| New Threats Detection Added | • Installfix |
| New Threat Protection | 98 |
| Newly Detected Threats | 11 |
Weekly Detected Threats
The following threats were added to Crystal Eye this week:
|
Threat name:
|
Installfix | ||||||||||||||||||
|
Installfix is a new attack that imitates legitimate sites such as Claude Code. These sites are identical copies of the official sites but contain instructions for “fake installs” that install infostealer malware onto the devices.
Installfix relies on malicious ads to redirect users to their Claude code site instead of the official site. They instruct the user to copy-and-paste a one-liner command into the terminal. This command would then install and run an infostealer. The infostealer is Amatera which is the ‘updated’ version of ACR Stealer. The malware can be run on both windows and MacOS.
|
|||||||||||||||||||
|
Threat Protected:
|
04 | ||||||||||||||||||
|
Rule Set Type:
|
|
||||||||||||||||||
|
Class Type:
|
Command-and-Control | ||||||||||||||||||
|
Kill Chain:
|
|
||||||||||||||||||
Known Exploited Vulnerabilities (Week 4 - March 2026)
For more information, please visit the Red Piranha Forum:
https://forum.redpiranha.net/t/known-exploited-vulnerabilities-catalog-4th-week-of-march-2026/648.
|
Vulnerability
|
CVSS
|
Description | Affected Version | Fixed Version | |
|
F5 BIG-IP (CVE-2025-53521)
|
9.8
|
Unauthenticated RCE - F5 BIG-IP APM contains an unspecified vulnerability that can allow an unauthenticated remote attacker to execute code on the system. This vulnerability was previously categorised as a Denial of Service (DoS) and has since been re-categorised in March 2026 as Remote Code Execution (RCE).
|
15.1.0 - 15.1.10
16.1.0 - 16.1.6
17.1.0 - 17.1.2
17.5.0 - 17.5.1
|
15.1.10.8
16.1.6.1
17.1.3
17.5.1.3
|
|
|
Aquasecurity Trivy (CVE-2026-33634)
|
9.4
|
Embedded Malicious Code - Aquasecurity Trivy contains embedded malicious code that could allow an attacker to gain access to everything within a CI/CD environment including tokens, SSH keys, cloud credentials, passwords and more. This is a part of a supply chain attack that began in late February 2026 and affected several components including 'aquasecurity/trivy' Go/Container image version 0.69.4, GitHub Actions 'aquasecurity/trivy-action' version 0.0.1 - 0.34.2 and 'aquasecurity/setup-trivy' versions 0.2.0 - 0.2.6. The initial supply chain on Trivy has contributed to additional supply chain attacks against opensource software including BerriAI's LiteLLM PyPi packages v1.82.7 and v1.82.8.
|
Trivy Go/Container 0.69.4
GitHub Action 'aquasecurity/trivy-action' 0.0.1 - 0.34.2
GitHub Action 'aquasecurity/setup-trivy' 0.2.0 - 0.2.6
|
v0.69.2,
v0.69.3
v0.35.0
v0.2.6
|
|
|
Langflow Langflow (CVE-2026-33017)
|
9.3
|
Unauthenticated RCE - Langflow contains a code injection vulnerability that can allow an unauthenticated remote attacker to execute arbitrary python code on the system via a specially crafted HTTP request, exploitation of this vulnerability can result in an attacker gaining access to the underlying server.
|
<= 1.8.2
|
1.9.0
|
Updated Malware Signature (Week 4 - March 2026)
|
Threat
|
Description | |
|
Darksword
|
Darksword is a set of iOS exploits that when chained together allow for full compromise of iOS platforms such as iPhone. The Darksword exploit chain affects all devices that are running iOS version 18.4 to 18.7. The exploit can be triggered by visiting a malicious site requiring minimal user interaction.
