
Zero Trust Architecture is a cybersecurity concept that assumes that no user, device, or network is inherently trustworthy. Instead, it requires strict authentication and access control measures to ensure that only authorised users and devices can access resources. Implementing Zero Trust Architecture can help protect against cyber-attacks and data breaches by limiting access to sensitive data and applications.
Zero-Trust compliance frameworks
Some popular Zero-Trust compliance frameworks exist that can assist in guidance for implementation, including the National Institute of Standards and Technology (NIST) Cybersecurity Framework, the Zero Trust Maturity Model (ZTMM), and the Cloud Security Alliance (CSA) Cloud Control Matrix. These frameworks guide a range of topics, including access control, network segmentation, identity and access management, and security monitoring.
In addition to these frameworks, several industry-specific compliance standards incorporate Zero Trust principles, such as the Payment Card Industry Data Security Standard (PCI DSS), the Health Insurance Portability and Accountability Act (HIPAA), and the General Data Protection Regulation (GDPR).
Effectively implement Zero Trust Architecture
1. IEC 62443 standards
A comprehensive approach to aspire when implementing Zero Trust principles can be found in OT standards set out in the IEC 62443. The IEC 62443 standards were developed by the International Electrotechnical Commission (IEC) in collaboration with industry experts, governments, and other stakeholders. The standards cover a wide range of topics, including risk assessment, network segmentation, access control, cryptography, incident response, and security management.
IEC 62443 is a set of international standards that define the security requirements for Industrial Automation and Control Systems (IACS). These standards provide a comprehensive framework for the design, implementation, and operation of secure IACS networks and applications, with the goal of protecting critical infrastructure from cyber-attacks. The framework outlines security Zones and Conduits as a way of implementing Zero Trust, this same approach can be taken in IT environments to develop a segmentation strategy within networks.
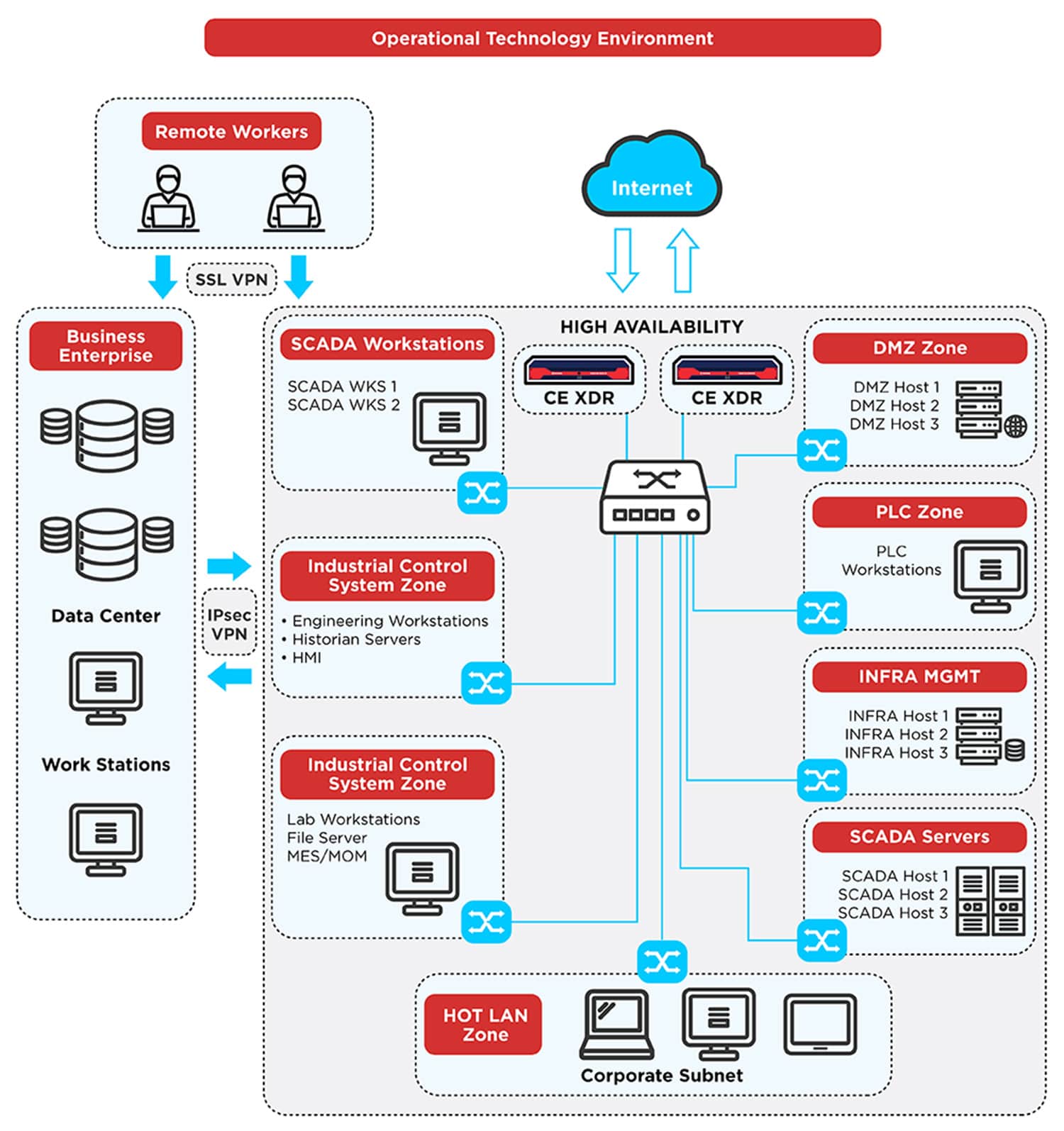
Zero Trust with clean network zones and controlled conduits can increase efficacy in detection engineering by reducing the attack surface and providing a clear boundary between trusted and untrusted zones. This approach involves segmenting the network into smaller, controlled zones and implementing strict access controls to limit the flow of traffic between them.
