| New Threats Detection Added | • SonOyuncuStealer • TORG Grabber |
| New Threat Protection | 109 |
| Newly Detected Threats | 9 |
Weekly Detected Threats
The following threats were added to Crystal Eye this week:
|
Threat name:
|
SonOyuncuStealer | |||||||||||||||||||||
|
SonOyuncuStealer is an information stealer written in C++ that is spread via fake software masquerading as a Minecraft mod launcher. It can capture screenshots, obtain credentials stored in web browsers, and exfiltrate other data from the local system via Discord webhooks.
|
||||||||||||||||||||||
|
Threat Protected:
|
02 | |||||||||||||||||||||
|
Rule Set Type:
|
|
|||||||||||||||||||||
|
Class Type:
|
Trojan-activity | |||||||||||||||||||||
|
Kill Chain:
|
|
|||||||||||||||||||||
|
Threat name:
|
TORG Grabber | |||||||||||||||||||||
|
TORG Grabber is an information stealer that has been active in development since December 2025. It’s commonly spread via fake software, cracked software, and ClickFix. As with most information stealers, it collects browser credentials, crypto wallets, local files, instant messaging and email credentials. Exfiltration is performed via HTTPS requests to the C2 servers, with other variants exfiltrating data via custom TCP protocols, Telegram Bot APIs, and REST APIs.
|
||||||||||||||||||||||
|
Threat Protected:
|
03 | |||||||||||||||||||||
|
Rule Set Type:
|
|
|||||||||||||||||||||
|
Class Type:
|
Trojan-activity | |||||||||||||||||||||
|
Kill Chain:
|
|
|||||||||||||||||||||
Known Exploited Vulnerabilities (Week 2 - April 2026)
For more information, please visit the Red Piranha Forum:
https://forum.redpiranha.net/t/known-exploited-vulnerabilities-catalog-2nd-week-of-april-2026/654.
|
Vulnerability
|
CVSS
|
Description | |
|
9.8
|
Unauthenticated RCE - Ivanti Endpoint Manager Mobile (EPMM) contains a command injection vulnerability that allows an unauthenticated remote attacker to execute operating system commands on the system.
|
Updated Malware Signature (Week 2 - April 2026)
|
Threat
|
Description | |
|
XWorm
|
A Remote Access Trojan (RAT) and malware loader that's commonly used in cyberattacks to give attackers full remote control over a victim's system. It's part of a growing trend of commercialised malware sold or rented on dark web forums, often under the guise of a “legitimate tool.”
|
Ransomware Report |
|
|
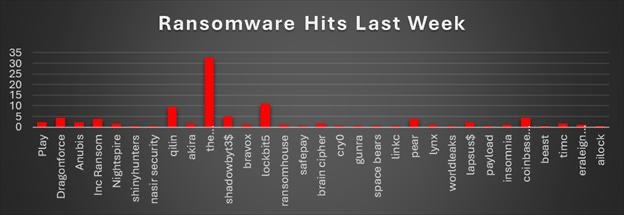
The Red Piranha Team conducts ongoing surveillance of the dark web and other channels to identify global organisations impacted by ransomware attacks. In the past week, our monitoring revealed multiple ransomware incidents across diverse threat groups, underscoring the persistent and widespread nature of these cyber risks. Presented below is a detailed breakdown of ransomware group activities during this period. Ransomware Hits Last WeekRansomware activity this week is dominated by The Gentlemen, accounting for 32.78% of all reported incidents and making it the single most aggressive operator by a wide margin. This is followed by LockBit 5 (11.11%) and Qilin (9.44%), both of which continue to demonstrate strong operational scale and consistency. Mid-tier activity includes ShadowBit3$ (5%), DragonForce (4.44%), and Coinbase Cartel (4.44%), along with INC Ransom (3.89%) and Pear (3.89%), showing a competitive second layer of active groups. Smaller but notable contributors include Play, Anubis, and Lapsus$ (each ~2.22%), while several groups such as NightSpire, Akira, Brain Cipher, and TIMC (~1.67%) maintain a steady but lower presence. The long tail consists of numerous low-frequency actors, like ShinyHunters, RansomHouse, SafePay, Cry0, Gunra, Space Bears, LinkC, WorldLeaks, Payload, Insomnia, Beast, ERALEIGN (APT73), and AILock (each ~0.56–1.11%), reinforcing the fragmented and decentralised nature of the ransomware ecosystem. |
Nasir Security
Nasir Security is not a ransomware operator; it is a pro-Iranian hacktivist and data-broker group conducting supply chain compromises and psychological operations against Middle Eastern and Israeli targets. The group's primary impact is propaganda: it compromises third-party contractors in the energy and critical infrastructure supply chain, exfiltrates documents from insecure cloud storage, then publishes heavily exaggerated breach claims on its data leak site to amplify perceived Iranian cyber capability during the ongoing Iran conflict.
The threat to organisations lies not in ransomware encryption but in supply chain compromise via business email compromise (BEC), spear phishing, and exploitation of insecure cloud storage at contractor organisations.
Threat Actor Description
A pro-Iranian hacktivist masquerading as a ransomware group, Nasir Security, emerged on 5 October 2025 with the registration of its data leak site domain nasir.cc (via Namecheap, 4 October 2025) and an initial attack claim against Taldor, a major Israeli IT services company. The group's first public statement declared itself as "Sons of Hezbollah Lebanon," vowing to avenge "the great warrior, Sayyed Hassan Nasrallah." Resecurity, the primary intelligence source on this actor, assesses that the group is "presumably associated with Iran" and likely comprises cyber-mercenaries hired or sponsored by Iran or its proxies rather than a formal state unit.