|
Ransomware Report |
|
|
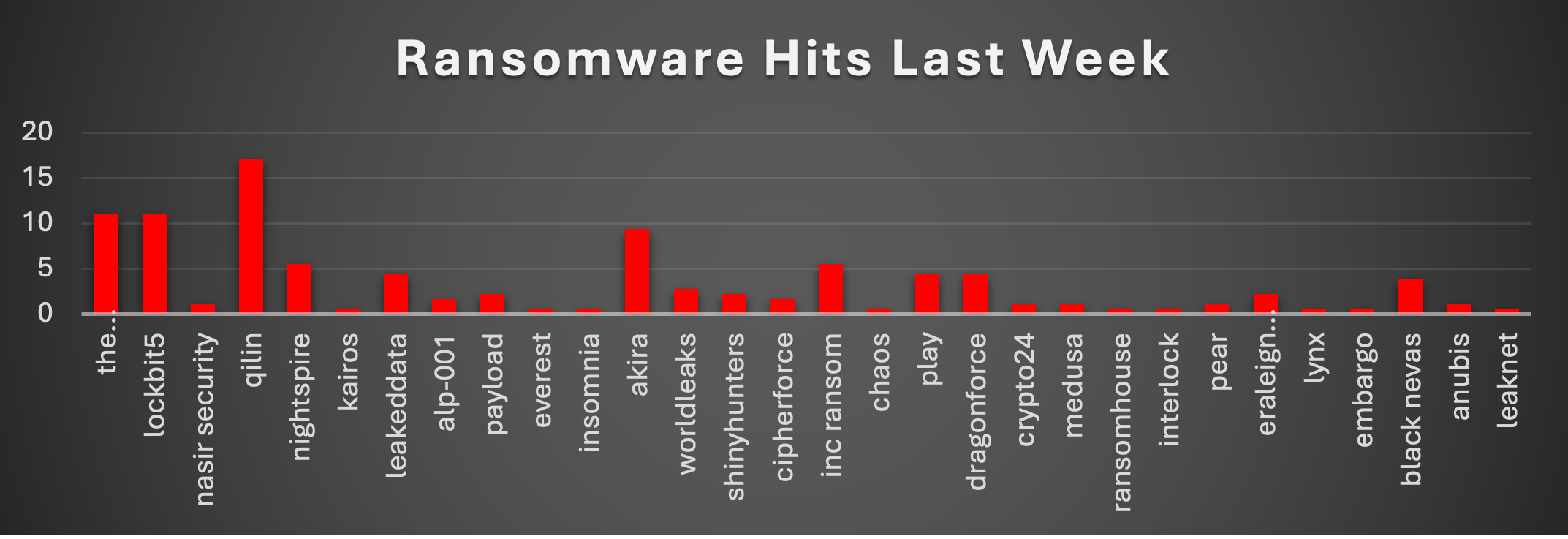
The Red Piranha Team conducts ongoing surveillance of the dark web and other channels to identify global organisations impacted by ransomware attacks. In the past week, our monitoring revealed multiple ransomware incidents across diverse threat groups, underscoring the persistent and widespread nature of these cyber risks. Presented below is a detailed breakdown of ransomware group activities during this period. Ransomware Hits Last WeekRansomware activity last week was heavily dominated by Qilin, which led all groups with 17.13% of total attacks, clearly establishing itself as the most active threat actor in the current cycle. Jointly following are LockBit5 and The Gentlemen, each contributing 11.05%, making them the second most dominant players and reinforcing their continued operational strength. Akira maintained a strong presence at 9.39%, while NightSpire and INC Ransom each accounted for 5.52%, showing consistent mid-to-high level activity. Groups such as LeakedData, Play, and DragonForce (4.42% each) also demonstrated steady campaign execution, indicating a competitive mid-tier landscape. Further down, BlackNevas (3.87%) and WorldLeaks (2.76%) contributed moderate activity, while actors like Payload, ShinyHunters, and Eraleign (APT73) (2.21% each) continued to operate at a controlled but noticeable scale. A long tail of smaller or emerging groups-including CipherForce, Alp-001 (1.66%), and others like Medusa, Crypto24, Anubis (~1.1%) - reflect the ongoing opportunistic attacks. Meanwhile, several groups such as Everest, Chaos, Interlock, LeakNet, Embargo, and others remained at minimal activity levels (~0.55% each). |
BlackNevas Ransomware
BlackNevas ransomware, also referred to as Trial Recovery, is a direct derivative of the Trigona ransomware family that first emerged in late 2024. It has rapidly expanded into a global double-extortion operation targeting large enterprises across healthcare, finance, manufacturing, legal, and telecommunications sectors.