By enforcing a Zero-Trust policy, all users, and devices, regardless of their location or level of access, must be authenticated and authorised before being granted access to network resources. The clear boundaries between clean network zones can make it easier for detection engineering teams to monitor and analyse network traffic, improving their ability to detect and respond to potential threats.
This can improve the detection and response capabilities of security teams by using the clear definition of set policies to improve detection efficacy, reduce false positives, and by limiting the potential impact of security incidents and reduce the risk of lateral movement by attackers.
To begin implementing Zero Trust architecture with Crystal Eye and a network, data governance owners must first define their organisation's assets and establish a hierarchy of access control policies. It allows clear governance principles that define what assets should and are allowed to traverse the network and connect to other assets. It involves mapping out the network architecture, and digital assets and identifying potential threats and attack vectors. With Crystal Eye threat detection and response capabilities, organisations can detect threats and respond quickly to security incidents, even across complex, multi-cloud environments.
2. Configuration Management Database (CMDB) for Asset Management
Crystal Eye OS manages assets on the network with a mapping function. Crystal Eye Orchestrate also includes a SaaS CMDB in its Security Mesh architecture. A Configuration Management Database (CMDB) is used as a foundation for asset management by providing a centralised repository for storing and managing information about digital assets.
It is important to note that we include and consider assets not just in the physical sense but at the digital layer. So, software libraries and document assets are also considered.
Here are some ways in which a CMDB can be used for asset management:
1. Inventory Management: Maintain a comprehensive inventory of all IT assets, including hardware, software, and other components. This inventory can include details such as asset type, model, manufacturer, serial number, and other relevant attributes.
2. Asset Tracking: Track the location and status of IT assets throughout their life cycle. It helps organisations identify underutilised or overutilized assets, track the movement of assets between departments or locations, and manage asset leases and contracts.
3. Change Management: Track changes made to IT assets, including changes to hardware configurations, software versions, and other components. It helps organisations maintain an accurate picture of their asset landscape and ensure that changes are properly documented and managed.
4. Incident Management: A CMDB is used to support incident management in CESOC by providing visibility into the configuration of IT assets that may be contributing to incidents or service disruptions. This can help organisations identify root causes and quickly resolve issues.
