| New Threats Detection Added | • BPFDoor |
| New Threat Protection | 127 |
| Newly Detected Threats | 7 |
Weekly Detected Threats
The following threats were added to Crystal Eye this week:
|
Threat name:
|
BPFDoor | ||||||||||||||||||
|
BPFDoor is a stealthy Linux backdoor used by China-based threat actors that focuses on telecommunications networks. This malware utilises Berkeley Packet Filter (BPF) functionality to inspect network traffic from within the Linux Kernel staying dormant until receiving a specially crafted magic packet. Two additional variants of this backdoor have recently been identified (‘httpShell’, ‘icmpShell’).
The additional of additional variants in combination of BPF makes detection more difficult as it can imitate ‘normal’ traffic such as NTP updates with NDR and EDR failing to detect the malicious packets being sent to and from the infected hosts.
|
|||||||||||||||||||
|
Threat Protected:
|
08 | ||||||||||||||||||
|
Rule Set Type:
|
|
||||||||||||||||||
|
Class Type:
|
Trojan-Activity | ||||||||||||||||||
|
Kill Chain:
|
|
||||||||||||||||||
Known Exploited Vulnerabilities (Week 2 - May 2026)
For more information, please visit the Red Piranha Forum:
https://forum.redpiranha.net/t/known-exploited-vulnerabilities-catalog-2nd-week-of-may-2026/662.
|
Vulnerability
|
CVSS
|
Description | Affected Version | Fixed Version | |
|
9.8 |
Unauthenticated SQLi - BerriAI LiteLLM contains an SQL injection vulnerability that can allow an unauthenticated remote attacker to retrieve and update values from the proxy database by sending a HTTP request with a specially crafted Authorisation header. |
1.81.16 - 1.83.6 |
1.83.7 |
||
|
7.2 |
Authenticated RCE - Ivanti Endpoint Manager Mobile (EPMM) contains a vulnerability that can allow an authenticated remote attacker with administrative access to execute code on the system. |
<= 12.6.1.0 |
12.6.1.1 |
||
|
9.8 |
Unauthenticated RCE - Palo Alto Networks PAN-OS contains an out-of-bounds write vulnerability within the User-ID Authentication Portal (Captive Portal) that can allow an unauthenticated remote attacker to execute code with root level privileges on the device by sending a specially crafted packet. |
Check vendor advisory for affected products and versions
|
|||
Updated Malware Signature (Week 2 - May 2026)
|
Threat
|
Description | |
|
NetSupport Rat
|
NetSupport Rat is a Remote Access Tool capable of avoiding EDR while maintaining persistence and performing data exfiltration and also has info stealer capabilities.
|
Ransomware Report |
|
|
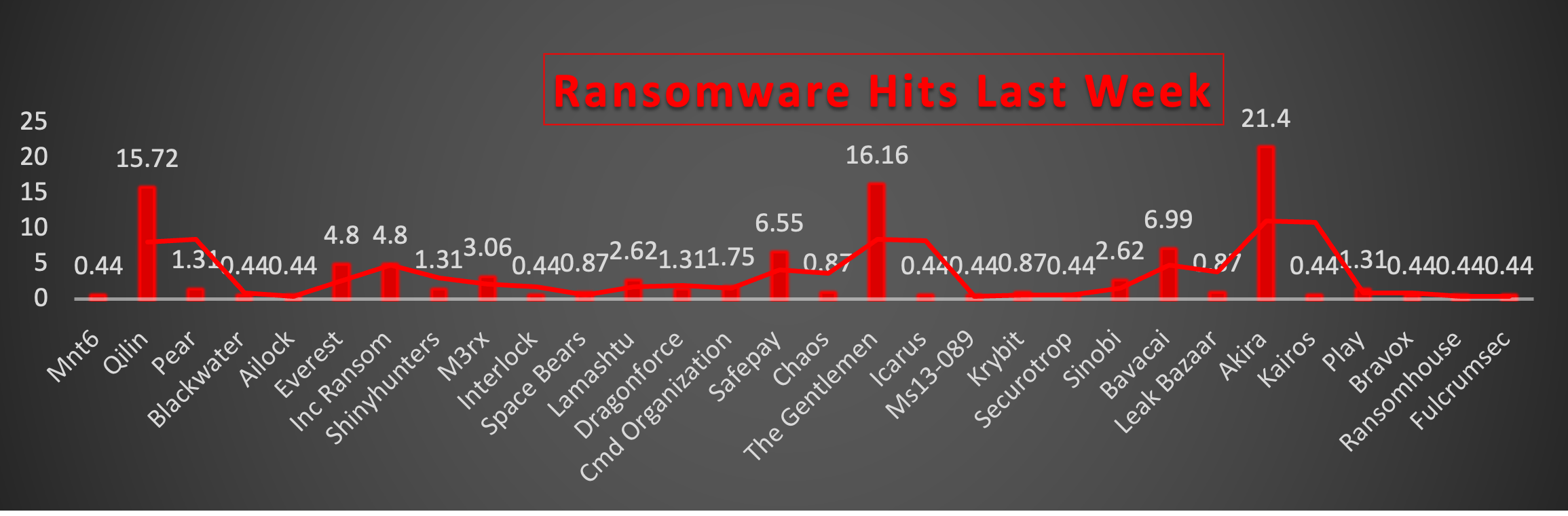
The Red Piranha Team conducts ongoing surveillance of the dark web and other channels to identify global organisations impacted by ransomware attacks. In the past week, our monitoring revealed multiple ransomware incidents across diverse threat groups, underscoring the persistent and widespread nature of these cyber risks. Presented below is a detailed breakdown of ransomware group activities during this period. Ransomware Hits Last WeekRansomware activity this week remained heavily concentrated among a handful of dominant threat groups, with Akira leading overall activity (21.4%), followed closely by The Gentlemen (16.16%) and Qilin (15.72%). These groups collectively accounted for a substantial portion of