Unlike typical Ransomware-as-a-Service operations, BlackNevas operates independently and does not franchise its payloads. Instead, the operators partner with established ransomware groups (Kill Security, Hunters International, DragonForce, Blackout, Embargo Team, and Mad Liberator) to publish stolen data on their respective leak sites. This partnership model mirrors the approach previously used by the RADAR/Dispossessor operation.
The ransomware employs a hybrid encryption scheme combining AES-256 symmetric encryption with RSA-4112 public key cryptography in Output Feedback (OFB) mode. Configuration data is embedded within each payload and encrypted using multiple layers of AES in CBC mode. Once files are encrypted, no further network communication is performed, significantly reducing detection opportunities post-encryption.
Victims are directed to negotiate via victim-specific email addresses and the @BlackNevas Telegram channel. Ransom notes threaten data publication to partner DLS sites within 7 days if demands are not met. A TOR-based extortion site has been identified at ctyfftrjgtwdjzlgqh4avbd35sqrs6tde4oyam2ufbjch6oqpqtkdtid[.]onion.
Detailed Tactics, Techniques and Procedures (TTPs)
MITRE ATT&CK Mapping
|
Tactic
|
Technique ID
|
Technique Name
|
BlackNevas Context
|
|
Initial Access
|
T1566
|
Phishing
|
Spear-phishing emails with malicious attachments were observed as primary delivery vectors.
|
|
Initial Access
|
T1190
|
Exploit Public-Facing Application
|
Exploitation of known vulnerabilities in internet-facing services for initial foothold.
|
|
Initial Access
|
T1078
|
Valid Accounts
|
Compromised credentials used for authenticated access.
|
|
Execution
|
T1059
|
Command & Scripting Interpreter
|
Ransomware accepts extensive CLI arguments: /fast, /full, /path, /erase, /debug, /stealth, /shdwn, /allow_system, /!lan, /!local.
|
|
Execution
|
T1203
|
Exploitation for Client Execution
|
Client-side exploitation post-phishing delivery.
|
|
Persistence
|
T1547.001
|
Registry Run Keys / Startup Folder
|
BlackNevas achieves persistence via Registry Run keys (confirmed by SentinelOne).
|
|
Privilege Esc.
|
T1068
|
Exploitation for Privilege Escalation
|
Exploitation of local vulnerabilities to escalate privileges.
|
|
Defence Evasion
|
T1027
|
Obfuscated Files/Information
|
Configuration data encrypted using multiple layers of AES-CBC within the payload.
|
|
Defence Evasion
|
T1070
|
Indicator Removal
|
Log and artefact cleanup observed.
|
|
Defence Evasion
|
T1562
|
Impair Defences
|
Attempts to disable security tools and recovery mechanisms.
|
|
Discovery
|
T1083
|
File & Directory Discovery
|
Runtime path analysis – evaluates path strings to determine encryption targets vs exclusions.
|
|
Discovery
|
T1135
|
Network Share Discovery
|
SMB enumeration/spreading capability (toggle: /!lan, /!local flags). Inherited from Trigona.
|
|
Discovery
|
T1012
|
Query Registry
|
Registry queries for system configuration and installed software.
|
|
Lateral Movement
|
T1021.002
|
SMB/Windows Admin Shares
|
Network propagation via SMB shares when /!lan flag is not set.
|
|
Impact
|
T1486
|
Data Encrypted for Impact
|
AES-256 + RSA-4112 hybrid encryption. Files renamed with .-encrypted extension. Default: 10% of file; /fast = 1%; /full = 100%.