5. Reporting: A CMDB can be used to generate reports and analytics on asset utilisation, maintenance, and other key metrics. This can help organisations optimise their asset management processes, identify areas for improvement, and ensure compliance with relevant regulations and standards.
Crystal Eye Orchestrate CMDB is a valuable tool for asset management, providing a central source of truth for IT assets and enabling organisations to make informed decisions about how best to manage their risk associated with the asset landscape.
Crystal Eye also has the capability to run SBOMs and check against vulnerabilities in Docker and Container environments.
3. Identity and Access Management
Once a complete picture of assets and the risks and governance over those assets has been determined, the next step is to implement Identity and Access Management (IAM) policies. Red Piranha can assist with our eCISO program to help build a strategic roadmap. With Crystal Eye, risk owners can easily set up IAM policies to ensure that only authorised users and devices can access sensitive data and applications.
Administrators can configure Role-Based Access Control (RBAC) policies to grant or deny access based on user roles and permissions. Crystal Eye also provides advanced analytics and visibility into user behaviour, enabling security teams to detect anomalies and potential threats quickly.
In addition to IAM policies, data governance owners and IT administrators should also implement network segmentation and micro-segmentation policies to limit the lateral movement of threats within their network. With Crystal Eye, administrators can segment their network based on workloads, applications, and data types, limiting access to sensitive resources to only authorised users and devices.
4. Passive Encryption Control
The use of Custom security zones and apps like the Passive Encryption Control allow for correct segmentation and access control should be implemented based on risks. Red Piranha runs Continuous Threat Exposure programs via eCISO to assist with the implementation of correct security zones and then reduction of risk to achieve Zero Trust Architecture.
The Passive Encryption Control application is specifically designed to passively model traffic originating from a device itself. This baseline state of network activity is created during network segmentation and device mapping and uses patented fingerprinting technology to baseline software passively on the device.
Crystal Eye continuously monitors network traffic for any deviations from the baseline of that device encryption software triggering events that can be used for a Moving Target Defence. Passive Encryption Control can identify potentially malicious activity and alert the user to take appropriate actions or be set to auto-block that device from communicating on the network yet still allows the operation of the device itself. These actions may include blocking traffic, allowing traffic, blocking the IoT device from accessing the Internet or pinholing specific traffic to the IoT device.
By using Passive Encryption Control in conjunction with Zero Trust principles, organisations can significantly improve their security posture and reduce the risk of data ex-filtration through covert network channels. By adopting a proactive approach to network security, organisations can minimise the impact of attacks by detecting and responding to them promptly.
5. Secure Web Gateway
A Secure Web Gateway (SWG) is a security solution that is designed to provide web security for an organisation's users and devices by enforcing security policies for web traffic. It is used as a tool to achieve Zero Trust by providing an additional layer of security to protect against potential threats.
Some ways in which a Secure Web Gateway can be used to achieve Zero Trust include Identity and Access Management, Web filtering and content control, Increased Detection Engineering Capability and assist in Data Loss Protection (DLP) programs and reporting.
A Secure Web Gateway can be used to enforce Identity and Access Management policies, ensuring that only authorised users and devices are granted access to web resources. This helps to prevent unauthorised access to sensitive data and applications. A Secure Web Gateway should be used to filter web traffic and block access to malicious websites and applications based on strong policy configuration linked to company compliance documents outlined use of assets and asset control.
It can also be used to control access to specific types of content, such as social media or file-sharing websites, that may pose a security risk. Once policies are in place, increased Threat Prevention and Detection can be achieved based on policy configuration A Secure Web Gateway can be used to detect and prevent a range of web-based threats, including malware, phishing, and other types of attacks. It can also provide real-time threat intelligence and analysis to help organisations respond quickly to potential threats.
The Crystal Eye Secure Web Gateway can be a valuable tool for achieving Zero Trust by providing an additional layer of security for web traffic. By enforcing strict security policies and preventing unauthorised access to web resources, organisations can significantly reduce the risk of web-based threats and improve their overall security posture.