Targeting patterns and supply chain focus
Nasir Security targets organisations across two primary sectors: energy/oil and gas and government/critical infrastructure, exclusively in the Middle East and Israel. The geographic scope spans Israel, the UAE, Oman, Iraq, Saudi Arabia and Kuwait.
No confirmed RaaS affiliation; operates within broader pro-Iranian hacktivist ecosystem alongside Handala Hack and Fatimion.
Attack Lifecycle & TTPs
Nasir Security has extremely limited TTP documentation compared to established ransomware groups There is no evidence of ransomware encryption, lateral movement within victim networks, or deployment of persistence mechanisms beyond initial access to contractor accounts.
This sparse technical footprint is consistent with the group's nature: it relies on social engineering, Business Email Compromise, and exploitation of insecure third-party cloud services rather than custom malware or complex intrusion tooling.
|
ATT&CK ID
|
Technique Name
|
Tactic
|
Observed Behaviour
|
|
T1195
|
Supply Chain Compromise
|
Initial Access
|
Core operational strategy. Targets third-party contractors (engineering, safety, construction vendors) serving major energy companies rather than attacking primary targets directly
|
|
T1566
|
Phishing: Spearphishing
|
Initial Access
|
Conducts targeted BEC via spear phishing against contractor employees.
|
|
T1190 / T0819
|
Exploit Public-Facing Application
|
Initial Access
|
Exploitation of public-facing applications.
|
|
T1656
|
Impersonation
|
Execution
|
Uses impersonation as part of BEC and social engineering operations.
|
|
T1530
|
Data from Cloud Storage
|
Collection
|
Exfiltrates data from insecure cloud storage services used by contractor organisations.
|
Indicators of Compromise
|
IOC Type
|
Value
|
|
Domain
|
nasir.cc
|
|
Tor
|
yzcpwxuhbkyjnyn4qsf4o5dkvu6m2fyo7dwizmnlutanlmzlos7pa6qd[.]onion
|
|
Domain Expiry Date
|
2026-10-04T11:51:24Z
|
|
Registry Domain ID
|
206658540_DOMAIN_CC-VRSN
|
Mitigation via Red Piranha Crystal Eye 5.5
The Red Piranha Crystal Eye Extended Detection and Response (XDR) version 5.5 platform provides a sovereign-built, comprehensive defence architecture explicitly designed to neutralise advanced persistent threats (APTs). Operating on a Cybersecurity Mesh Architecture (CSMA), Crystal Eye 5.5 integrates on-premise gateways, cloud Virtual Private Clouds (VPCs), and remote workforce endpoints into a singular, cohesive security ecosystem. The following framework outlines specific mitigation strategies leveraging Crystal Eye 5.5 capabilities to defeat Nasir Security's TTPs.
- Microsoft Entra ID Single Sign-On (SSO) Integration
- Intrusion Detection and Prevention Systems (IDPS)
- Infrastructure Blacklisting
Worldwide Ransomware Victims
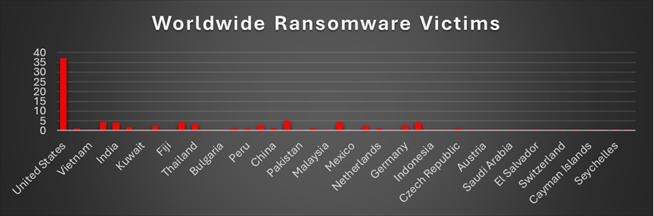
This week’s global ransomware distribution again shows a clear concentration in high-value economies with a wide global spread, led by the United States at 37.22%, maintaining its position as the primary target due to strong financial incentives and a large enterprise footprint. A second tier of consistently impacted countries includes the United Kingdom, France, Canada, and Italy (each ~4.44%), followed by Brazil (5%) and India (3.89%), indicating both developed and large emerging markets are being actively targeted.
Mid-level activity across Thailand (3.33%), Japan (2.78%), Germany (2.78%), and Spain and Taiwan (2.22%) highlights continued expansion into Asia-Pacific and Europe. Meanwhile, countries such as Australia (1.67%), along with several others across the Middle East, Africa, and Latin America (~1.11% and 0.56%), form a long tail of opportunistic targeting.
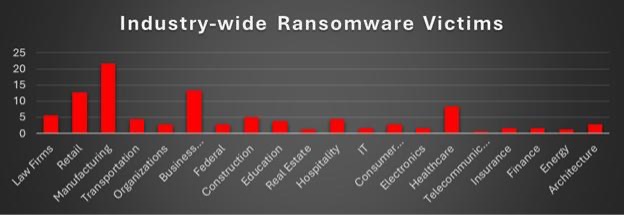
Industry-wide Ransomware Impact
This week’s industry-wise ransomware distribution clearly shows a heavy concentration on operationally critical and revenue-driven sectors, with Manufacturing leading at 21.67%, reinforcing its position as the most targeted industry due to its dependence on continuous operations and low tolerance for downtime. Business Services (13.33%) and Retail (12.78%) follow closely, indicating attackers are prioritising sectors with high transaction volumes and customer-facing services where disruption directly impacts revenue. Healthcare (8.33%) remains a significant target due to the sensitivity of data and urgency of service restoration, while Law Firms (5.56%) and Construction (5%) show consistent exposure due to valuable legal data and ongoing project dependencies.
Mid-tier activity is spread across Transportation (4.44%), Hospitality (4.44%), and Education (3.89%), reflecting a broad attack surface across service and infrastructure sectors. Smaller contributions from Federal (2.78%), Organisations (2.78%), Consumer Services (2.78%), and Architecture (2.78%) indicate steady but lower targeting, while industries such as IT, Finance, Insurance, Electronics (each ~1.67%), and niche sectors like Energy, Real Estate (~1.11%), and Telecommunications (0.56%) highlight opportunistic attacks.