|
|
Impact
|
T1561.001
|
Disk Content Wipe
|
/erase switch overwrites file data and applies .-erased extension.
|
|
C2
|
T1071
|
Application Layer Protocol
|
No post-encryption C2 was observed. Communications via Telegram and email only.
|
Validated Command-Line Arguments
The following arguments were confirmed through ASEC debug-mode analysis of live BlackNevas samples:
|
Argument
|
Behaviour
|
|
/allow_system
|
Encrypts system-critical paths (normally excluded)
|
|
/fast
|
Encrypts only 1% of file content for rapid deployment
|
|
/full
|
Encrypts entire file content
|
|
/path
|
Specifies target directory for encryption
|
|
/debug
|
Outputs verbose execution logs including ransomware version info
|
|
/stealth
|
Changes extension and creates ransom note during encryption (covert mode)
|
|
/shdwn
|
Forces system shutdown after encryption completes
|
|
/erase
|
Overwrites file data; applies .-erased extension
|
|
/!lan
|
Disables network share encryption (SMB propagation off)
|
|
/!local
|
Disables local file encryption
|
|
/log
|
Standard verbose log output to txt file
|
|
/short_log
|
Reduced log output (not every function call logged)
|
Encryption Behaviour & File Exclusions
Excluded extensions (to maintain system stability): .sys, .dll, .exe, .log, .bmp, .vmem, .vswp, .vmxf, .vmsd, .scoreboard, .nvram, .vmss. Excluded files: NTUSER.DAT, how_to_decrypt.txt.
Trial-recovery naming convention applied to demonstration files with extensions: .doc, .docx, .hwp, .jpg, .pdf, .png, .rtf, .txt. These files receive the naming format trial-recovery.[random].[random].-encrypted to prove decryption capability to victims
Mitigation
Gateway AV + IDPS (Security Ruleset, Detection & Protection Mode) - Blocks BlackNevas payloads at the perimeter.
Network Segmentation + Inline IDPS per Zone - BlackNevas inherits Trigona's SMB enumeration/spreading capability (toggled via /!lan flag).
ForceField Brute-Force Protection + ZTNA/IAM - BlackNevas operators use valid accounts (T1078) for initial access. ForceField auto-blocks source IPs exceeding failed login thresholds.
DLP + DNS.Insure + Content Filtering - Counters the double-extortion data theft. Configure CE DLP policies to detect anomalous large-volume outbound transfers. Enable DNS.
CE AAI Threat Intelligence Feeds + IOC Blocklists - Ingest all validated BlackNevas IOCs (4 MD5s, 3 SHA256s, 4 operator email addresses, TOR DLS address) into CE custom blocklists. CE's Automated Actionable Intelligence integration with the Cyber Threat Alliance ensures continuously updated signatures as new BlackNevas variants emerge.
