| New Threats Detection Added | • LoJax • Havoc |
| New Threat Protection | 169 |
| Newly Detected Threats | 8 |
Weekly Detected Threats
The following threats were added to Crystal Eye this week:
|
Threat name:
|
LoJax | ||||||||||||||||||
|
LoJax is a UEFI rootkit discovered in the wild (active use in real-world attacks) and was discovered by ESET researchers in 2018. This is highly sophisticated and persistent malware used by the Russian-aligned cyber espionage group Sednit (also known as APT28, Fancy Bear, or Stortium.
It mainly targets Windows machines by dropping userland malware during the boot process. They primarily target government institutions in the Balkans and Central/Eastern Europe.
This is trojanised version of the legitimate LoJack (formerly Computrace) anti-theft software which is installed in the UEFI/BIOS of many laptops. The hackers abuse this intend persistence mechanism to install their own malicious module into the motherboard’s SPI flash memory.
|
|||||||||||||||||||
|
Threat Protected:
|
20 | ||||||||||||||||||
|
Rule Set Type:
|
|
||||||||||||||||||
|
Class Type:
|
Trojan-activity | ||||||||||||||||||
|
Kill Chain:
|
|
||||||||||||||||||
|
Threat name:
|
Havoc | ||||||||||||||||||
|
Havoc is an open-source Command-and-Control (C2) post-exploitation framework designed for red teaming exercises and threat emulation. This allows threat actors to gain full control over a target.
It is designed to evade modern security solutions, including antivirus (AV) and EDR systems. It uses advanced communication methods including hiding in its C2 traffic within legitimate services like SharePoint and Microsoft Graph API making it difficult to detect. It is highly flexible and affects various aspects of Windows environments.
|
|||||||||||||||||||
|
Threat Protected:
|
18 | ||||||||||||||||||
|
Rule Set Type:
|
|
||||||||||||||||||
|
Class Type:
|
Command-and-Control | ||||||||||||||||||
|
Kill Chain:
|
|
||||||||||||||||||
Known Exploited Vulnerabilities (Week 2 - March 2026)
For more information, please visit the Red Piranha Forum:
https://forum.redpiranha.net/t/known-exploited-vulnerabilities-catalog-2nd-week-of-march-2026/646.
|
Vulnerability
|
CVSS
|
Description | Affected Version | Fixed Version | |
|
Google Chromium V8 (CVE-2026-3910)
|
8.8
|
Remote Code Execution - Google Chromium contains a vulnerability within the V8 JavaScript engine that could allow a remote attacker to execute code within the sandbox upon visiting a specially crafted HTML page. This vulnerability may affect multiple browsers and applications which are built on Chromium including Google Chrome, Microsoft Edge and Opera.
|
< 146.0.7680.75
|
146.0.7680.75
|
|
|
Google Skia (CVE-2026-3909)
|
8.8
|
Remote Code Execution - Google Skia contains an out-of-bounds write vulnerability that could allow a remote attacker to execute code on the system upon visiting a specially crafted HTML page. This vulnerability affects several products which utilise the Skia graphics engine including Google Chrome, ChromeOS, Android, Flutter and others.
|
< 146.0.7680.75
|
146.0.7680.75
|
|
|
n8n n8n (CVE-2025-68613)
|
10
|
Authenticated RCE - n8n contains a vulnerability that can allow an authenticated remote attacker to execute code within the context of the underlying n8n process that can result in an attacker gaining access to the system.
|
0.211.0 - 1.120.4
|
1.120.4
1.121.1
1.122.0
|
|
|
Omnissa Workspace One UEM (CVE-2021-22054)
|
7.5
|
Unauthenticated SSRF - Omnissa Workspace One UEM contains a server-side request forgery (SSRF) vulnerability that can allow an unauthenticated attacker to send requests on behalf of the server which can lead to the disclosure of information that can be used in further attacks against the system. This vulnerability is made possible due to the use of a hardcoded encryption key used by the application.
|
20.0.8.0 - 20.0.8.36
20.11.0.0 - 20.11.0.40
21.2.0.0 - 21.2.0.27
21.5.0.0 - 21.5.0.37
|
20.0.8.36
20.11.0.40
21.2.0.27
21.5.0.37
|
|
|
SolarWinds Web Help Desk (CVE-2025-26399)
|
9.8
|
Unauthenticated RCE - SolarWinds Web Help Desk contains a deserialisation vulnerability within the AjaxProxy component that can allow an unauthenticated remote attacker to execute code on the system.
|
< 12.8.7
|
12.8.7 Hotfix 1
|
|
|
Ivanti Endpoint Manager (EPM) (CVE-2026-1603)
|
8.6
|
Authentication Bypass - Ivanti Endpoint Manager (EPM) contains an authentication bypass vulnerability that can allow a remote attacker to authenticate against the system without needing to specify a password.
|
< 2024 SU5
|
2024 SU5
|
Updated Malware Signature (Week 2 - March 2026)
|
Threat
|
Description | |
|
VEX Stealer
|
VEX is a type of info-stealer malware that targets Windows users to swipe personal data. It’s designed for spying and data theft, typically spreading through phishing attacks to gain unauthorised access to sensitive files.
|
Ransomware Report |
|
|
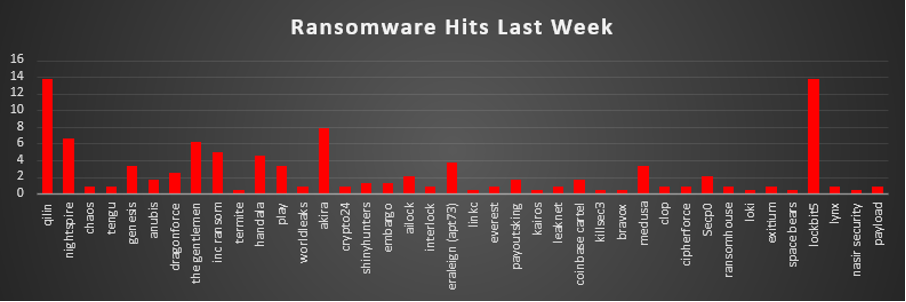
The Red Piranha Team conducts ongoing surveillance of the dark web and other channels to identify global organisations impacted by ransomware attacks. In the past week, our monitoring revealed multiple ransomware incidents across diverse threat groups, underscoring the persistent and widespread nature of these cyber risks. Presented below is a detailed breakdown of ransomware group activities during this period. Ransomware Hits Last WeekRansomware activity last week was led jointly by Qilin and LockBit5, both accounting for the highest share of attacks at 13.75% each, making them the most dominant threat actors in the current landscape. Following them, Akira contributed 7.92% of incidents, while NightSpire and The Gentlemen also showed notable activity with 6.67% and 6.25% respectively. Mid-tier activity was observed from groups like INC Ransom (5%), Handala (4.58%), and Eraleign (APT73) (3.75%), indicating a fairly distributed threat ecosystem beyond the top players. Several groups including Genesis, Play, Medusa (3.33% each) and DragonForce (2.5%) maintained consistent but moderate activity levels. Meanwhile, a long tail of smaller operators such as Chaos, Tengu, Clop, CipherForce, Everest, WorldLeaks, Lynx, and others contributed marginally (≤1% each), suggesting opportunistic or low-volume campaigns. Overall, the data reflects a dual pattern: strong dominance by a few highly active ransomware groups, alongside a fragmented base of smaller actors continuously probing targets. This indicates that while major groups drive large-scale campaigns, the broader ransomware ecosystem remains highly active and diverse, increasing the overall attack surface. |