observed attacks, demonstrating continued operational maturity and aggressive campaign execution. Other highly active actors included Bavacai (6.99%) and SafePay (6.55%), both showing a notable increase in operational presence. Everest and Inc Ransom (4.8% each) maintained steady activity levels, reinforcing their continued role within the active ransomware ecosystem. Moderate campaign activity was observed from M3rx (3.06%), while Lamashtu and Sinobi (2.62% each) continued targeted operations across multiple sectors. CMD Organisation (1.75%), along with Pear, ShinyHunters, DragonForce, and Play (1.31% each), contributed lower but still consistent levels of activity. Overall, the threat landscape continues to reflect a top-heavy ransomware ecosystem, where a few highly active groups dominate global operations while numerous smaller or emerging actors conduct opportunistic attacks. The continued diversity of active groups also highlights the resilience and adaptability of the broader Ransomware-as-a-Service (RaaS) model. |
MNT6 Ransomware
Executive Summary
Red Piranha's threat intelligence team identified MNT6 as a newly active data-leaking ransomware operator during March 2026 monitoring operations. MNT6 was first documented alongside a cohort of other newly emerged threat actors, with an established Tor-based data leak infrastructure observed from its earliest activity.
Leak Site and Dark Web Infrastructure
We confirmed the MNT6 Tor-hosted data leak site through dark web monitoring conducted on 02 May 2026. The following onion address was recorded:
ttvbuilv5mf2wggfjgmvin22ndzghpukhsyy6coz3p4wt5nqnxah7tyd[.]onion
Red Piranha's analysis of the leak site structure identified sequential victim numbering at path /timed-post/[number]/. The Photonic post was recorded at /timed-post/4/.
Extortion, Data Sales, and Exfiltration Staging Model
Red Piranha confirmed through direct observation of MNT6 infrastructure that the group operates three concurrent monetisation and data staging mechanisms:
- Direct victim extortion: MNT6 threatens to publish exfiltrated data unless the victim initiates ransom negotiations, evidenced by the statement observed on the Photonic post: "The full leak will be published soon, unless a company representative contacts us via the channels provided."
- Automated Bitcoin data sales marketplace: An embedded purchase portal on the Tor site allows any third party to buy exfiltrated data directly. Photonic data was listed at 127.83 BTC payable to wallet bc1qnhxd487nx8ca2lmxcdevzdmuf6jqk5dx6nkm80, with automated release after 3 blockchain confirmations.
- MEGA.nz cloud storage for exfiltrated data hosting: Red Piranha identified that MNT6 uses MEGA.nz as the primary hosting platform for staging and distributing exfiltrated victim data. A MEGA.nz folder link was embedded in at least one victim's leak post. The MEGA account was subsequently terminated by MEGA for Terms of Service violation - the data availability status for that link is now unconfirmed.
Red Piranha observed that the MEGA.nz folder link associated with an MNT6 victim post (URL prefix: mega.nz/folder/9U[redacted]) returned the following message: "Folder is no longer available - The account that created this link has been terminated due to a violation of our Terms of Service."