Indicators of Compromise (IOCs)
Network / Communication IOCs
|
Type
|
Indicator
|
|
TOR DLS
|
ctyfftrjgtwdjzlgqh4avbd35sqrs6tde4oyam2ufbjch6oqpqtkdtid[.]onion
|
|
Email
|
amsomar[@]consultant[.]com
|
|
Email
|
black4over[@]newlookst[.]com
|
|
Email
|
suppcarter[@]uymail[.]com
|
|
Email
|
paymeuk[@]consultant[.]com
|
|
Telegram
|
@BlackNevas
|
Host-Based Artefacts
|
Artefact Type
|
Detail
|
|
Ransom Note
|
how_to_decrypt.txt (dropped in every directory containing encrypted files)
|
|
File Extension
|
.-encrypted / .ENCRYPTED (encryption mode) | .-erased (erase/wipe mode)
|
|
File Naming
|
Standard: [random].[random].-encrypted | Demo: trial-recovery.[random].[random].-encrypted
|
|
Registry
|
Persistence via Registry Run keys (HKCU/HKLM\Software\Microsoft\Windows\CurrentVersion\Run)
|
Iran-US-Israel Cyber War IOCs
MuddyWater / MOIS Active C2 Nodes
|
IP Address
|
Threat Actor
|
Verdict
|
Top Tags
|
OTX Link
|
|
185.236.25.119
|
MuddyWater
|
Malicious
|
MuddyWater, Tsundere, MOIS
|
ip/185.236.25.119
|
|
193.17.183.126
|
MuddyWater
|
Malicious
|
MuddyWater, Ethereum, Amazon-cert-spoof
|
ip/193.17.183.126
|
|
194.11.246.101
|
MuddyWater
|
Malicious
|
MuddyWater, ESET, Hosterdaddy
|
ip/194.11.246.101
|
|
194.11.246.78
|
MuddyWater
|
Malicious
|
MuddyWater, ESET, Fooder
|
ip/194.11.246.78
|
|
209.74.87.100
|
MuddyWater
|
Malicious
|
MuddyWater, KeyC2, PersianC2
|
ip/209.74.87.100
|
|
89.40.31.242
|
MuddyWater
|
Malicious
|
MuddyWater, Hosterdaddy, post-EpicFury
|
ip/89.40.31.242
|
|
89.40.31.236
|
MuddyWater
|
Malicious
|
MuddyWater, ScreenConnect, RMM
|
ip/89.40.31.236
|
|
212.232.22.136
|
MuddyWater
|
Malicious
|
MuddyWater, ESET, Hosterdaddy
|
ip/212.232.22.136
|
|
62.106.66.112
|
MuddyWater
|
Malicious
|
MuddyWater, ESET, Hosterdaddy
|
ip/62.106.66.112
|
|
157.20.182.49
|
MuddyWater
|
Malicious
|
MuddyWater, Sliver, C2
|
ip/157.20.182.49
|
|
146.19.143.14
|
MuddyWater
|
Malicious
|
MuddyWater, C2
|
ip/146.19.143.14
|
|
136.243.87.112
|
MuddyWater
|
Malicious
|
MuddyWater, C2
|
ip/136.243.87.112
|
|
162.0.230.185
|
MuddyWater
|
Malicious
|
MuddyWater
|
ip/162.0.230.185
|
|
104.237.233.40
|
MuddyWater
|
Malicious
|
MuddyWater
|
ip/104.237.233.40
|
JaJoJoo LLC Certificate-Spoofing Infrastructure
|
IP Address
|
Threat Actor
|
Pulses
|
Top Tags
|
OTX Link
|
|