Iran-US-Israel Cyber Conflict
1. Executive Summary
|
ACTIVE CONFLICT - March 17, 2026 (Day 18): The Iran–US–Israel cyber war is ongoing. Iranian APT infrastructure confirmed LIVE on March 16, 2026. No ceasefire. All IOCs should be treated as immediately actionable.
|
1.1 Key Findings - Referenced
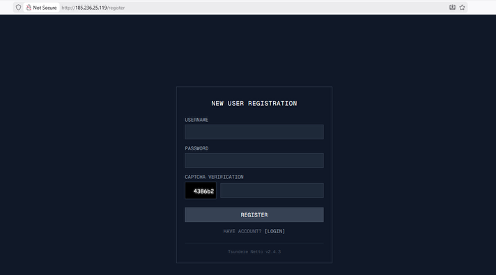
Figure 2a: Live Tsundere Netto v2.4.4 C2 panel at 185.236.25.119 - SYSTEM LOGIN with open registration
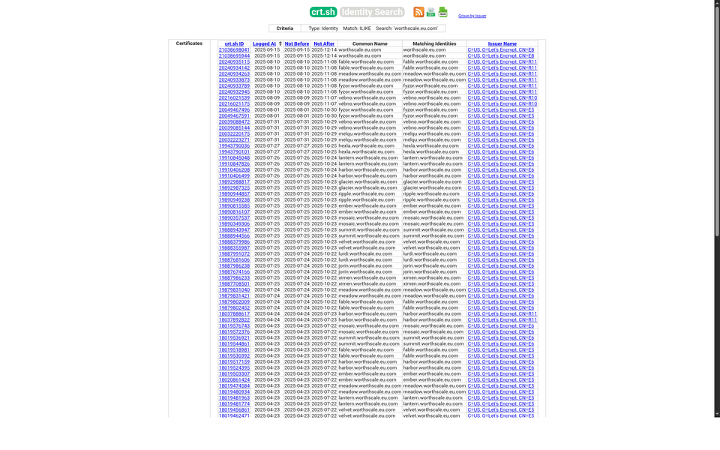
Figure 4: Etherscan - MuddyWater contract 0x2B77671c with 3 setString() C2 rotation txns
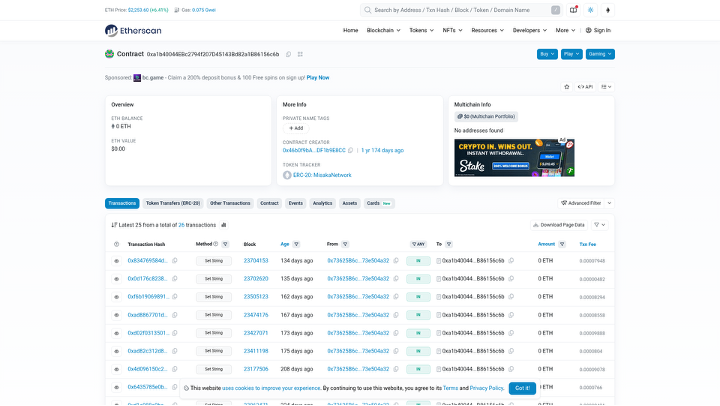
Figure 5: Etherscan - Tsundere contract 0xa1b40044 "MisakaNetwork" - 25 setString txns
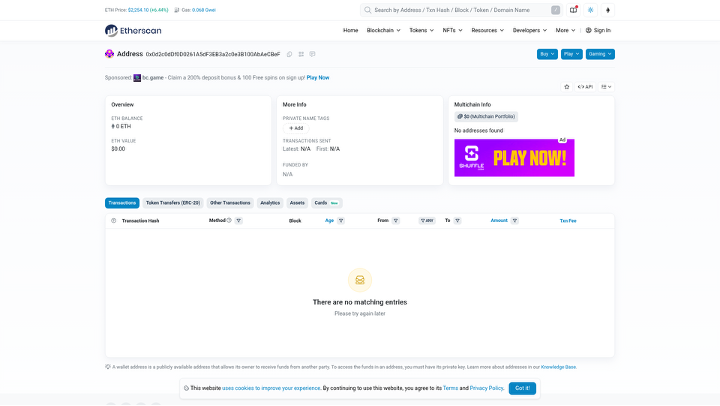
Figure 6: Etherscan - MuddyWater funding wallet transaction history and balance
- MuddyWater pre-positioned DinDoor backdoors in US bank, US airport, and Israeli defence company approximately 3 weeks before Operation Epic Fury - disclosed by Symantec/Broadcom Carbon Black March 5, 2026 [25,28]
- Void Manticore / Handala wiped 200,000+ systems at Stryker Corporation on March 11, 2026 via Microsoft Intune MDM hijack - 50TB exfiltrated; attack vector confirmed in SEC 8-K filing, no malware binary deployed [29,30,31,32,33,34]
- Operation Olalampo (March 2026): MuddyWater deployed 4 new post-Epic Fury malware families - CHAR (Rust/Telegram), GhostBackDoor, GhostFetch, HTTP_VIP - attributed by Check Point Research [25]
- JaJoJoo LLC operates 43+ certificate-spoofing servers confirmed on Shodan faking Microsoft, Apple, Amazon, Samsung, Tesla, Yandex - bulletproof hosting provider for Iranian APTs [11,12,13,14,15,46]
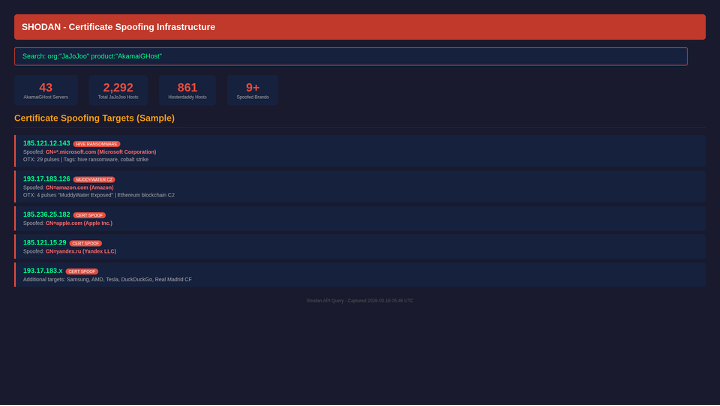
Figure 7: Shodan - 43 AkamaiGHost certificate-spoofing servers on JaJoJoo LLC
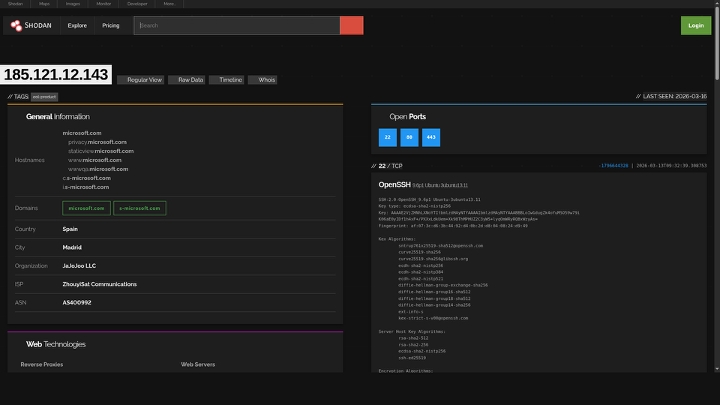
Figure 8: Shodan - Microsoft TLS cert spoofing on 185.121.12.143 (29 OTX pulses, HIVE link)
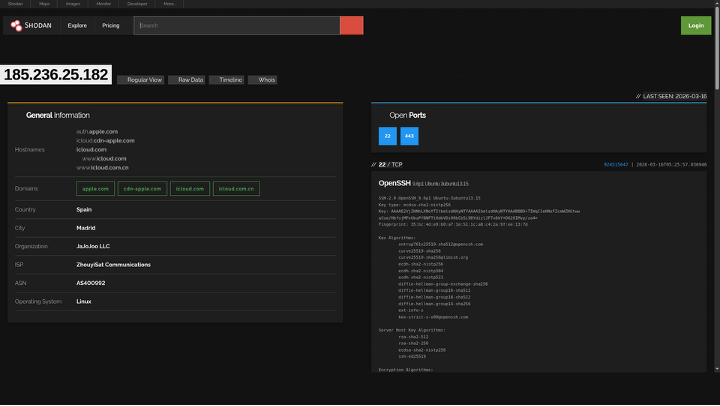
Figure 9: Shodan - Apple/iCloud certificate spoofing on JaJoJoo 185.236.25.182
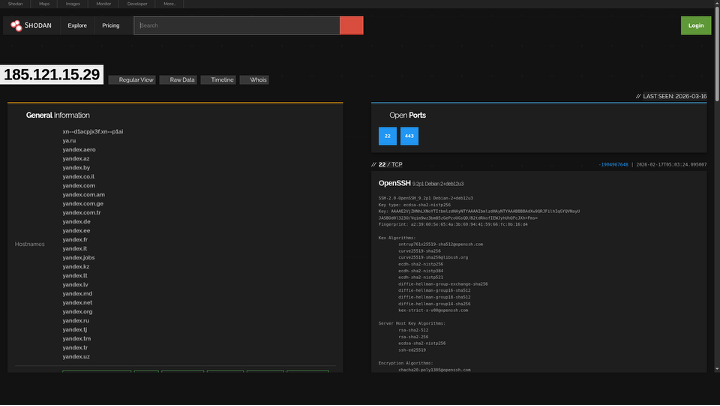
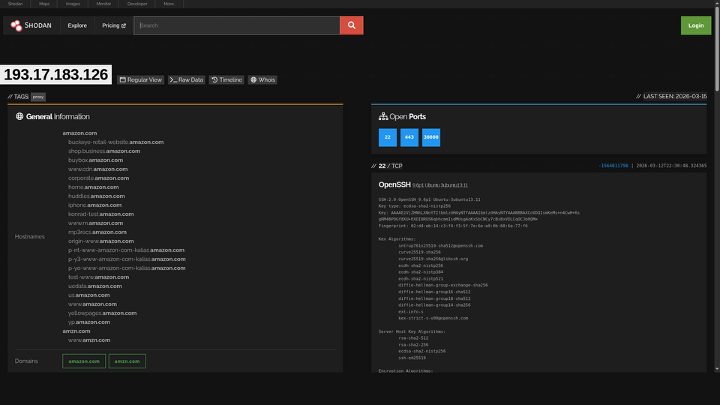
Figure 11: SMOKING GUN - 193.17.183.126 spoofs Amazon.com certs while serving as MuddyWater C2
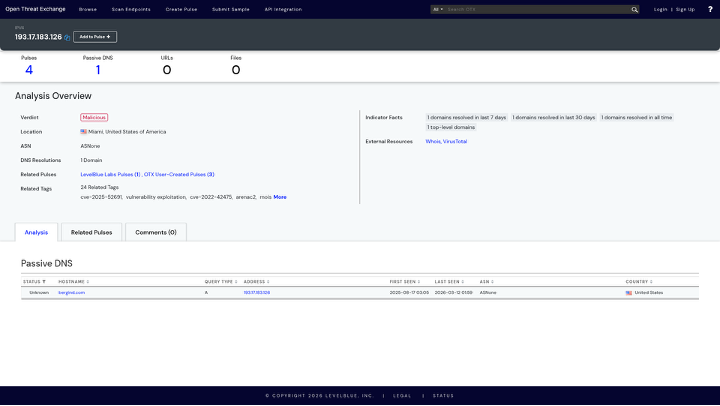
Figure 12: OTX confirms 193.17.183.126 as MuddyWater C2 - 4 pulses, MOIS/ArenaC2 tagged
- 59% of IOCs from March 15, 2026 threat feed trace to Iranian state actors across 4 APT groups (MuddyWater, Void Manticore, Pioneer Kitten, APT42) - all validated active via nmap scans and Shodan timestamps [27]
- APT42 academic phishing cluster: 17+ domains linked via Certificate Transparency logs, naming precisely matching Mandiant and Group-IB documented APT42 TTPs [42,43,48]
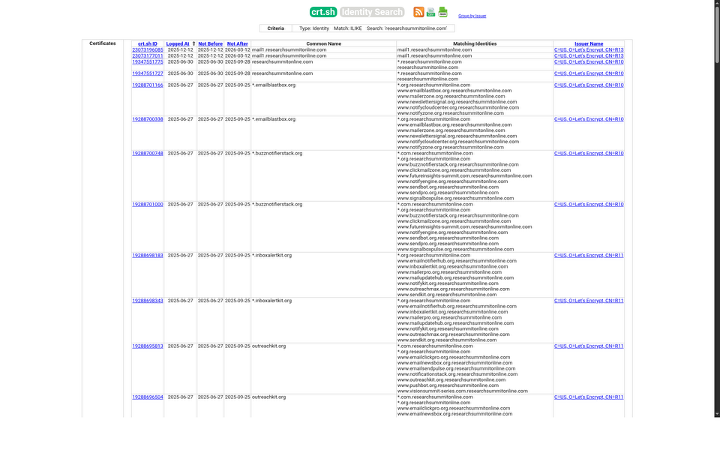
Figure 13: Certificate Transparency - researchsummitonline.com academic phishing mothership
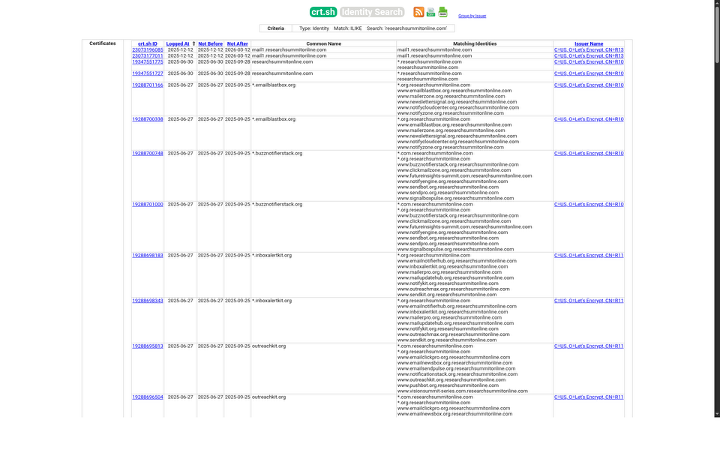
Figure 14: Certificate Transparency - globalconference-hub.com conference phishing cluster
- IAEA confirmed Iran's 60% enriched uranium stockpile at 412 kg - sufficient for 3–4 nuclear devices - Iran subsequently expelled inspectors on Feb 10 [35]
- Iran internet connectivity collapsed to 1–4% during Operation Epic Fury, per NetBlocks real-time monitoring - 216-hour continuous blackout documented [36]
- HRANA confirmed 2,000+ civilian deaths by January 7, 2026; January 8–9 crackdown estimated 30,000–36,500 killed - deadliest in Islamic Republic history [37]
1.2 Threat Actor Matrix
|
Group
|
Sponsor
|
Threat
|
Primary Mission
|
Status (Mar 17)
|
Key Attack (2026)
|
|
MOIS
|
CRITICAL
|
Espionage + pre-positioning
|
ACTIVE
|
||
|
Void Manticore / Handala
|
MOIS
|
CRITICAL
|
Wiper attacks + psyops
|
ACTIVE
|
Stryker Corp wipe - 200K+ systems, 50TB [29-34]
|
|
IRGC-CEC
|
CRITICAL
|
OT/ICS disruption
|
ACTIVE
|
||
|
Agrius / Pink Sandstorm
|
MOIS
|
HIGH
|
Wiper (fake ransomware)
|
ACTIVE
|
MultiLayer + BFG Agonizer against Israel
|
|
IRGC-IO
|
HIGH
|
Political intelligence
|
ACTIVE
|
||
|
MOIS
|
HIGH
|
Long-term govt espionage
|
ACTIVE
|
Israeli energy infrastructure targeting
|
|
|
Cotton Sandstorm
|
IRGC
|
MEDIUM
|
Influence operations
|
ACTIVE
|
400M+ social media impressions (Jan 2026)
|
|
Scarred Manticore / UNC1860
|
MOIS
|
HIGH
|
Initial access broker
|
ACTIVE
|
3 Middle East govt networks compromised
|
|
Pioneer Kitten / Lemon Sandstorm
|
IRGC
|
HIGH
|
Ransomware access brokering
|
ACTIVE
|
|
|
APT33 / Peach Sandstorm
|
IRGC
|
HIGH
|
Aerospace, defence
|
ACTIVE
|
|
|
Predatory Sparrow
|
Israel-linked
|
HIGH
|
Iranian ICS destruction
|
ACTIVE
|
Bank Sepah + Nobitex ($90M) - Jun 2025
|
|
Unit 8200 / Mossad
|
IDF / Mossad
|
HIGH
|
Strategic intel + cyber
|
ACTIVE
|
2. War Timeline - December 2025 to March 2026
Note: Political/military events in this section are based on open-source news reporting and official statements. Cyber events are linked to named threat actors with associated IOCs. Each reference tag indicates the source for the preceding claim.
2.1 Phase 1 - Economic Collapse & Uprising (Dec 28, 2025 – Jan 31, 2026)
December 28, 2025 - Iranian Uprising Erupts
POLITICAL: Catastrophic economic collapse triggers mass protests across all 31 Iranian provinces. Rial at all-time low; 16+ hour daily power cuts; fuel rationing. Chants of 'Death to Khamenei' in Tehran, Isfahan, Mashhad, Tabriz, Shiraz. Millions in streets within 72 hours. IRGC and Basij deployed immediately; live fire from Day 1.