6. Advanced Firewall
The utilisation of borderless firewalling concepts to implement policy control across distributed environments can be achieved in Crystal Eye and is a concept used to implement Zero Trust in web applications and microservices.
So as perimeter-based security depreciates, a new geography of Zero Trust emerges. Ingress from anywhere and egress to anywhere, pass through this space, which is a security-defined control plane abstracted from network traffic. Filtering at the perimeter now involves algorithms that oversee a lake of data. This way, policy administration is brought as close to the action as possible. With Crystal Eye (CE) solutions, the workflow is traced, marked and checked against entity behaviour analytics, the integrated risk registry and policies, as well as dynamic policy resulting from threat intelligence allows for a moving target defence approach to be taken.
The CE Attack Surface Reduction endpoint app (CEASR) is an example of a host-based point at which the Zero Trust policy is enforced. The feature was originally designed to assist with meeting the ASD’s Essential 8 endpoint ISM control requirements and then auditing against those controls. It is a great tool to enforce strict host policy control on Windows endpoints and a way to audit and monitor those policy controls to reduce risk, particularly against Zero Day host attacks that may be missed by EDR.
While the CE XDR Security Platform extends firewalling to on-premises gateways, cloud-native gateways, and brokering points. Network segmentation also creates enforcement points between zones, and when interconnected by an SD-WAN, the use of new protocols like WireGuard as a Software Defined Perimeter (SDP) controller provides hybrid architecture access to brokered resources rather than directly joining networks.
Further Endpoint detection and protection should be considered as well as locking down important assets like Azure AD. The two main ways to implement access control here are with Tenant Control, which requires no license upgrades and the use of a Secure Web Gateway to control access and enforce policy into the tenant or with Conditional access, which will require license upgrades within the Azure Tenant.
Zero Trust Architecture for Hybrid Work Environments
The increasing trend of hybrid work environments, high cloud adoption, AI and automation, and BYOD poses significant security risks and compliance issues. The BYOD trend, although convenient for users to access organisations’ data from their personal devices, can lead to huge security risks if those devices are not properly secured. Device-based conditional access policies can be a saviour in such scenarios. These policies can control access to ensure that only authorised devices can access sensitive data.
To create device-based conditional access policies, the following requirements must be met: Only Office 365 users with specific roles, such as Global Administrator, Security Administrator, and Conditional Access Administrator, can create Conditional Access policies. Also, an Azure AD Premium P1 license is required for Conditional Access policies. Before applying device policies, users need to register their devices with the Azure AD device registration service.
Five essential device-based Conditional Access policies that should be set up in any Office 365 organisation are:
- Block access for unknown or unsupported device platforms
- Require an approved app or app protection policy for Android and iOS devices
- Require multi-factor authentication for Intune device enrolment
- Require multi-factor authentication to register or join devices to Azure AD
- Require compliant, hybrid joined devices, or MFA
Implementing a policy that blocks access to devices for unknown or unsupported device platforms will reduce the potential attack surface for any threats. The “Require approved app and app protection” policy ensures that employees access data solely through secure and authorised apps. Enabling the policy named “Require multi-factor authentication for Intune device enrolment” secures sensitive data access. Finally, requiring multi-factor authentication to register or join devices to Azure AD and requiring compliant, hybrid joined devices, or MFA can further enhance security.
Finally, any mature security program requires monitoring, and measurement risk owners can leverage Crystal Eye's integrated and inclusive world-leading Threat Intelligence, Vulnerability Management and subscription-based or on-demand Incident Response capabilities and services to monitor and respond to security incidents proactively. With real-time threat alerts and automated response actions, organisations can quickly mitigate potential threats and reduce their risk of a security breach.
Implementing Zero Trust Architecture with Red Piranha and Crystal Eye is no longer an architectural aspiration but a must-have for risk reduction that requires careful planning, configuration, and ongoing monitoring.
However, with Crystal Eye's comprehensive security capabilities, use of Red Piranha’s security support and CTEM programs, organisations can confidently implement a Zero-Trust framework that provides robust protection against cyber threats and ensures the security of their sensitive data and applications.