The MEGA account used by MNT6 has been taken down. We cannot confirm or deny whether the data was accessed or downloaded prior to termination. The MEGA.nz base domain remains a confirmed exfiltration platform IOC for MNT6 regardless of this takedown.
TACTICS, TECHNIQUES, AND PROCEDURES
This table contains ONLY TTPs with direct observable evidence identified by Red Piranha from MNT6 infrastructure, victim posts, purchase portal, and the McKay post content. No TTPs are included based on general tradecraft or inference. As of 10 May 2026, no MNT6 malware samples have been identified or analysed.
|
Tactic
|
Technique ID
|
Technique Name
|
|
Reconnaissance
|
T1592
|
Gather Victim Host Information
|
|
Reconnaissance
|
T1589.001
|
Gather Victim Identity Info - Credentials
|
|
Exfiltration
|
T1567.002
|
Exfiltration to Cloud Storage (MEGA.nz)
|
|
Exfiltration
|
T1048
|
Exfiltration Over Alternative Protocol
|
|
Impact
|
T1657
|
Financial Theft / Extortion
|
|
Command-and-Control
|
T1090.003
|
Multi-hop Proxy (Tor)
|
|
Resource Development
|
T1583 / T1608
|
Acquire Infrastructure - Cryptocurrency & Cloud Storage
|
INDICATORS OF COMPROMISE
|
Type
|
Indicator
|
|
Tor Onion - BLOCK
|
ttvbuilv5mf2wggfjgmvin22ndzghpukhsyy6coz3p4wt5nqnxah7tyd.onion
|
|
Bitcoin Wallet - MONITOR & BLOCK
|
bc1qnhxd487nx8ca2lmxcdevzdmuf6jqk5dx6nkm80
|
|
Photonic data for sale
|
127.83 BTC
|
|
Cloud Platform - MONITOR
|
mega.nz
|
|
URL Pattern - MEGA Folder
|
mega.nz/folder/9U[redacted]
|
|
Domain - Victim, DO NOT BLOCK
|
mckay.co.nz
|
|
Domain - Victim, DO NOT BLOCK
|
photonic.com
|
|
Domain - Victim, DO NOT BLOCK
|
silfabsolar.com
|
|
Leak Site URL Pattern
|
/timed-post/[N]/
|
MITIGATION USING RED PIRANHA CRYSTAL EYE 5.5
Mitigations are mapped exclusively to TTPs confirmed by Red Piranha and to verified IOCs, including MEGA.nz exfiltration platform usage.
Controls Mapped to Confirmed MNT6 TTPs
- Create a local IDPS rule in Crystal Eye targeting the confirmed MNT6 Tor onion address. Set to Detection & Protection (inline block) mode across all security zones. Blocks access to the data leak site, purchase portal, and any Tor-based C2 channels.
- Configure Crystal Eye SWG to:
- block the Tor network category.
- block or restrict MEGA.nz upload and share-link traffic for internal hosts. MNT6 confirmed to use MEGA.nz /folder/ share links for exfiltrated data staging. Prevent upload of data to MEGA.nz from internal endpoints.
- Ingest confirmed IOCs into Crystal Eye AAI: (1) Bitcoin wallet bc1qnhxd487nx8ca2lmxcdevzdmuf6jqk5dx6nkm80; (2) mega.nz as a flagged exfiltration platform for high-risk egress correlation. Alert on any internal host initiating connections to MEGA.nz upload endpoints.
General Ransomware Hardening - Best Practice (Not MNT6-Specific)
- Enable Crystal Eye IDPS in Detection and Protection mode with the full Red Piranha backend ruleset across all security zones.
- Enable Crystal Eye Gateway Antivirus with signature and heuristic scanning on all ingress and egress traffic.
- Enable Crystal Eye M365 DLP integration to detect anomalous SharePoint and OneDrive data movement and block phishing-delivered payloads.
- Enforce MFA on all VPN, RDP, and M365 access points. Segment and isolate backup infrastructure to ensure it remains offline and immutable.