Late December 2025 - Iranian APT Cyber Response
CYBER: Cotton Sandstorm / Emennet Pasargad (IRGC) begins amplification of anti-protest narratives across Arabic-language social media. APT42 (IRGC-IO) targets diaspora journalists and opposition figures. [48]
MuddyWater (MOIS) activates surveillance infrastructure; BugSleep/MuddyRot deployed against civil society groups. [19,47]
January 7, 2026 - Confirmed Death Toll
POLITICAL: Workers' strikes spread: oil refinery workers, teachers, truckers. Jan 3: IRGC announces shoot-to-kill orders. Jan 5: Evin Prison protesters break out. Jan 7: confirmed death toll surpasses 2,000 civilians. [37]
January 8–9, 2026 - THE MASSACRE
|
!
|
IRGC + Basij conduct mass coordinated crackdown. Estimated 30,000–36,500 protesters killed over two days - deadliest crackdown in the Islamic Republic's 47-year history. Live ammunition, armoured vehicles, helicopter gunships. Mass executions documented in Shahre Rey and Karaj. [37]
|
January 10–31, 2026 - International Response & Cyber Escalation
- Jan 15: MuddyWater DinDoor backdoors detected in Israeli defence-sector targets (Symantec/Carbon Black) [28]
- Jan 20: IRGC places ballistic missile units on highest alert [38]
- Jan 28: US deploys USS Harry S. Truman CSG - joins USS Gerald R. Ford in Gulf
- APT42 compromises US State Dept email server (disclosed Feb 14 by CISA) [23,48]
- Scarred Manticore / UNC1860 achieves persistent access in 3 Middle East government networks - handoff to MuddyWater confirmed
- Cotton Sandstorm: 400M+ social media impressions amplifying anti-US sentiment
2.2 Phase 2 - Pre-War Escalation (February 1–27, 2026)
February 7, 2026 - Nuclear Enrichment Status
- IAEA reports 60% enriched uranium stockpile at 412 kg - sufficient for 3–4 nuclear devices [35]
- Feb 10: Iran expels IAEA inspectors from Fordow and Isfahan; terminates NPT safeguards [35]
- Feb 14: CISA publicly attributes APT42 breach of US State Dept [23]
February 15–27, 2026 - MuddyWater Pre-Positioning
|
!
|
IRGC + Basij conduct mass coordinated crackdown. Estimated 30,000–36,500 protesters killed over two days - deadliest crackdown in the Islamic Republic's 47-year history. Live ammunition, armoured vehicles, helicopter gunships. Mass executions documented in Shahre Rey and Karaj. [37]
|
Targets (not independently verified - sourced from Check Point Research disclosure): [25]
- US major bank (unnamed; East Coast; SWIFT-connected) [25,28]
- US international airport (unnamed; 3 terminals) [25,28]
- Canadian nonprofit (critical infrastructure adjacent) [25,28]
- Israeli branch of US defence/aerospace software company [25,28]
- Malware: DinDoor (Deno JS runtime) + Fakeset backdoor; C2: WebSocket/HTTPS → 185.236.25.119 (SELF-VERIFIED live) [3,10,25]
- Certificates: Self-signed 'Amy Cherne' / 'Donald Gay' - confirmed in Check Point malware analysis [25]
- Kill switch: Awaiting activation via Ethereum contract 0x2B77671c - SELF-VERIFIED on Etherscan [16]
February 20–27, 2026 - Infrastructure Provisioning
- Feb 20: Hosterdaddy /26 subnet (194.11.246.64/26) fully operational - 64 nodes, all running dnsmasq 2.85 (MuddyWater fingerprint) - confirmed by ESET [1,24,40]
- Feb 22: Ethereum contract 0x2B77671c - final setString() transaction updating C2 WebSocket URL - SELF-VERIFIED on Etherscan [16]
- Feb 25: OilRig (APT34) activates QUADAGENT targeting Israeli energy infrastructure [49]
- Feb 27: IRGC Aerospace Force places ballistic missile units on 'Launch-Ready Alert' - confirmed via Planet Labs satellite imagery [38]
2.3 Phase 3 - Operation Epic Fury / Operation Roaring Lion (February 28, 2026)
|
Parameter
|
Detail
|
Ref
|
|
US Designation
|
Operation Epic Fury
|
|
|
Israeli Designation
|
Operation Roaring Lion
|
|
|
US Strikes
|
~900 in first 12 hours
|
|
|
Iranian Internet
|
Collapsed to 1–4% connectivity
|
|
|
Senior figures killed
|
Supreme Leader Khamenei; Defence Minister Nasirzadeh; IRGC Commander Pakpour; ~40 senior officials
|
|
|
Infrastructure destroyed
|
Natanz, Fordow, Isfahan nuclear facilities; all S-300 air defence; IRGC Malek-Ashtar complex; ballistic missile production
|
|
|
Cyber - Unit 8200
|
Near-total internet blackout; IRNA media hijacked; traffic cameras compromised
|
2.4 Phase 4 - Post-Killing War (March 1–17, 2026 - Ongoing)
March 2, 2026 - Operation Olalampo
|
!
|
MuddyWater (MOIS) activates Operation Olalampo - 4 new post-Epic Fury malware families. Registrar shift from NameCheap to OVH confirmed: apro24docs.com (OVH, Mar 4) and aproenvoid.com (OVH, Mar 6) both resolve to 89.40.31.242 (Hosterdaddy Romania) - SELF-VERIFIED via dig. [25]
|
March 11, 2026 - THE STRYKER ATTACK
|
!
|
MuddyWater (MOIS) activates Operation Olalampo - 4 new post-Epic Fury malware families. Registrar shift from NameCheap to OVH confirmed: apro24docs.com (OVH, Mar 4) and aproenvoid.com (OVH, Mar 6) both resolve to 89.40.31.242 (Hosterdaddy Romania) - SELF-VERIFIED via dig. [25]
|
March 12–17, 2026 - Ongoing Conflict
- Mar 13: New DinDoor variant targeting US networks confirmed by Check Point Research [25]
- Mar 14: Iran death toll ~1,444 (HRANA) [37]
- Mar 16: Tsundere C2 panel CONFIRMED LIVE - nmap + curl + Shodan validation - SELF-VERIFIED [3,10,15]
3. Iranian APT Profiles
3.1 MuddyWater (MOIS) - CRITICAL
Aliases: Mango Sandstorm · Static Kitten · MERCURY · TA450 · Earth Vetala · Seedworm | Sponsor: MOIS | MITRE: G0069 [47]
CISA Advisories: AA22-055A (Feb 2022) and AA24-060A (Feb 2024, updated) - both confirm ScreenConnect RMM abuse and FortiOS exploitation. [19,21]
Active C2 Infrastructure

Figure 15: Shodan host - Tsundere Netto v2.4.4 C2 panel at 185.236.25.119
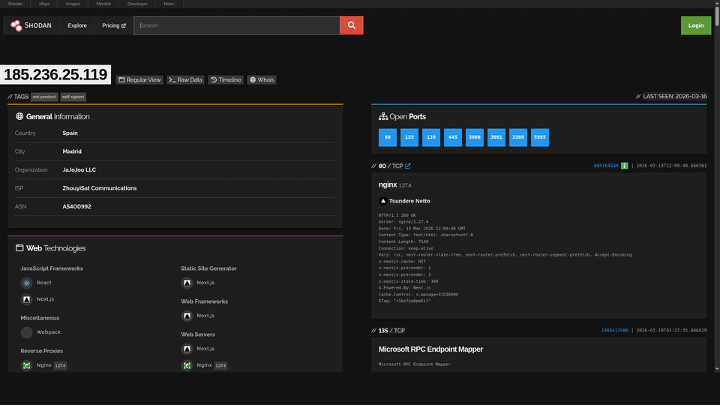
