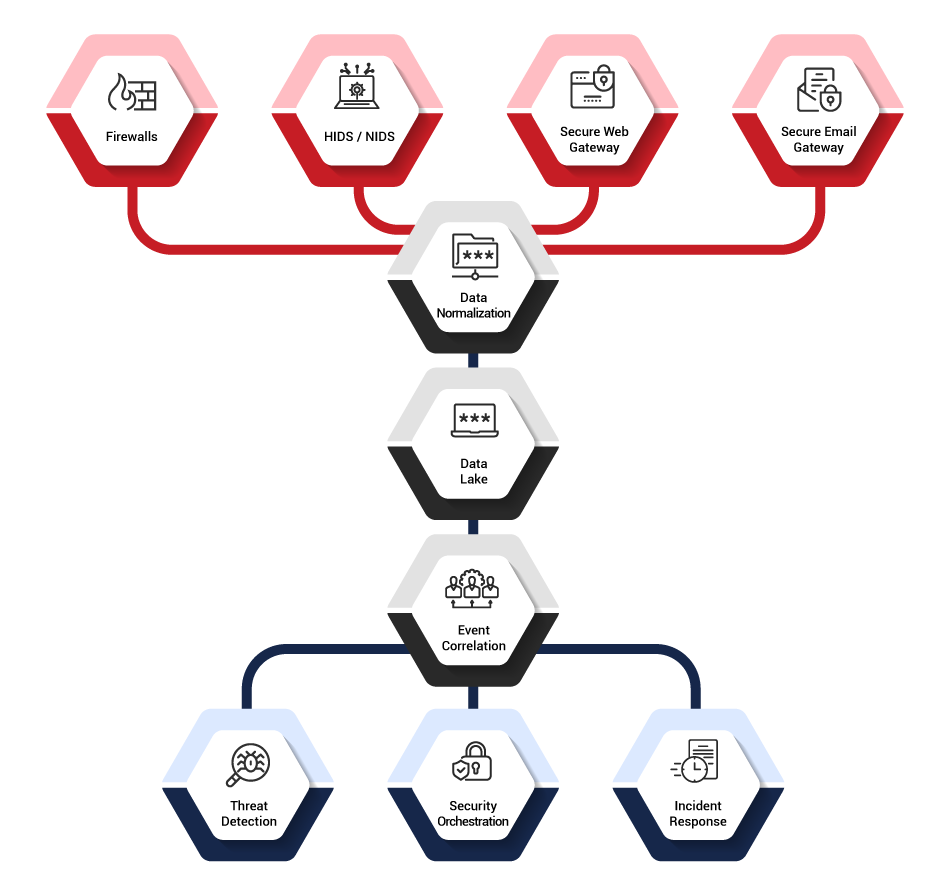
More than SIEM
- XDR avoids the complex integration required with Security Information & Event Management (SIEM) and breaks down the silos between different systems by having a single data store for all events.
- Where SIEM focuses on pulling the data together into events, XDR has the added benefit of pro-active and automated rapid response to stop threats in their tracks before real damage occurs. XDR goes a step further to provide advanced threat detection with research analysis labs to support defensive efforts.
Integrated SOAR
- Our XDR solution has integrated Security Orchestration, Automation & Response (SOAR) processes which allow you to automate responses to low-risk threats and coordinate responses to high-risk threats with the relevant resources.
- These capabilities are typically not accessible for most organisations, but our integrated SOAR approach provides a comprehensive, cost effective response solution available to businesses of any size. Our automated incident response process gets executed immediately when a breach occurs and is significantly cheaper than alternative options.
Key Features of Crystal Eye XDR
Passive Encryption Control Our Advanced Passive Encryption Control technology protects networks with application-specific fingerprinting to establish traffic baselines allowing you to secure your network even with IoT devices present. Azure AD Use your Crystal Eye XDR appliance to capture extended Microsoft 365 signals useful in threat detection with all Microsoft subscription levels, usually reserved for corporate subscribers only. Read more on our Azure AD Cloud Monitoring. | Wireguard Crystal Eye XDR appliances also support the faster and more secure WireGuard protocol as well as traditional VPN technologies like SSL and IPSec VPN. Threat Hunting Gain visibility and in-depth information and signals around your network to efficiently detect and locate threats or potential threats in your network with our comprehensive Threat Hunting Dashboard. |
CRYSTAL EYE XDR DATA FLOW ARCHITECTURE
MDR – Managed Detection and Response
- We offer a fully managed XDR solution to take on the responsibility for operating the platform, so our certified security analysts in our 24/7 SOC are available to investigate and resolve security incidents in real-time across your network and help coordinate rapid response activities.
- Our integrated managed services streamline security operations with incident response playbooks and threat hunting supported by our Automated Actionable Intelligence
- This can be fully managed or can dovetail into your SecOps team to provide additional support.