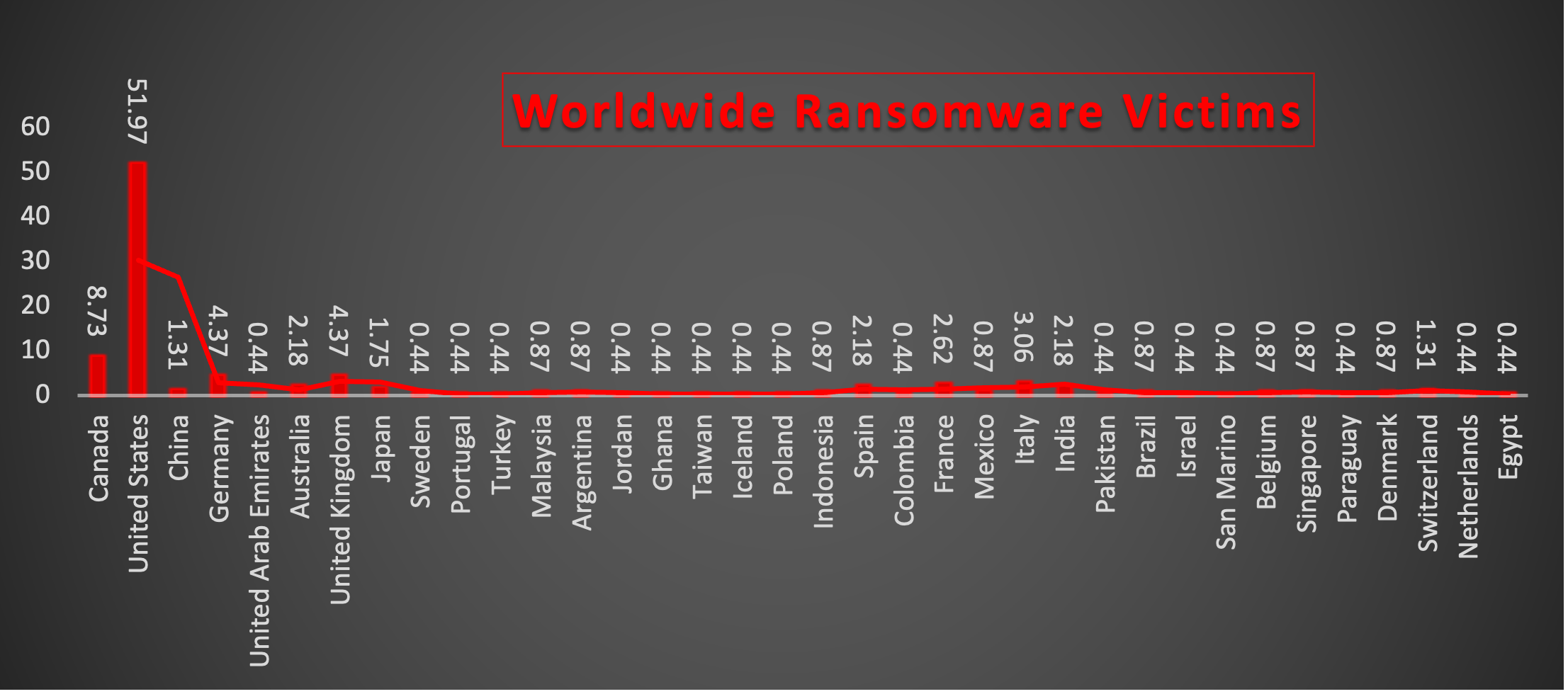
Worldwide Ransomware Victims
Ransomware activity this week remained heavily concentrated in North America, with the United States accounting for the majority of global incidents (51.97%). The continued dominance of the U.S. reflects its large enterprise footprint, high-value targets, and broad exposure across critical industries.
Canada (8.73%) recorded the second-highest level of activity, while Germany and the United Kingdom (4.37% each) continued to experience notable ransomware pressure, reinforcing the ongoing targeting of major Western economies.
Moderate activity was observed in Italy (3.06%) and France (2.62%), followed by Australia, Spain, and India (2.18% each). These regions continue to face steady ransomware operations driven by both opportunistic affiliates and organised threat groups.
Additional activity was distributed across Japan (1.75%), and China and Switzerland (1.31% each), indicating continued campaign expansion across Asia-Pacific and European regions. Countries including Malaysia, Argentina, Indonesia, Mexico, Brazil, Belgium, Singapore, and Denmark (0.87% each) experienced lower but recurring levels of ransomware activity.
Isolated incidents were reported across a broad range of countries including United Arab Emirates, Sweden, Portugal, Turkey, Jordan, Ghana, Taiwan, Iceland, Poland, Colombia, Pakistan, Israel, San Marino, Paraguay, Netherlands, and Egypt (0.44% each). This demonstrates the continued global reach of ransomware operations, even in regions with comparatively lower attack volumes.
Overall, the geographic distribution highlights a continued preference for economically mature and digitally dependent nations, while also showing that ransomware groups maintain broad international targeting strategies across multiple continents simultaneously.
Overall, the geographic spread highlights the continued focus on developed and digitally mature economies, while also demonstrating that ransomware groups are maintaining broad international targeting strategies across multiple regions simultaneously.