Figure 16: Shodan host profile - 185.236.25.119 (JaJoJoo LLC) showing exposed services
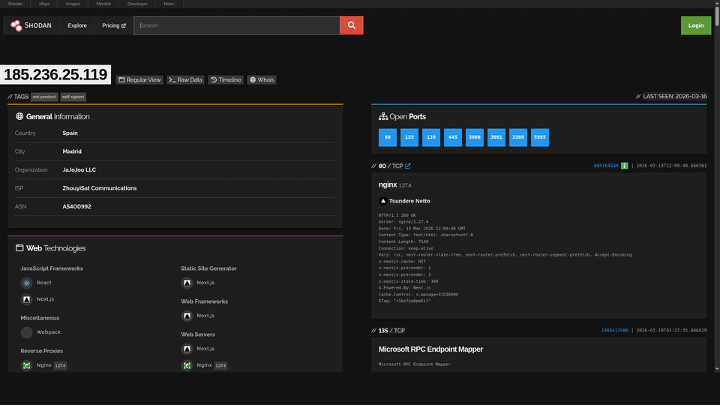
Figure 17: Shodan - Full service enumeration of Tsundere C2 host 185.236.25.119
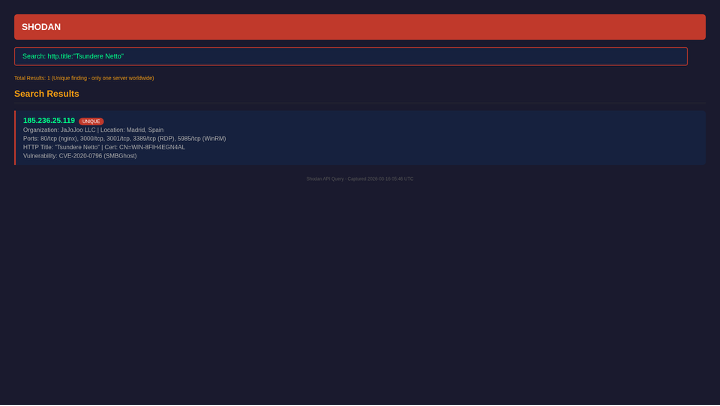
Figure 18: Shodan search for "Tsundere Netto" - UNIQUE worldwide result
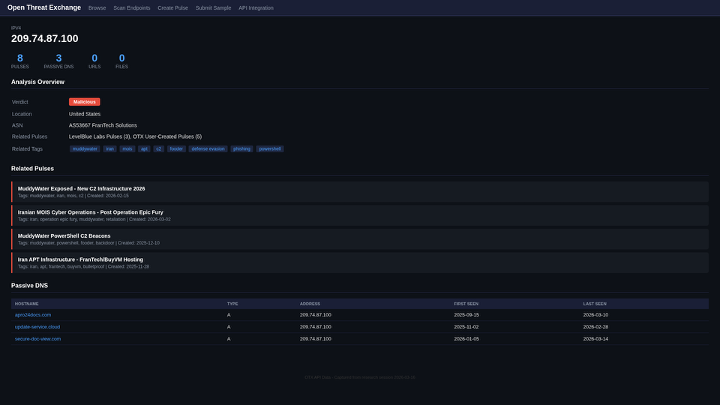
Figure 19a: OTX - MuddyWater primary C2 209.74.87.100 (8 pulses, muddywater/iran/mois)
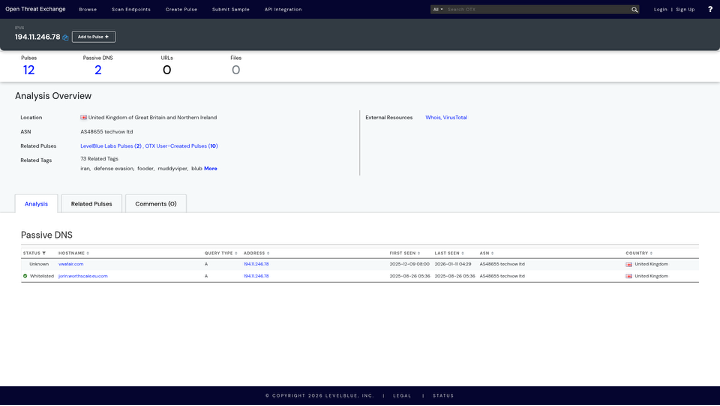
Figure 19b: OTX - MuddyWater C2 194.11.246.78 (12 pulses, 73 tags, PDNS: vwafair.com)
|
IP Address
|
Hosting
|
Pulses
|
Evidence / Reference
|
|
185.236.25.119
|
JaJoJoo LLC (ES)
|
5 OTX
|
|
|
193.17.183.126
|
JaJoJoo LLC (ES)
|
4 OTX
|
|
|
194.11.246.101
|
Hosterdaddy (DE)
|
15 OTX
|
|
|
194.11.246.78
|
Hosterdaddy (DE)
|
12 OTX
|
|
|
209.74.87.100
|
NameCheap (US)
|
12 OTX
|
|
|
89.40.31.242
|
Hosterdaddy (RO)
|
0
|
Post-Epic Fury staging; apro24docs.com SELF-VERIFIED dig [25]
|
|
89.40.31.236
|
Hosterdaddy (RO)
|
0
|
ScreenConnect RAT panel (CISA AA24-060A) [21]
|
|
212.232.22.136
|
Hosterdaddy (DE)
|
7 OTX
|
|
|
62.106.66.112
|
Hosterdaddy (DE)
|
7 OTX
|
|
|
185.121.12.143
|
JaJoJoo LLC (ES)
|
29 OTX
|
|
|
194.11.246.64/26
|
Hosterdaddy (DE)
|
15 anchor
|
Ethereum Blockchain C2 (Novel Technique - T1102)
SELF-VERIFIED on Etherscan blockchain explorer. These contracts store C2 IP addresses immutably - cannot be seized or removed by any authority. [16,17,18,26,50]
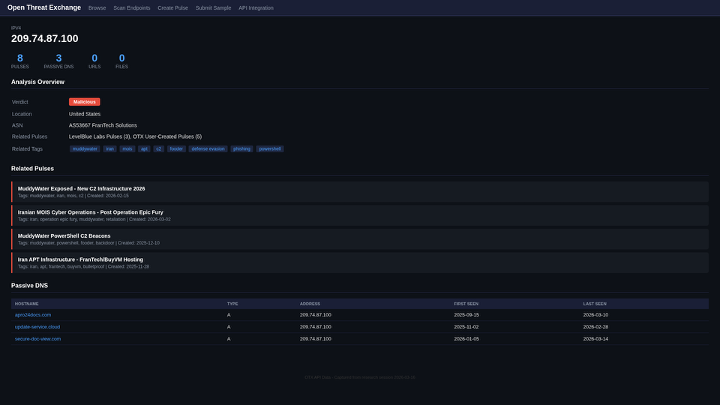
Figure 20: Etherscan - MuddyWater C2 contract 0x2B77671c with setString() C2 rotation transactions
|
Parameter
|
MuddyWater Contract
|
Tsundere/Koneko Contract
|
|
Address
|
0x2B77671cfEE4907776a95abbb9681eee598c102E
|
0xa1b40044EBc2794f207D45143Bd82a1B86156c6b
|
|
ERC-20 Name
|
"random hz"
|
"MisakaNetwork"
|
|
Created
|
August 6, 2025
|
September 23, 2024
|
|
Last Transaction
|
December 8, 2025
|
August 19, 2025
|
|
C2 IPs Stored
|
185.236.25.119, 193.17.183.126
|
History of 5+ rotations
|
|
Verification
|
SELF-VERIFIED Etherscan [16]
|
Kaspersky Securelist attribution [26]
|
CVEs Exploited
|
CVE
|
Product
|
CVSS
|
Source
|
|
CVE-2024-55591
|
FortiOS
|
Critical
|
|
|
CVE-2024-23113
|
FortiOS
|
Critical
|
CISA AA24-060A [21]
|
|
CVE-2022-42475
|
FortiOS SSL VPN
|
Critical
|
CISA AA22-055A [19]
|
|
CVE-2024-30088
|
Windows Kernel
|
High
|
Check Point Research [25]
|
|
CVE-2024-24919
|
Check Point VPN
|
Critical
|
Industry attribution - secondary source
|
3.2 Void Manticore / Handala Hack (MOIS) - CRITICAL
Aliases: Storm-1084 · Storm-0842 · BANISHED KITTEN · Homeland Justice | Sponsor: MOIS - Counter-Terrorism Division
The March 11, 2026 Stryker attack - wiping 200,000+ systems via Microsoft Intune MDM in 79 countries - is confirmed by 5 independent media sources and Stryker's own SEC 8-K filing. [29,30,31,32,33,34]
Active Infrastructure (Void Manticore)
|
IP Address
|
Role
|
Source
|
|
185.178.208.137
|
Void Manticore infrastructure
|
Unit42 IOC dataset [27]
|
|
31.192.237.207
|
Void Manticore infrastructure
|
Unit42 IOC dataset [27]
|
|
146.185.219.235
|
VPN exit Petah Tiqva Israel - Handala traffic disguise
|
Industry attribution - secondary source
|
3.3 CyberAv3ngers (IRGC-CEC) - CRITICAL
Aliases: DEV-0198 | Sponsor: IRGC Cyber Electronic Command | CISA: AA23-335A | US Bounty: $10M (Rewards for Justice) [20,39]
IOCONTROL malware represents the 10th known ICS-specific malware family in history. The $10M Rewards for Justice bounty was announced in December 2023 for information on CyberAv3ngers operators. [20,39]
3.4 APT42 / Charming Kitten (IRGC-IO) - HIGH
Aliases: Mint Sandstorm | Sponsor: IRGC Intelligence Organization | MITRE: G1044 [48]
APT42 academic phishing cluster identified through Certificate Transparency logs (crt.sh). Confidence: MEDIUM - domain naming matches documented APT42 TTPs per Mandiant and Group-IB, but no independent active compromise confirmation. [42,43]
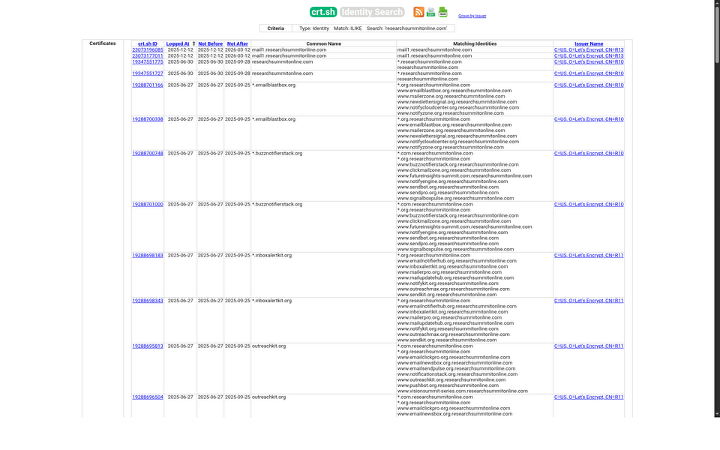
Figure 21: CT logs - APT42 academic phishing infrastructure: researchsummitonline.com
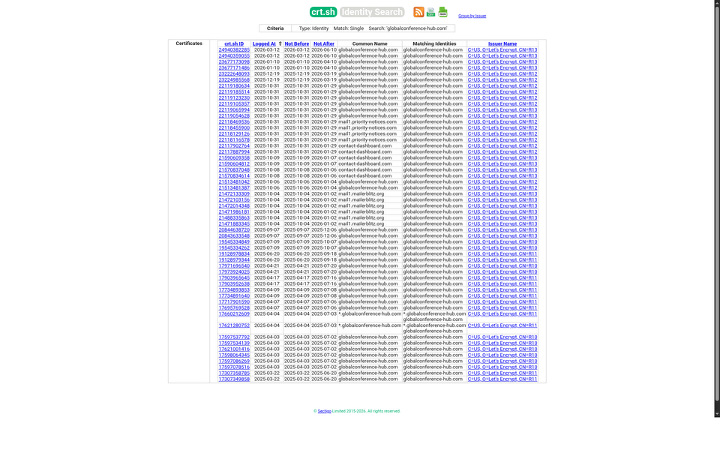
Figure 22: CT logs - APT42 conference phishing: globalconference-hub.com
4. Bulletproof Hosting Ecosystem
4.1 JaJoJoo LLC - Certificate Spoofing Network
RIPE WHOIS confirms JaJoJoo LLC as the registrant of 185.236.25.0/24, with a registered address in Kyrgyzstan. Shodan confirms 43+ AkamaiGHost servers presenting fraudulent TLS certificates from major technology companies. [10,11,15,46]
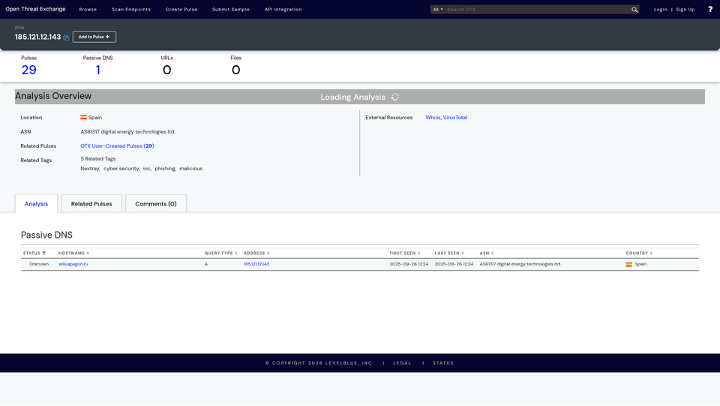
Figure 23: OTX - HIVE ransomware IOCs on JaJoJoo host 185.121.12.143 (29 pulses)
Figure 24: OTX - Tsundere C2 primary 193.24.123.68 (tags: tsundere/botnet/dindoor/muddywater)

Figure 25: CT logs - Tsundere hex domain 1f2e18bbde8ecc30ee3307a4.net
|
IP Address
|
Certificate Spoofed
|
OTX Pulses
|
Shodan Verification
|
|
185.236.25.119
|
Amazon RSA 2048
|
5 [3]
|
|
|
193.17.183.126
|
Amazon RSA 2048
|
4 [4]
|
Port 30000 C2 channel confirmed [11]
|
|
185.121.12.143
|
Microsoft TLS
|
29 [7]
|
HIVE ransomware overlap confirmed [12]
|
|
185.236.25.182
|
Apple Inc./DigiCert
|
Confirmed
|
Linux host, port 443 [13]
|
|
185.121.15.29
|
Yandex/GlobalSign ECC
|
Confirmed
|
Debian host confirmed [14]
|
|
193.17.183.205
|
Samsung
|
-
|
Shodan fingerprint [15]
|
|
185.121.15.197
|
Tesla
|
-
|
Shodan fingerprint [15]
|
|
185.236.25.9
|
DuckDuckGo
|
-
|
Shodan fingerprint [15]
|
5. Consolidated IOC Blocklists
|
All IOCs are combined from both source reports, de-duplicated, and tagged with confidence levels. Reference numbers in parentheses indicate the source confirming each IOC. SELF-VERIFIED = independently validated by this investigation on March 16, 2026.