185.236.25.182
|
JaJoJoo LLC
|
4
|
JaJoJoo, Apple-cert-spoof, APT
|
ip/185.236.25.182
|
|
185.121.15.29
|
JaJoJoo LLC
|
3
|
JaJoJoo, Yandex-cert-spoof, GlobalSign
|
ip/185.121.15.29
|
|
185.121.15.127
|
JaJoJoo LLC
|
3
|
JaJoJoo, Microsoft-cert-spoof
|
ip/185.121.15.127
|
|
185.236.25.233
|
JaJoJoo LLC
|
2
|
JaJoJoo, Microsoft-cert-spoof
|
ip/185.236.25.233
|
|
193.17.183.89
|
JaJoJoo LLC
|
3
|
JaJoJoo, Microsoft-cert-spoof, MuddyWater
|
ip/193.17.183.89
|
|
185.236.25.9
|
JaJoJoo LLC
|
2
|
JaJoJoo, DuckDuckGo-cert-spoof
|
ip/185.236.25.9
|
Domain Indicators with OTX Links
MuddyWater Active C2 + Infrastructure Domains
|
Domain
|
Threat Actor
|
OTX
|
|
worthscale.eu.com
|
MuddyWater
|
domain/worthscale.eu.com
|
|
apro24docs.com
|
MuddyWater
|
domain/apro24docs.com
|
|
aproenvoid.com
|
MuddyWater
|
domain/aproenvoid.com
|
|
countarctice.us
|
MuddyWater
|
domain/countarctice.us
|
|
vwafair.com
|
MuddyWater
|
domain/vwafair.com
|
|
processplanet.org
|
MuddyWater
|
domain/processplanet.org
|
|
magicallyday.com
|
MuddyWater
|
domain/magicallyday.com
|
|
dokedge.de.com
|
MuddyWater
|
domain/dokedge.de.com
|
|
urbpart.us.com
|
MuddyWater
|
domain/urbpart.us.com
|
|
pushbeacon.org
|
MuddyWater
|
domain/pushbeacon.org
|
|
notifyblast.org
|
MuddyWater
|
domain/notifyblast.org
|
|
iaresult.us.com
|
MuddyWater
|
domain/iaresult.us.com
|
|
vmbfat.eu.com
|
MuddyWater
|
domain/vmbfat.eu.com
|
|
pulpower.com
|
MuddyWater / Tsundere
|
domain/pulpower.com
|
|
1f2e18bbde8ecc30ee3307a4.net
|
MuddyWater / Tsundere
|
domain/1f2e18bbde8ecc30ee3307a4.net
|
|
storetemu.shop
|
MuddyWater (phishing)
|
domain/storetemu.shop
|
|
detainstitudent.online
|
Iran-aligned (phishing)
|
domain/detainstitudent.online
|
APT42 Academic Phishing Cluster
|
Domain
|
Threat Actor
|
Verdict
|
OTX Link
|
|
researchsummitonline.com
|
APT42 / Charming Kitten
|
Suspicious
|
domain/researchsummitonline.com
|
|
globalconference-hub.com
|
APT42 / Charming Kitten
|
Suspicious
|
domain/globalconference-hub.com
|
Cotton Sandstorm / APT28 Overlap Domains
|
Domain
|
Threat Actor
|
Verdict
|
Notes
|
OTX Link
|
|
vps-agent.net
|
Cotton Sandstorm / APT28 overlap
|
Malicious
|
FBI seized under warrant.
|
domain/vps-agent.net
|
Named OTX Pulses
|
Threat Actor
|
Pulse Title
|
Key IOCs in Pulse
|
OTX Pulse Link
|
|
MuddyWater