- This also allows MSPs to deliver fully Managed Detection and Response (MDR) services, delivered via our Crystal Eye Orchestrate console.
Integrated Vulnerability Management
- Crystal Eye offers vulnerability tuning within the IPS engine to provide virtual patching against known vulnerabilities identified in your environment.
- The moment you install Crystal Eye, you can schedule a Vulnerability Scan of your environment. This feature shows you the number of vulnerabilities that have been detected, then it shows you how many have exploits which are leaving you at risk. Armed with this knowledge, you can implement the recommended changes on the vulnerable systems or tune the inbuilt IDPS and firewall to stop the threat at the Crystal Eye.
IRM – Integrated Risk Management
- The Crystal Eye Integrated Risk Management (IRM) solution provides an automated and integrated approach to meeting your compliance obligations. It pulls together relevant compliance information and controls from multiple points across your network into a central dashboard that allows you to manage and report on that information to ensure you're compliant to a range of standards and provides a snapshot of your compliance posture at a point in time.
- The compliance journey can be a pain-staking process that requires a lot of investment in time and resources. Our IRM module automates the majority of the work required to achieve and maintain compliance, thereby significantly reducing the cost for your business to gain a competitive edge in the market.
- Crystal Eye IRM can also be integrated into our eCISO™ (electronic Chief Information Security Officer) product and vCISO (virtual Chief Information Security Officer) service to deliver a comprehensive solution to Integrated Risk Management.
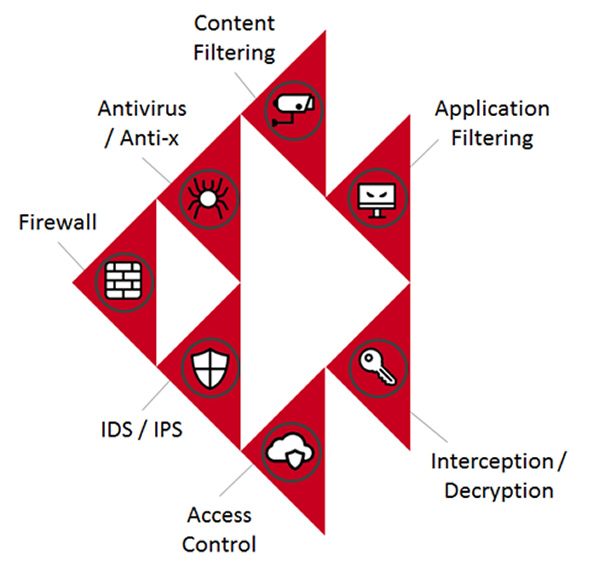
Crystal Eye Firewall
The Crystal Eye platform includes a full-featured next-generation firewall with a range of integrated security controls such as firewall, IPS, secure web gateway and secure email gateway. This ties into our overall XDR platform to deliver superior protection for your business.
Threat Intelligence
Our Automated Actionable Intelligence (AAI) delivers the most timely and accurate threat intelligence, all integrated into the Crystal Eye platform. Cyber Threat Intelligence is an essential component of an organisation's overall security strategy, as it provides a systematic and comprehensive approach to identifying and addressing potential threats. Red Piranha is a world leader in the collection and processing of threat intelligence. We are also a member of the Cyber Threat Alliance based out of Washington, DC and are one of its top contributors.
Our fully-verified intelligence feeds provide deeper context and integrates seamlessly with the platform to enhance your decision-making. This helps prevent attacks and reduce risk by helping you understand the historical context of where these cyber threats originated, who is behind them, when have they attacked, what methods they used and what they're after. Get on-demand access to current and historical metadata on IPs, domains, and other related threat intelligence to help research cyber threats and investigate incidents.
In addition to reputation intel, you get condemnation evidence, deep context, history, and detection information. It's all searchable in an easy-to-use cyber threat analysis portal that includes:
- Trends and timestamps of when a threat was seen and the associated category
- Type of threat and exploit kit names when available
- Related samples used in associated or related attacks
- Actionable IP and Domain Reputation intelligence
Red Piranha provides up-to-date managed IDPS rule sets aimed at giving actionable protection and detection capability. We serve our customer base with over 46,000 dedicated rules that allow the best-in-breed threat hunting capability, with the Red Piranha threat hunting team working round the clock to track threats and reduce risk to customers.
Get our Weekly Threat Intelligence Reports straight to your inbox, subscribe now.
An Integrated Approach
- Crystal Eye XDR delivers a comprehensive solution across a range of security areas, with the whole platform working together to protect, detect and respond to threats in your environment.
- This all works together to provide a single defence-in-depth platform to mitigate risks to your organisation.
- Our modular approach can be catered to meet the needs of each company, so you can pick and choose what matters most to you without implementing the whole solution.
- It's about business outcomes and managing risks specific to your needs, not just about technology for the sake of it.
* Cost of a Data Breach Report, Ponemon Institute, 2023
** Based on an actual customer case study