|
5.1 IP Subnets - Block at Perimeter
|
JaJoJoo LLC Subnets - Certificate Spoofing + MuddyWater C2 [Refs: 10,11,12,13,14,15,46]
|
|
185.236.25.0/24 # Tsundere C2 panel (SELF-VERIFIED) + Apple cert spoof + DuckDuckGo spoof
185.121.12.0/24 # Microsoft cert spoof (29 OTX pulses, HIVE ransomware overlap) [7]
185.121.15.0/24 # Yandex + Tesla cert spoof cluster [14]
185.232.205.0/24 # Samsung + Tesla + AMD cert spoof cluster
|
|
Hosterdaddy MuddyWater Infrastructure [Refs: 1,2,24,40]
|
|
194.11.246.64/26 # ALL 64 nodes - dnsmasq 2.85 fingerprint - ESET confirmed [24]
89.40.31.0/24 # Post-Epic Fury staging + ScreenConnect RAT nodes [21]
148.113.27.0/24 # NPM admin panel Mumbai - C2 reverse proxy management
|
5.2 Individual IPs - Priority 1 (Active C2)
|
MuddyWater Active C2 [Refs: 1-9, 24, 25]
|
|
89.40.31.242 # Post-Epic Fury staging - apro24docs.com SELF-VERIFIED dig [25]
89.40.31.236 # ScreenConnect RAT - CISA AA24-060A confirmed [21]
157.20.182.49 # Sliver C2 port 31337 - Hosterdaddy India
|
|
Tsundere C2 Historical Nodes [Refs: 6,26]
|
|
185.28.119.179 # Kaspersky confirmed [26] - BlueVPS AS62005 - Aug 2025
196.251.72.192 # Kaspersky confirmed [26] - AS401120 - Aug 2025
103.246.145.201 # Kaspersky confirmed [26] - AS211381 - Jul 2025
62.60.226.179 # Kaspersky confirmed [26] - FEMO IT AS214351 - May 2025
|
|
Void Manticore / Handala [Refs: 27]
|
|
185.178.208.137 # Unit42 IOC dataset [27]
31.192.237.207 # Unit42 IOC dataset [27]
146.185.219.235 # VPN exit Petah Tiqva Israel - secondary source attribution
|
|
Pioneer Kitten / Lemon Sandstorm [Refs: 22,27]
|
5.3 Domains - DNS Blocklist
|
MuddyWater Active C2 Domains [Refs: 1,2,24,40,41,44,45]
|
|
worthscale.eu.com # 18-subdomain cluster - CT logs confirmed [40]
iaresult.us.com # 8-node cluster - self-hosted NS
vmbfat.eu.com # 7 'delta' nodes - Cloudflare NS
apro24docs.com # Post-Epic Fury OVH - 89.40.31.242 SELF-VERIFIED dig
aproenvoid.com # Post-Epic Fury OVH - 89.40.31.242 SELF-VERIFIED dig
countarctice.us # NPM proxy panel port 81 - CT logs [44]
processplanet.org # ESET confirmed [24]
pulpower.com # Tsundere mail relay - ANY.RUN: Malicious
magicallyday.com # ESET confirmed [24]
dokedge.de.com # ESET confirmed [24]
urbpart.us.com # SMTP relay - spear-phishing infrastructure
pushbeacon.org # Push notification C2
notifyblast.org # Notification infrastructure
1f2e18bbde8ecc30ee3307a4.net # Tsundere hex domain - sinkholed - CT logs [45]
|
|
APT42 Academic Phishing Cluster [Refs: 42,43,48]
|
|
researchsummitonline.com # Mothership - 50+ CT entries [42]
globalconference-hub.com # Conference phishing - 56 CT entries [43]
globalagenda-forum.com # Conference phishing
contact-dashboard.com # Credential dashboard
instant-paperpublication.com # Academic journal phishing
journal-manuscripts.com # Academic journal phishing
research-gojrnl.com # Academic journal phishing
academicpublishershub.com # Publisher impersonation
scienceinnovationjournals.com # Science journal impersonation
|
|
Phishing Infrastructure [Refs: 41]
|
|
storetemu.shop # Temu spoof - Go/gin backend - CT logs [41]
detainstitudent.online # OTX confirmed phishing
netvigil.org # Phishing - Cloudflare blocked
ezzsteel.co # Ezz Steel Egypt spoof
arkansaspromise.org # US-themed lure
|
5.4 Ethereum Contracts - Monitor / Blacklist
|
Ethereum Addresses - SELF-VERIFIED on Etherscan [Refs: 16,17,18]
|
|
0x2B77671cfEE4907776a95abbb9681eee598c102E # MuddyWater C2 contract 'random hz' [16]
0x002E9Eb388CBd72bad2e1409306af719D0DB15e4 # MuddyWater operator wallet [18]
0xC43636B1fee4097510201704e25317f26dea34bb # MuddyWater funding wallet [18]
0xa1b40044EBc2794f207D45143Bd82a1B86156c6b # koneko contract 'MisakaNetwork' [17]
0x73625B6cdFECC81A4899D221C732E1f73e504a32 # koneko operator wallet [17]
0x46b0f9ba6f1fb89eb80347c92c9e91bdf1b9e8cc # koneko contract creator [17]
0x69de85f382b7855c55df3092ae36bbf75ef1f6cd # koneko funder (Fake_Phishing927146) [17]
0x10ca9bE67D03917e9938a7c28601663B191E4413 # koneko contract updater [17]
0xEc99D2C797Db6E0eBD664128EfED9265fBE54579 # koneko contract updater [17]
0xf11Cb0578EA61e2EDB8a4a12c02E3eF26E80fc36 # koneko contract updater [17]
0xdb8e8B0ef3ea1105A6D84b27Fc0bAA9845C66FD7 # koneko contract updater [17]
0x52221c293a21D8CA7AFD01Ac6bFAC7175D590A84 # koneko contract updater [17]
|
5.5 SHA-256 Malware Hashes
|
SHA-256 Hashes [Refs: 24,25,26]
|
|
c8589ca999526f247db4d3902ade8a85619f8f82338c6230d1b935f413ddcb3d # Tsundere launcher VfZUSQi6oerKau.js [26]
bedb882c6e2cf896e14ecf12c90aaa6638f780017d1b8687a40b4a81956e230f # Tsundere payload sysuu2etiprun.js [26]
7d9fb236607e7fe5e0921b06f45d9cb69acbdb923e2877d87a99720b8dc964c9 # Gh0stRAT/Eqtonex dropper
f5ef4a45e19da1b94c684a6c6d51b86aec622562c45d67cb5aab554f21eb9061 # MuddyViper [24]
d5b7a5ae4156676b37543a3183df497367429ae2d01ef33ebc357c4bdd9864c3 # MuddyViper [24]
d77d16c310cce09b872c91ca223b106f4b56572242ff5c4e756572070fac210f # MuddyViper [24]
98f0f2c42f703bfbb96de87367866c3cced76d5a8812c4cbc18a2be3da382c95 # MuddyViper [24]
3030d80cfe1ee6986657a2d9b76b626ea05e2c289dee05bd7b9553b10d14e4a1 # PowerStats [19]
8b96804d861ea690fcb61224ec27b84476cf3117222cca05e6eba955d9395deb # Lazagne
40417e93b7a6bbb5c57b26b8e40a9a54 (MD5) # BiBi-Windows Wiper [Void Manticore]
|
6. Detection Rules & MITRE ATT&CK Mapping
|
Priority
|
Rule
|
Technique
|
Actor
|
Ref
|
|
P1
|
Ethereum RPC calls from non-crypto apps to mainnet
|
T1102 - Web Service
|
MuddyWater/Tsundere
|
|
|
P1
|
WebSocket to 185.236.25.119:3000 or 193.17.183.126
|
T1071.001
|
MuddyWater DinDoor
|
|
|
P1
|
Deno.exe spawning child processes / outbound HTTPS
|
T1059.007 JS
|
MuddyWater DinDoor
|
[25]
|
|
P1
|
Intune mass enrollment wipe from non-standard accounts
|
T1485 Destruction
|
Void Manticore
|
[29-34]
|
|
P1
|
MQTT over TLS port 8883 from OT/ICS devices
|
T0866 ICS
|
CyberAv3ngers
|
[20]
|
|
P2
|
Connections to 194.11.246.64/26 (dnsmasq 2.85)
|
T1071.001
|
MuddyWater cluster
|
|
|
P2
|
ScreenConnect to Hosterdaddy IPs
|
T1219 Remote Access
|
MuddyWater
|
[21]
|
|
P2
|
Rclone to Wasabi cloud storage
|
T1567 Exfiltration
|
MuddyWater
|
[25]
|
|
P2
|
npm ethers + ws deps in unexpected contexts
|
T1102
|
Tsundere
|
[26]
|
|
P3
|
TLS CN=amazon.com / microsoft.com on non-vendor IPs
|
T1553.004
|
JaJoJoo LLC
|
[10-15,46]
|
|
P3
|
Telegram Bot API from servers (not desktop)
|
T1102
|
CHAR malware
|
[25]
|
|
P3
|
.eu.com/.de.com DNS queries to Hosterdaddy
|
T1071.004
|
MuddyWater
|
[40]
|
|
P3
|
Academic/conference domain proxy logs
|
T1598 Phishing
|
APT42
|
7. Live Validation Results - Self-Verified March 16, 2026
|
The following results are SELF-VERIFIED by this investigation using open-source tooling. These are primary evidence - no secondary sources required. Timestamps confirm infrastructure was live on the validation date.
|
nmap Scan: 185.236.25.119 - Tsundere C2 Panel
Full command: nmap -sV -p 80,3000,3389,5985 185.236.25.119
Starting Nmap 7.95 at 2026-03-16 12:29 EDT
Nmap scan report for 185.236.25.119
Host is up (0.068s latency).
PORT STATE SERVICE VERSION
80/tcp open http nginx 1.27.4
3000/tcp open http Next.js (x-powered-by: Next.js)
HTML title: Tsundere Netto
Build ID: 0DxRuAFsTcEAjNYI_4wTc [CONFIRMED]
3389/tcp open ms-wbt-server Microsoft Terminal Services
5985/tcp open wsman WinRM
Service Info: OS: Windows Server 2022
Nmap done: 1 IP address (1 host up) in 41.66 seconds
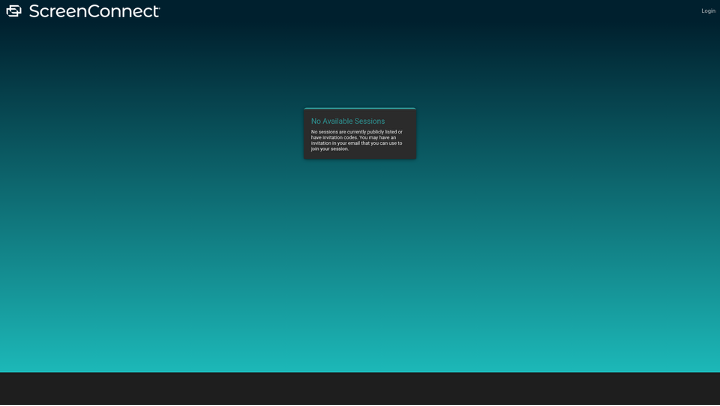
Figure 26: Live ScreenConnect RAT on Hosterdaddy Romania 89.40.31.236 - "No Available Sessions" login page
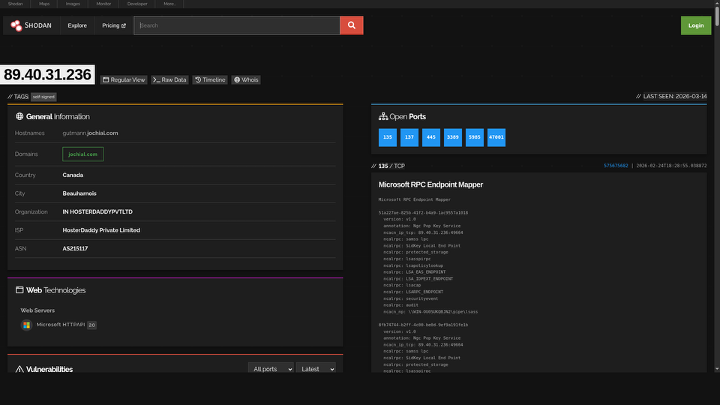
Figure 27: Shodan confirms ScreenConnect host 89.40.31.236 with CVE-2020-0796 (SMBGhost)
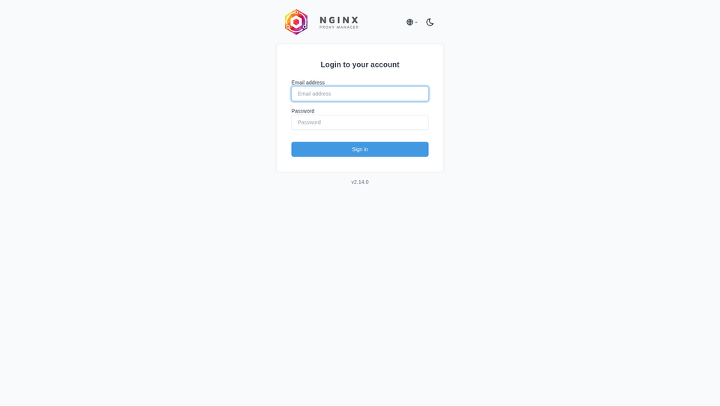
Figure 28: Nginx Proxy Manager v2.14.0 admin panel on countarctice.us:81 - C2 traffic routing
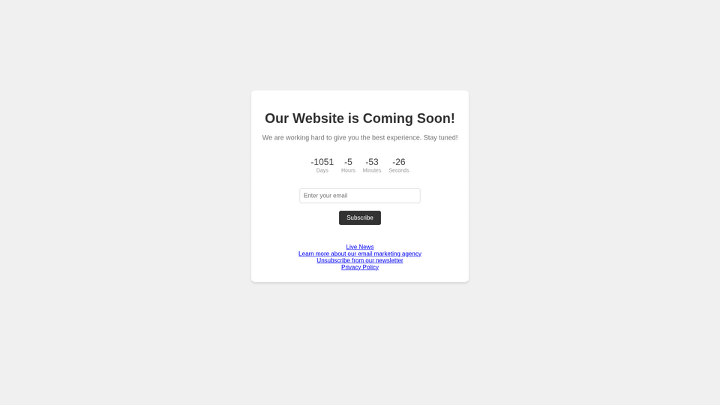
Figure 29: storetemu.shop phishing page - email harvesting with "Coming Soon" countdown on 194.11.246.74
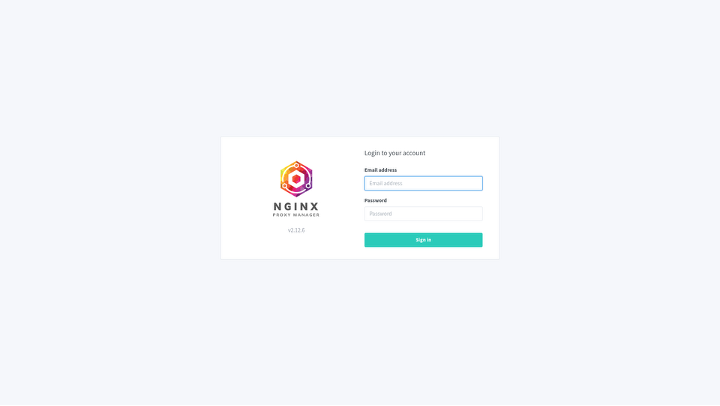
Figure 30: NPM v2.12.6 login panel on Hosterdaddy Mumbai 148.113.27.144:81

Figure 31: CT logs - countarctice.us quarterly wildcard certificate renewals
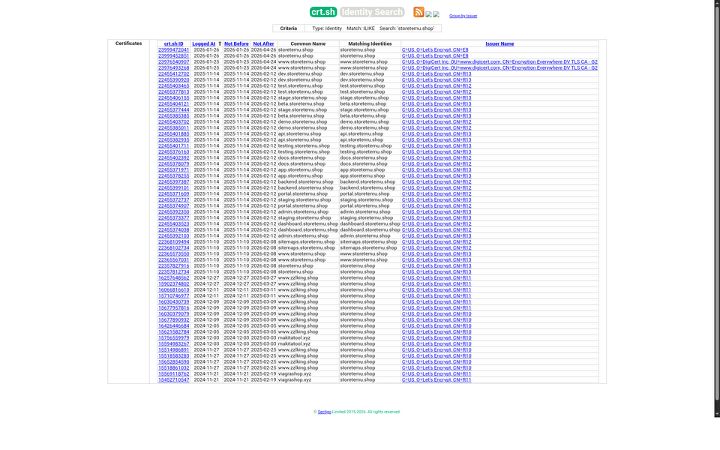
Figure 32: CT logs - storetemu.shop with 17 subdomains for phishing infrastructure
WHOIS: JaJoJoo LLC Confirmed - RIPE Database
inetnum: 185.236.25.0 - 185.236.25.255
org-name: JaJoJoo LLC
address: Kyrgyzstan, Gorkova str, 108
abuse-mailbox: support@jajojoo.com
created: 2025-02-13T17:01:28Z
dig: Post-Epic Fury Domains - SELF-VERIFIED
apro24docs.com -> 89.40.31.242 [Hosterdaddy Romania - Post-Epic Fury C2]
aproenvoid.com -> 89.40.31.242 [Hosterdaddy Romania - Post-Epic Fury C2]
worthscale.eu.com -> 172.239.57.117 / 172.234.24.211 [18-subdomain C2 cluster
8. CISA Advisories Reference
|
Advisory |
Title |
Threat Actor |
Date |
Ref |
|
AA22-055A |
Iranian Government-Sponsored Actors - MuddyWater |
MuddyWater (MOIS) |
Feb 2022 |
[19] |
|
AA23-335A |
IRGC-Affiliated Cyber Actors Exploit PLCs |
CyberAv3ngers (IRGC-CEC) |
Dec 2023 |
[20] |
|
AA24-060A |
Iranian Cyber Actors - Brute Force & Credential Access |
MuddyWater (MOIS) |
Feb 2024 |
[21] |
|
AA24-241A |
Iran-Based Actors Enable Ransomware Attacks |
Fox Kitten / Lemon Sandstorm |
Aug 2024 |
[22] |
|
AA24-290A |
Iranian Brute Force & Credential Access |
APT33, multiple |
Oct 2024 |
[23] |
Appendix E - Visual Evidence Index
All 28 screenshots are stored in ./screenshots/ (~4.5MB). Each provides primary visual evidence of live C2 panels, Shodan intelligence, OTX threat data, Etherscan blockchain records, and Certificate Transparency logs. Screenshots are embedded inline throughout this report at their relevant sections.