|
MuddyWater Exposed - New C2 Infrastructure 2026
|
194.11.246.101, 209.74.87.100, worthscale.eu.com
|
|
|
MuddyWater
|
Iranian MOIS Cyber Operations - Post Operation Epic Fury
|
89.40.31.242, apro24docs.com, aproenvoid.com
|
|
|
MuddyWater
|
MuddyWater PowerShell C2 Beacons
|
194.11.246.78, 212.232.22.136, vwafair.com
|
|
|
JaJoJoo LLC
|
Iran APT Infrastructure - FranTech/BuyVM Hosting
|
185.236.25.119, 193.17.183.126, 185.121.12.143
|
|
|
MuddyWater/Tsundere
|
Tsundere Botnet Infrastructure - DinDoor Variant
|
193.24.123.68, pulpower.com, 1f2e18bbde8ecc30ee3307a4.net
|
|
|
MuddyWater/Tsundere
|
Iranian APT MuddyWater C2 Servers
|
193.24.123.68, 185.28.119.179, 62.60.226.179
|
|
|
MuddyWater
|
Blockchain-Based C2 Infrastructure
|
185.236.25.119, 193.17.183.126, ETH:0x2B77671c
|
|
|
MuddyWater
|
LevelBlue Labs Pulses - MuddyWater New C2 2026
|
194.11.246.101, 209.74.87.100, 212.232.22.136
|
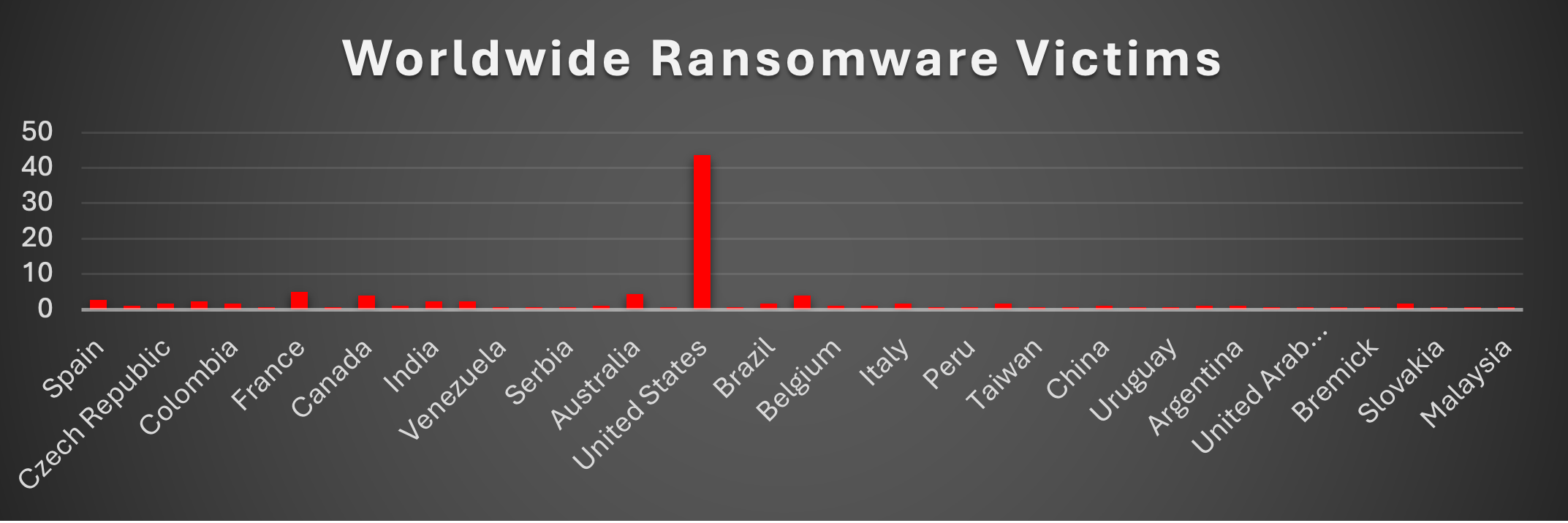
Ransomware Victims by Geography
The latest distribution of ransomware victims again reinforces a very clear pattern: heavy concentration in a single country with global spillover everywhere else.
Leading the chart, United States dominates with 43.65% of all victims-almost half of the global total. This is consistent with broader industry data, where the U.S. typically accounts for ~45–51% of ransomware activity due to its dense, high-value digital ecosystem.
The second tier includes France (4.97%) and Australia (4.42%), followed closely by Canada and Germany (both at 3.87%). These are all economically strong, digitally mature regions-prime targets because attackers expect higher ransom payouts and faster negotiations.
A mid-range cluster includes countries like Spain (2.76%), India (2.21%), Thailand (2.21%), and South Africa (2.21%). These numbers show ransomware is no longer limited to Western economies-it’s actively expanding into emerging and developing markets.
Further down, a wide spread of countries-Brazil, Italy, United Kingdom, Morocco, Colombia, Czech Republic (~1.66%)-show steady but moderate activity, indicating consistent targeting rather than spikes.
Finally, a long tail of countries-including Japan, Malaysia, Saudi Arabia, Portugal, Tunisia, and many others (~0.55%)-reflect opportunistic attacks or isolated incidents.