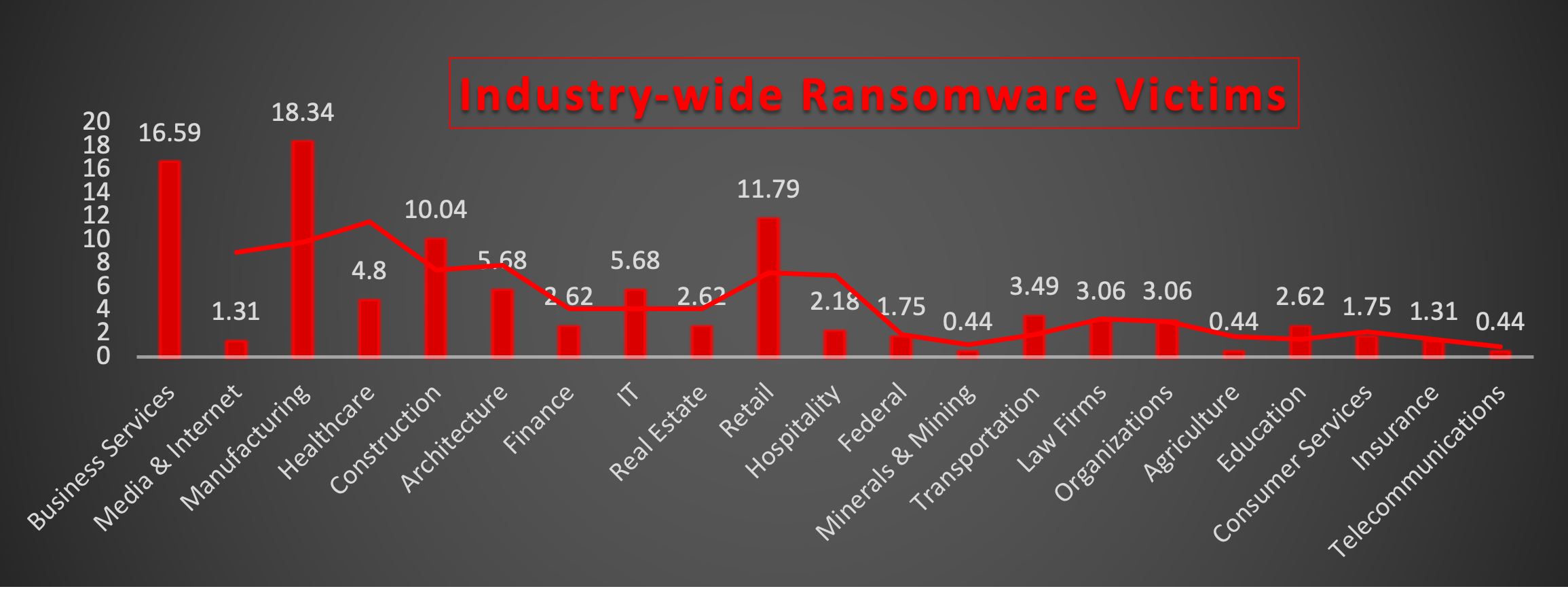
Industry-wide Ransomware Impact
Ransomware activity this week was primarily concentrated in Manufacturing (18.34%) and Business Services (16.59%), making them the most targeted industries during the reporting period. The continued focus on these sectors reflects attackers’ preference for organisations with critical operational dependencies and high disruption impact.
The Retail sector (11.79%) and Construction (10.04%) also experienced significant ransomware activity, highlighting sustained targeting of industries with broad supply chains, distributed infrastructure, and operational urgency. Architecture and IT (5.68% each), along with Healthcare (4.8%), continued to face notable threats, indicating persistent pressure on both technology-driven and service-oriented environments.
Moderate activity was observed across Transportation (3.49%), and Law Firms and Organisations (3.06% each), while Finance, Real Estate, and Education (2.62% each) maintained lower but consistent levels of targeting.
Additional sectors including Hospitality (2.18%), Federal and Consumer Services (1.75% each), and Media & Internet and Insurance (1.31% each) experienced scattered ransomware incidents, suggesting broader opportunistic campaign activity across multiple verticals.
Minimal activity was recorded within Minerals & Mining, Agriculture, and Telecommunications (0.44% each), reflecting either lower exposure or reduced targeting priority during this period.
Overall, the distribution demonstrates that ransomware operators continue to prioritise industries where operational downtime, business continuity disruption, and sensitive data exposure create strong leverage for extortion and ransom negotiations.