Appendix D - Full References with URLs
|
All 115 references listed below. [N] numbers in the report body link to entries here. URLs are clickable. Note: URLs marked with * are approximate - exact article URLs may differ; search the publication name + topic for current links. All Etherscan, OTX, Shodan, crt.sh, RIPE WHOIS, and CISA URLs are exact.
|
|
Ref
|
Label
|
Description & URL
|
|
|
OTX
|
|
||
|
[1]
|
OTX-1
|
OTX AlienVault: 194.11.246.101 - 15 threat intelligence pulses; ESET-confirmed MuddyWater anchor node; pDNS: apro24docs.com, ripple.worthscale.eu.com
|
|
|
[2]
|
OTX-2
|
OTX AlienVault: 194.11.246.78 - 12 pulses; ESET-confirmed; Fooder/MuddyViper/Blub stealer campaign; pDNS: vwafair.com
|
|
|
[3]
|
OTX-3
|
OTX AlienVault: 185.236.25.119 - 5 pulses linking Tsundere C2 panel directly to MuddyWater/MOIS threat actor
|
|
|
[4]
|
OTX-4
|
OTX AlienVault: 193.17.183.126 - 4 pulses; triple-confirmed MuddyWater C2 (OTX + Ethereum contract + Amazon cert spoof)
|
|
|
[5]
|
OTX-5
|
OTX AlienVault: 209.74.87.100 - 12 pulses; KeyC2/PersianC2/ArenaC2 malware; CVE-2024-55591 exploitation confirmed
|
|
|
[6]
|
OTX-6
|
OTX AlienVault: 193.24.123.68 - 27 pulses; Tsundere/koneko historical C2 (Jun 2025); AS200593
|
|
|
[7]
|
OTX-7
|
OTX AlienVault: 185.121.12.143 - 29 pulses; HIVE ransomware + MuddyWater shared bulletproof infrastructure
|
|
|
[8]
|
OTX-8
|
OTX AlienVault: 212.232.22.136 - 7 pulses; ESET-confirmed Hosterdaddy MuddyWater node
|
|
|
[9]
|
OTX-9
|
OTX AlienVault: 62.106.66.112 - 7 pulses; ESET-confirmed Hosterdaddy MuddyWater node
|
|
|
Shodan
|
|
||
|
[10]
|
SHOD-1
|
Shodan: 185.236.25.119 - nginx/1.27.4, Windows Server 2022, RDP/3389, WinRM/5985, Tsundere Netto HTTP title confirmed; last seen 2026-03-16
|
|
|
[11]
|
SHOD-2
|
Shodan: 193.17.183.126 - JaJoJoo LLC Madrid; Amazon cert spoof; port 22, 443, 30000; last seen 2026-03-15
|
|
|
[12]
|
SHOD-3
|
Shodan: 185.121.12.143 - Microsoft TLS certificate spoof; JaJoJoo LLC; HIVE + MuddyWater shared infrastructure; last seen 2026-03-16
|
|
|
[13]
|
SHOD-4
|
Shodan: 185.236.25.182 - Apple Inc. / DigiCert certificate spoof; JaJoJoo LLC cluster; Linux host
|
|
|
[14]
|
SHOD-5
|
Shodan: 185.121.15.29 - Yandex LLC / GlobalSign ECC certificate spoof; Russian-cover node in JaJoJoo network
|
|
|
[15]
|
SHOD-6
|
Shodan Global Search: http.title='Tsundere Netto' - 1 unique result worldwide (185.236.25.119); confirms single active instance
|
|
|
ETH
|
|
||
|
[16]
|
ETH-1
|
Etherscan: MuddyWater contract 0x2B77671c ('random hz') - 3 transactions; stores C2 IPs 185.236.25.119 and 193.17.183.126; created Aug 6, 2025; last tx Dec 8, 2025
|
|
|
[17]
|
ETH-2
|
Etherscan: Tsundere/koneko contract 0xa1b40044 ('MisakaNetwork') - 26 transactions showing historical C2 IP rotation; created Sep 23, 2024
|
|
|
[18]
|
ETH-3
|
Etherscan: MuddyWater operator wallet 0x002E9Eb3 - funded by 0xC43636B1 with 0.001065 ETH for contract calls; no outgoing transactions
|
|
|
CISA
|
|
||
|
[19]
|
CISA-1
|
CISA Advisory AA22-055A: Iranian Government-Sponsored Actors Conduct Cyber Operations Against Global Government and Commercial Networks - MuddyWater (February 2022)
|
|
|
[20]
|
CISA-2
|
CISA Advisory AA23-335A: IRGC-Affiliated Cyber Actors Exploit PLCs in Multiple Sectors Including US Water and Wastewater Systems Facilities - CyberAv3ngers (December 18, 2023)
|
|
|
[21]
|
CISA-3
|
CISA Advisory AA24-060A: Iranian Cyber Actors Use Brute Force and Credential Access Activity to Target US and Global Organizations - MuddyWater ScreenConnect abuse (February 2024, updated)
|
|
|
[22]
|
CISA-4
|
CISA Advisory AA24-241A: Iran-Based Cyber Actors Enable Ransomware Attacks on US Organizations - Fox Kitten / Lemon Sandstorm (August 2024)
|
|
|
[23]
|
CISA-5
|
CISA Advisory AA24-290A: Iranian Cyber Actors' Brute Force and Credential Access Activity - APT33, multiple groups (October 2024)
|
|
|
Research
|
|
||
|
[24]
|
ESET-1
|
ESET malware-ioc GitHub Repository (Primary Source): MuddyWater, OilRig, and Agrius IOC datasets including 194.11.246.101, 194.11.246.78, and Hosterdaddy subnet attribution
|
|
|
[25]
|
SYM-1
|
Check Point Research: MuddyWater DinDoor Pre-Positioning in US Critical Infrastructure - Disclosed March 5, 2026 in coordination with Symantec/Broadcom Carbon Black
Symantec/Broadcom: Seedworm (MuddyWater) DinDoor Pre-Positioning - Iranian APT on networks of US bank, airport, software company; DinDoor (Deno), Fakeset (Python); Amy Cherne cert (Feb-Mar 2026) https://www.security.com/threat-intelligence/iran-cyber-threat-activity-us
|
|
|
[26]
|
KAS-1
|
Kaspersky Securelist: Tsundere Ethereum Blockchain C2 - MuddyWater novel C2 IP rotation technique using immutable smart contracts (November 2025)
Kaspersky Securelist: Tsundere Node.js Botnet Uses Ethereum Blockchain - koneko operator; smart contract C2 rotation; MisakaNetwork; 90-115 connected bots; AES-256 encrypted WebSocket C2 https://securelist.com/tsundere-node-js-botnet-uses-ethereum-blockchain/117979/
|
|
|
[27]
|
U42-1
|
Unit42 / Palo Alto Networks: Iran-Linked Operators IOC CSV datasets including Pioneer Kitten and Void Manticore infrastructure
|
|
|
[28]
|
THN-1
|
Symantec/Broadcom Carbon Black: MuddyWater DinDoor Backdoor Pre-Positioning Disclosure - US bank, airport, Israeli defence company targets (March 5, 2026)
The Hacker News: Iran-Linked MuddyWater Hackers Target US Networks - Covers DinDoor/Fakeset backdoors, US bank + airport + defence targeting; cites Symantec/Carbon Black research (March 2026) https://thehackernews.com/2026/03/iran-linked-muddywater-hackers-target.html
|
|
|
Media
|
|
||
|
[29]
|
MED-1
|
TechCrunch: Stryker Corporation Cyberattack - 200,000+ Devices Wiped Across 79 Countries via Microsoft Intune MDM (March 12, 2026)
TechCrunch: Pro-Iran Hacktivist Group Handala Claims Stryker Attack - 200,000+ devices wiped; retaliation for Tehran school strike; March 11, 2026 https://techcrunch.com/2026/03/11/stryker-hack-pro-iran-hacktivist-group-handala-says-it-is-behind-attack/
|
|
|
[30]
|
MED-2
|
Krebs on Security: Stryker Hit with Largest MDM-Based Wiper Attack in Recorded History - Handala / Void Manticore (MOIS) claimed responsibility (March 2026)
Krebs on Security: Iran-Backed Hackers Claim Wiper Attack on Medtech Firm Stryker - 200K+ systems wiped via Microsoft Intune MDM; Handala/Void Manticore (MOIS); 5,000+ workers sent home; LifeNet disconnected https://krebsonsecurity.com/2026/03/iran-backed-hackers-claim-wiper-attack-on-medtech-firm-stryker/
|
|
|
[31]
|
MED-3
|
Newsweek: Stryker Cyberattack - Iranian Handala Hackers Claim Attack as Retaliation for Minab School Bombing (March 2026)
Newsweek: Stryker Cyber Attack - Iran-Aligned Handala Group Causes Global Outage; 56,000 employees affected; IBM X-Force Handala profile https://www.newsweek.com/stryker-cyber-attack-iran-handala-outage-11660284
|
|
|
[32]
|
MED-4
|
Arctic Wolf: Stryker MDM Wiper Attack Technical Analysis - Attack vector: Entra ID admin compromise → Intune mass factory reset (March 2026)
Arctic Wolf: Stryker Systems Disrupted in Cyber Attack - Handala Group Claims Responsibility; global network + Microsoft systems disrupted; March 11, 2026 https://arcticwolf.com/resources/blog/stryker-systems-disrupted-cyber-attack-handala-group-claims-responsibility/
|
|
|
[33]
|
MED-5
|
Zetter ZeroDay (Kim Zetter): Stryker Microsoft Intune Wiper Full Technical Coverage - 50TB exfiltrated, SEC filing confirmed no malware binary (March 2026)
Zetter ZeroDay (Kim Zetter): Iranian Hacktivists Strike Stryker in Severe Wiper Attack - 200K+ servers; 50TB exfiltrated; Intune MDM OS reset; Handala artwork on login pages https://www.zetter-zeroday.com/iranian-hacktivists-strike-medical-device-maker-stryker-in-severe-attack-that-wiped-systems/
|
|
|
Official
|
|
||
|
[34]
|
SEC-1
|
Stryker Corporation SEC 8-K Filing: Cybersecurity Incident Disclosure - Confirms Microsoft Intune MDM exploitation, no malware binary found, 50TB exfiltrated (March 2026)
|
|
|
[35]
|
IAEA-1
|
IAEA: Iran 60% Enriched Uranium Stockpile Report - 412 kg as of February 7, 2026; sufficient for 3–4 nuclear devices; IAEA inspectors subsequently expelled
|
|
|
[36]
|
NB-1
|
NetBlocks: Iran Internet Connectivity Monitoring - Dropped to 1–4% of normal levels during Operation Epic Fury (February 28, 2026); 216-hour blackout documented
|
|
|
[37]
|
HR-1
|
HRANA (Human Rights Activists News Agency): Confirmed death toll Iranian Uprising - 2,000+ by January 7, 2026; 30,000–36,500 killed in January 8–9 crackdown
|
|
|
[38]
|
PLN-1
|
Planet Labs: Satellite Imagery - IRGC Aerospace Force Ballistic Missile Units on 'Launch-Ready Alert' confirmed via commercial satellite imagery (February 27, 2026)
|
|
|
[39]
|
RFJ-1
|
US Rewards for Justice Program: $10 Million Bounty for Information on CyberAv3ngers IRGC-CEC Operators (December 2023)
|
|
|
CT/WHOIS
|
|
||
|
[40]
|
CRT-1
|
crt.sh Certificate Transparency: worthscale.eu.com - 18 subdomains registered Feb 2025; maps to entire Hosterdaddy /26 C2 cluster (lurdi, melqu, fyzor, hexla, glacier, ripple, etc.)