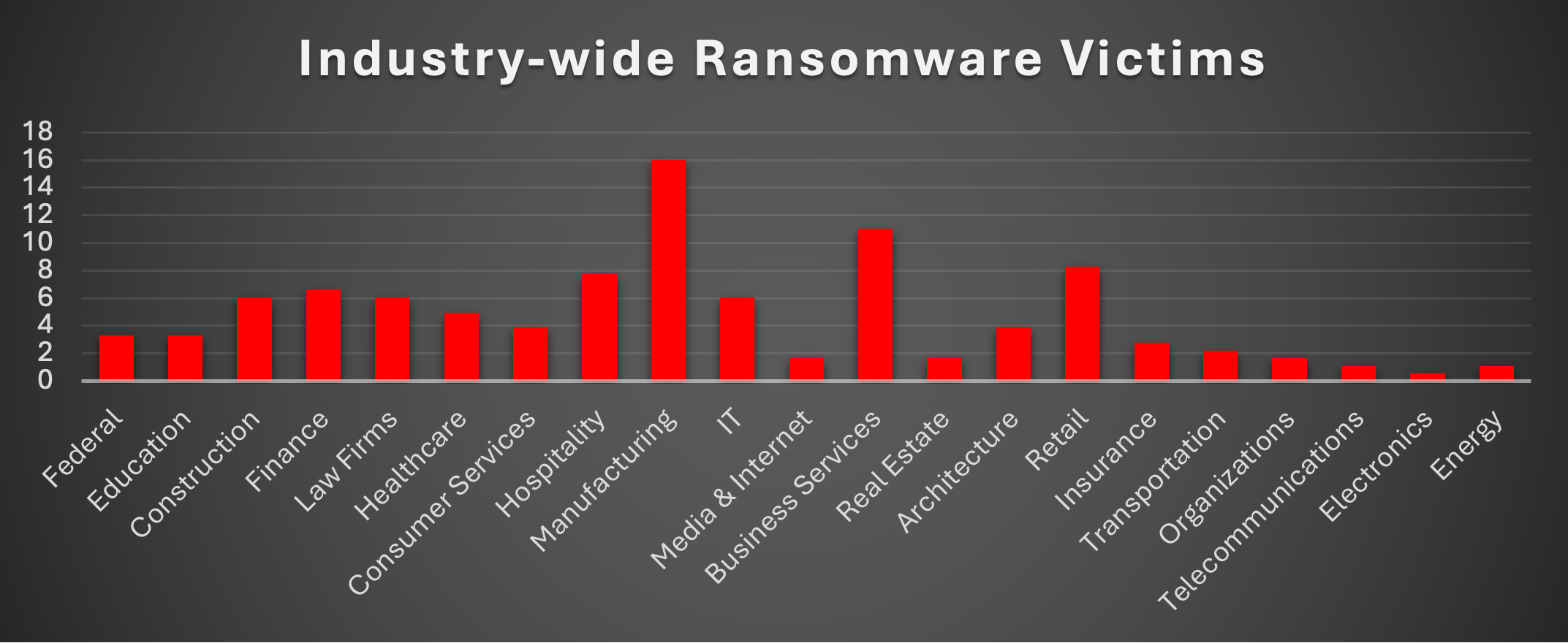
Industry-wide Ransomware Impact
Ransomware activity across industries this week shows a clear concentration in sectors where operational disruption directly translates to financial pressure.
Manufacturing leads by a wide margin at 16.02%, continuing its position as the most targeted industry. This is expected production downtime is equal to immediate losses, making these organisations highly susceptible to ransom demands. Following this, Business Services (11.05%) and Retail (8.29%) show strong targeting, reflecting attackers’ focus on service ecosystems and consumer-facing platforms.
A competitive mid-tier includes Hospitality (7.73%), Finance (6.63%), and a cluster of industries at 6.08%-Construction, Law Firms, and IT. These sectors are valuable due to sensitive data, contractual dependencies, or operational urgency.
Further down, Healthcare (4.97%), Consumer Services (3.87%), and Architecture (3.87%) indicate steady but controlled targeting. These industries remain relevant due to data sensitivity and infrastructure dependencies.
Lower activity sectors include Federal and Education (3.31%), followed by Insurance (2.76%), Transportation (2.21%), and smaller segments like Media & Internet, Real Estate, Organisations (~1.66%).
At the bottom, Telecommunications and Energy (1.1%), and Electronics (0.55%) saw minimal activity-likely due to either stronger defences, lower immediate payout potential, or fewer exposed attack surfaces.