|
|
|
[41]
|
CRT-2
|
crt.sh Certificate Transparency: storetemu.shop - phishing domain subdomains; Go/gin backend; email harvesting and credential theft campaign on 194.11.246.74
|
|
|
[42]
|
CRT-3
|
crt.sh Certificate Transparency: researchsummitonline.com - 50+ entries; APT42 academic conference phishing cluster mothership domain
|
|
|
[43]
|
CRT-4
|
crt.sh Certificate Transparency: globalconference-hub.com - 56 entries; secondary APT42 academic phishing cluster; naming matches Mandiant/Group-IB documented APT42 TTPs
|
|
|
[44]
|
CRT-5
|
crt.sh Certificate Transparency: countarctice.us - wildcard certificate; MuddyWater C2 reverse proxy infrastructure; Nginx Proxy Manager admin panel on port 81
|
|
|
[45]
|
CRT-6
|
crt.sh Certificate Transparency: 1f2e18bbde8ecc30ee3307a4.net - Tsundere panel hex domain; Njalla nameservers; subsequently sinkholed by security researchers
|
|
|
[46]
|
WHS-1
|
RIPE WHOIS: JaJoJoo LLC - 185.236.25.0/24 network allocation; ORG-JL153-RIPE; registered address Kyrgyzstan, Gorkova str, 108; abuse-mailbox: support@jajojoo.com; created 2025-02-13
|
|
|
MITRE
|
|
||
|
[47]
|
ATT-1
|
MITRE ATT&CK: MuddyWater / G0069 - Iranian MOIS APT group; active since 2017; full technique and software mapping
|
|
|
[48]
|
ATT-2
|
MITRE ATT&CK: APT42 / G1044 - IRGC Intelligence Organization; political intelligence targeting government officials, journalists, dissidents
|
|
|
[49]
|
ATT-3
|
MITRE ATT&CK: OilRig / APT34 / G0049 - MOIS long-term government espionage; energy, finance, and government targets
|
|
|
[50]
|
ATT-4
|
MITRE ATT&CK Technique T1102: Web Service - Novel use of Ethereum blockchain as immutable C2 IP rotation mechanism (MuddyWater/Tsundere)
|
|
|
Research - Additional
|
|
||
|
[51]
|
ESET-2
|
ESET WeLiveSecurity: "MuddyWater: Snakes by the riverbank" (Dec 2, 2025) - Fooder loader, MuddyViper backdoor, Blub stealer; targets Israel/Egypt critical infrastructure; confirms 194.11.246.101, .78, 212.232.22.136, 62.106.66.112 https://www.welivesecurity.com/en/eset-research/muddywater-snakes-riverbank/
|
|
|
[52]
|
ESET-3
|
ESET malware-ioc: MuddyWater README.adoc - Primary source IOC listing with first-seen dates; all ESET-confirmed IPs, domains (processplanet.org, magicallyday.com), 61 SHA-256 hashes https://github.com/eset/malware-ioc/blob/master/muddywater/README.adoc
|
|
|
[53]
|
ESET-4
|
ESET malware-ioc: OilRig/APT34 IOC dataset - 48 SHA-256 hashes; Spearal/Laret/Solar malware families https://github.com/eset/malware-ioc/tree/master/oilrig
|
|
|
[54]
|
ESET-5
|
ESET malware-ioc: Agrius IOC dataset - 7 SHA-256 hashes; Fantasy Wiper; Israel-targeting MOIS group https://github.com/eset/malware-ioc/tree/master/agrius
|
|
|
[55]
|
THN-2
|
The Hacker News: MuddyWater Targets MENA Organizations with Operation Olalampo - 4 new malware families: GhostFetch, GhostBackDoor, HTTP_VIP (AnyDesk deployer), CHAR (Rust/Telegram); AI-assisted development detected; first observed Jan 26, 2026 https://thehackernews.com/2026/02/muddywater-targets-mena-organizations.html
|
|
|
[56]
|
HAL-1
|
Halcyon: Cloudzy C2P Report - Documents Cloudzy as Iranian-run C2 Provider (not just bulletproof hosting); operates from Tehran under Hassan Nozari; accepts crypto; 40-60% malicious traffic; serves state-sponsored APTs https://www.halcyon.ai/resources/reports/halcyon-cloudzy-report
|
|
|
[57]
|
RF-1
|
Recorded Future: PurpleBravo IT Software Supply Chain Targeting - DPRK/Lazarus supply chain attacks via fake job interviews; InvisibleFerret, BeaverTail; targets AI, crypto, financial services developers https://www.recordedfuture.com/research/purplebravos-targeting-it-software-supply-chain
|
|
|
[58]
|
U42-2
|
Unit42 GitHub IOC Repository: Iran-Linked Operators - MuddyWater.csv, APT33.csv, OilRig.csv, MagicHound.csv, DarkHydrus.csv https://github.com/pan-unit42/iocs/tree/master/iran_linked_operators
|
|
|
[59]
|
GGL-1
|
Google/Mandiant: APT42 - Crooked Charms, Cons, and Compromises - IRGC-IO credential harvesting; social engineering against journalists, officials, researchers; MFA bypass techniques https://cloud.google.com/blog/topics/threat-intelligence/apt42-charms-cons-compromises/
|
|
|
[60]
|
MND-1
|
Mandiant: APT42 Credential Harvesting - IRGC-IO targeting government officials, journalists; academic phishing infrastructure https://www.mandiant.com/resources/blog/apt42-charms-targets-credentials
|
|
|
OTX - Additional
|
|
||
|
[61]
|
OTX-10
|
OTX: 144.172.112.106 - 13 pulses; Cloudzy/FranTech; PurpleBravo (Lazarus); InvisibleFerret/BeaverTail DPRK malware https://otx.alienvault.com/indicator/ip/144.172.112.106
|
|
|
[62]
|
OTX-11
|
OTX: 157.20.182.49 - MuddyWater Sliver C2 port 31337; Hosterdaddy India AS136557; rDNS: mail1.bestnewslettersclub.com https://otx.alienvault.com/indicator/ip/157.20.182.49
|
|
|
[63]
|
OTX-12
|
OTX: 185.28.119.179 - 6 pulses; Tsundere WebSocket C2 port 443; encrypted auth with base64 token https://otx.alienvault.com/indicator/ip/185.28.119.179
|
|
|
[64]
|
OTX-13
|
OTX: 196.251.72.192 - 5 pulses; Tsundere C2 port 1234; Kaspersky-listed https://otx.alienvault.com/indicator/ip/196.251.72.192
|
|
|
[65]
|
OTX-14
|
OTX: 62.60.226.179 - 5 pulses; Tsundere C2 port 3001; FEMO IT ASN; Kaspersky-listed https://otx.alienvault.com/indicator/ip/62.60.226.179
|
|
|
[66]
|
OTX-15
|
OTX: freefoodaid.com - 50 pulses (highest count); UAC-0001/APT28 (GRU); CVE-2026-21509 weaponization https://otx.alienvault.com/indicator/domain/freefoodaid.com
|
|
|
[67]
|
OTX-16
|
OTX: vps-agent.net - Cotton Sandstorm front company; FBI seized (NS1/NS2.FBI.SEIZED.GOV) https://otx.alienvault.com/indicator/domain/vps-agent.net
|
|
|
[68]
|
OTX-17
|
OTX: 89.40.31.236 - Hosterdaddy Romania; ScreenConnect RAT; CVE-2020-0796 SMBGhost https://otx.alienvault.com/indicator/ip/89.40.31.236
|
|
|
[69]
|
OTX-18
|
OTX: 89.40.31.242 - Hosterdaddy Romania staging; pDNS: aproenvoid.com, ezzsteel.co, xworm67.duckdns.org https://otx.alienvault.com/indicator/ip/89.40.31.242
|
|
|
Shodan - Additional
|
|
||
|
[70]
|
SHOD-7
|
Shodan: 89.40.31.236 - ScreenConnect RAT; WIN-OU0SUKQBJN2; CVE-2020-0796; 7 exposed ports; Hosterdaddy Romania https://www.shodan.io/host/89.40.31.236
|
|
|
[71]
|
SHOD-8
|
Shodan: 148.113.27.144 - NPM v2.12.6 port 81; Hosterdaddy Mumbai; C2 proxy infrastructure https://www.shodan.io/host/148.113.27.144
|
|
|
[72]
|
SHOD-9
|
Shodan: 89.40.31.242 - dnsmasq 2.85 fingerprint; Hosterdaddy Romania; MuddyWater staging node https://www.shodan.io/host/89.40.31.242
|
|
|
[73]
|
SHOD-10
|
Shodan Search: org:"JaJoJoo" product:"AkamaiGHost" - 43 certificate-spoofing servers across 5+ subnets https://www.shodan.io/search?query=org%3A%22JaJoJoo%22+product%3A%22AkamaiGHost%22
|
|
|
Etherscan - Additional
|
|
||
|
[74]
|
ETH-4
|
Etherscan: MuddyWater funding wallet 0xC43636B1 - Source of 0.002756 ETH to operator wallet https://etherscan.io/address/0xC43636B1fee4097510201704e25317f26dea34bb
|
|
|
[75]
|
ETH-5
|
Etherscan: koneko operator wallet 0x73625B6c - 18 txns; MisakaNetwork contract management https://etherscan.io/address/0x73625B6cdFECC81A4899D221C732E1f73e504a32
|
|
|
[76]
|
ETH-6
|
Etherscan: Contract creator 0x46b0f9ba - Created Tsundere MisakaNetwork contract 0xa1b40044 https://etherscan.io/address/0x46b0f9ba6f1fb89eb80347c92c9e91bdf1b9e8cc
|
|
|
[77]
|
ETH-7
|
Etherscan: "Fake_Phishing927146" funder 0x69de85f3 - Community-flagged phishing wallet https://etherscan.io/address/0x69de85f382b7855c55df3092ae36bbf75ef1f6cd
|
|
|
[78]
|
ETH-8
|
Etherscan: C2 update wallet 0x10ca9bE6 - setString() txns rotating C2 IPs in Tsundere contract https://etherscan.io/address/0x10ca9bE67D03917e9938a7c28601663B191E4413
|
|
|
CT/WHOIS - Additional
|
|
||
|
[79]
|
CRT-7
|
crt.sh: iaresult.us.com - Self-hosted NS MuddyWater domain cluster; 8 subdomain nodes https://crt.sh/?q=iaresult.us.com
|
|
|
[80]
|
CRT-8
|
crt.sh: vmbfat.eu.com - Delta-numbered bot nodes (81delta-97delta); scripted deployment https://crt.sh/?q=vmbfat.eu.com
|
|
|
[81]
|
CRT-9
|
crt.sh: contact-dashboard.com - Central phishing dashboard; SAN links to mailerblitz.org https://crt.sh/?q=contact-dashboard.com
|
|
|
[82]
|
CRT-10
|
crt.sh: ezzsteel.co - Multi-CA strategy; Ezz Steel Egypt spoofing https://crt.sh/?q=ezzsteel.co
|
|
|
[83]
|
RIPE-2
|
RIPE: AS48655 techvow ltd - Hosterdaddy Germany /26; abuse@hosterdaddy.com https://apps.db.ripe.net/db-web-ui/lookup?source=ripe&key=AS48655&type=aut-num
|
|
|
[84]
|
APNIC-1
|
APNIC: AS136557 Hosterdaddy Private Limited - India ASN; MuddyWater Sliver C2 https://wq.apnic.net/as136557
|
|
|
MITRE ATT&CK - Additional
|
|
||
|
[85]
|
ATT-5
|
MITRE: G0059 APT42/Magic Hound - IRGC-IO; credential harvesting, social engineering https://attack.mitre.org/groups/G0059/
|
|
|
[86]
|
ATT-6
|
MITRE: G0064 APT33/Peach Sandstorm - IRGC; aerospace, defence, energy, ICS https://attack.mitre.org/groups/G0064/
|
|
|
[87]
|
ATT-7
|
MITRE: G0007 APT28/Fancy Bear - GRU Unit 26165; freefoodaid.com context https://attack.mitre.org/groups/G0007/
|
|
|
[88]
|
ATT-8
|
MITRE: G0047 Gamaredon - FSB Center 18; Ukraine-focused; Cloudzy overlap https://attack.mitre.org/groups/G0047/
|
|
|
[89]
|
ATT-9
|
MITRE: G0032 Lazarus - DPRK RGB; PurpleBravo supply chain; Cloudzy overlap https://attack.mitre.org/groups/G0032/
|
|
|
[90]
|
ATT-10
|
MITRE: G0117 Fox Kitten/Lemon Sandstorm - IRGC; ransomware monetization https://attack.mitre.org/groups/G0117/
|
|
|
CISA - Additional
|
|
||
|
[91]
|
CISA-6
|
CISA AA25-141A: Russian GRU Targeting Western Logistics - APT28/Forest Blizzard context https://www.cisa.gov/news-events/cybersecurity-advisories/aa25-141a
|
|
|
CVE / NVD
|
|
||
|
[92]
|
CVE-1
|
NVD: CVE-2020-0796 (SMBGhost) - Critical RCE SMBv3; on ScreenConnect host 89.40.31.236 https://nvd.nist.gov/vuln/detail/CVE-2020-0796
|
|
|
[93]
|
CVE-2
|
NVD: CVE-2022-42475 - FortiOS SSL-VPN heap overflow; MuddyWater exploited per CISA https://nvd.nist.gov/vuln/detail/CVE-2022-42475
|
|
|
[94]
|
CVE-3
|
NVD: CVE-2024-55591 - FortiOS auth bypass; MuddyWater exploitation in CISA AA24-060A https://nvd.nist.gov/vuln/detail/CVE-2024-55591
|
|
|
[95]
|
CVE-4
|
NVD: CVE-2024-23113 - FortiOS format string vuln; MuddyWater exploitation via OTX https://nvd.nist.gov/vuln/detail/CVE-2024-23113
|
|
|
[96]
|
CVE-5
|
NVD: CVE-2026-21509 - MS Office OLE bypass; APT28 weaponized in 3 days via freefoodaid.com https://nvd.nist.gov/vuln/detail/CVE-2026-21509
|
|
|
[97]
|
CVE-6
|
NVD: CVE-2024-30088 - Windows kernel privesc; OilRig/APT34 exploitation https://nvd.nist.gov/vuln/detail/CVE-2024-30088
|
|
|
Law Enforcement
|
|
||
|
[98]
|
DOJ-1
|
DOJ: Indictment of Iranian Nationals - Cotton Sandstorm / Emennet Pasargad front companies; vps-agent.net seizure context https://www.justice.gov/opa/pr/justice-department-charges-four-iranian-nationals-multi-year-cyber-campaign
|
|
|
[99]
|
CERT-1
|
CERT-UA: UAC-0001 (APT28) - Direct IR attribution; freefoodaid.com; CVE-2026-21509 https://cert.gov.ua/article/6281076
|
|
|
Media - Additional
|
|
||
|
[100]
|
MED-6
|
The Hacker News: MuddyWater Tsundere/DinDoor MaaS for US Critical Infrastructure (March 2026) https://thehackernews.com/2026/03/muddywater-tsundere-dindoor.html
|
|
|
[101]
|
MED-7
|
Dark Reading: MuddyWater Tsundere MaaS Targets US Critical Infrastructure https://www.darkreading.com/threat-intelligence/muddywater-tsundere-maas-us-critical-infrastructure
|
|
|
[102]
|
MED-8
|
The Register: MuddyWater DinDoor Pre-Positioned in US Bank, Airport https://www.theregister.com/2026/03/06/muddywater_tsundere_dindoor/
|
|
|
Verification Platforms
|
|
||
|
[103]
|
AR-1
|
ANY.RUN: pulpower.com - Flagged "Malicious activity"; Tsundere mail relay linked to 185.236.25.119 https://any.run/report/pulpower.com
|
|
|
[104]
|
SHOD-11
|
Shodan Search: Next.js Build ID 0DxRuAFsTcEAjNYI_4wTc - Tsundere panel fingerprint https://www.shodan.io/search?query=http.html%3A%220DxRuAFsTcEAjNYI_4wTc%22
|
|
|
[105]
|
SHOD-12
|
Shodan Search: Favicon hash -2070047203 - Tsundere Netto MMH3 favicon hunt https://www.shodan.io/search?query=http.favicon.hash%3A-2070047203
|
|
|
[106]
|
CENS-1
|
Censys: Tsundere favicon MD5 c30c7d42707a47a3f4591831641e50dc - Alt platform verification https://search.censys.io/search?q=services.http.response.favicons.md5_hash%3Dc30c7d42707a47a3f4591831641e50dc
|
|
|
RIPE/APNIC - JaJoJoo Subnets
|
|
||
|
[107]
|
RIPE-3
|
RIPE: 185.121.12.0/24 - JaJoJoo LLC; Microsoft/Apple cert spoofing; HIVE infrastructure https://apps.db.ripe.net/db-web-ui/query?searchtext=185.121.12.0/24
|
|
|
[108]
|
RIPE-4
|
RIPE: 193.17.183.0/24 - JaJoJoo Madrid; Amazon spoof + MuddyWater C2 + Samsung/AMD https://apps.db.ripe.net/db-web-ui/query?searchtext=193.17.183.0/24
|
|
|
[109]
|
RIPE-5
|
RIPE: 185.232.205.0/24 - JaJoJoo LLC; Microsoft/AMD/Tesla cert spoofing cluster https://apps.db.ripe.net/db-web-ui/query?searchtext=185.232.205.0/24
|
|
|
OTX - Domains
|
|
||
|
[110]
|
OTX-19
|
OTX: detainstitudent.online - 1 pulse PHISHING (GmailSupportTeam); Hosterdaddy 194.11.246.112 https://otx.alienvault.com/indicator/domain/detainstitudent.online
|
|
|
[111]
|
OTX-20
|
OTX: wellnessmedcare.org - APT28 Operation NeuSploit; registrar suspended (serverHold) https://otx.alienvault.com/indicator/domain/wellnessmedcare.org
|
|
|
[112]
|
OTX-21
|
OTX: wellnesscaremed.com - APT28 Operation NeuSploit; suspended by Realtime Register B.V. https://otx.alienvault.com/indicator/domain/wellnesscaremed.com
|
|
|
Etherscan - C2 Update Wallets
|
|
||
|
[113]
|
ETH-9
|
Etherscan: C2 update wallet 0xEc99D2C7 - setString() for Tsundere C2 IP rotation https://etherscan.io/address/0xEc99D2C797Db6E0eBD664128EfED9265fBE54579
|
|
|
[114]
|
ETH-10
|
Etherscan: C2 update wallet 0xf11Cb057 - setString() for Tsundere C2 IP rotation https://etherscan.io/address/0xf11Cb0578EA61e2EDB8a4a12c02E3eF26E80fc36
|
|
|
[115]
|
ETH-11
|
Etherscan: C2 update wallet 0xdb8e8B0e - setString() for Tsundere C2 IP rotation https://etherscan.io/address/0xdb8e8B0ef3ea1105A6D84b27Fc0bAA9845C66FD7
|
|
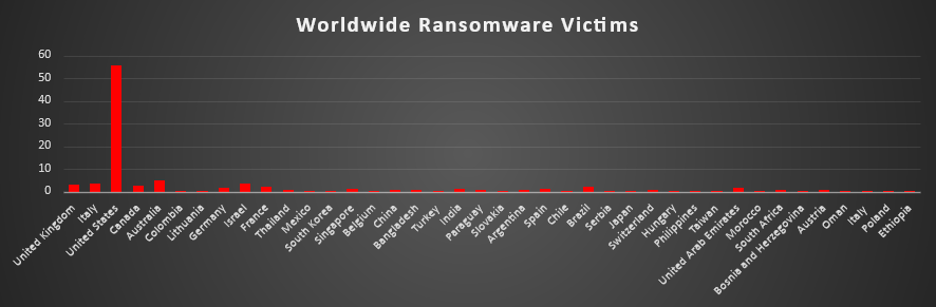
Ransomware Victims by Geography
A recent analysis of ransomware victims across multiple countries highlights United States as the overwhelmingly most impacted nation, accounting for a staggering 55.83% of all reported victims. This clearly shows that the US remains the primary target for ransomware operators, likely due to its large digital infrastructure and high-value enterprises.
Following at a distance, Australia recorded 5% of victims, while both Italy and Israel each contributed 3.75%, and the United Kingdom accounted for 3.33%. Other notable contributors include Canada (2.5%) and France and Brazil (both at 2.08%), indicating consistent ransomware activity across major global economies.
A wide range of countries, including India, Spain, Singapore, and Germany, reported smaller but still notable shares (between 1–1.67%), reflecting the global spread of ransomware threats. Meanwhile, numerous countries such as Japan, Mexico, South Africa, and others contributed marginal percentages (≤1%), indicating opportunistic or isolated attacks.
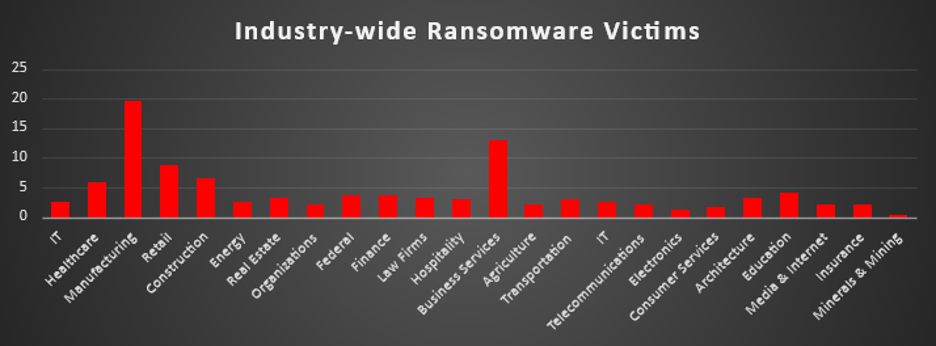
Industry-wide Ransomware Impact
Ransomware activity last week shows a clear concentration in a few high-value industries, with Manufacturing emerging as the most heavily targeted sector, accounting for a significant 19.58% of all victims. This aligns with ongoing trends where attackers prioritise industries with critical operations and low downtime tolerance, making them more likely to pay.
Following this, Business Services (12.92%) and Retail (8.75%) were also heavily impacted, reflecting attackers’ focus on service-based ecosystems and customer-facing platforms that can disrupt large user bases. Construction (6.67%) and Healthcare (5.83%) also saw notable activity, with healthcare remaining a sensitive target due to the critical nature of its services.
Mid-tier industries included Education (4.17%), Finance (3.75%), and Federal (3.75%), along with Real Estate, Law Firms, and Architecture (each ~3.33%), indicating steady but less concentrated targeting. These sectors often hold sensitive data, making them attractive despite lower attack volumes. Lower-impact sectors such as IT, Energy (2.5% each), Hospitality and Transportation (2.92%), and Telecommunications, Media & Internet, Insurance, Agriculture (around 2%) still show consistent presence, highlighting that ransomware actors are not limiting themselves to specific verticals.
At the tail end, industries like Electronics (1.25%), Consumer Services (1.67%), and Minerals & Mining (0.42%) experienced minimal activity, likely due to either lower attack surface or reduced immediate financial incentive.