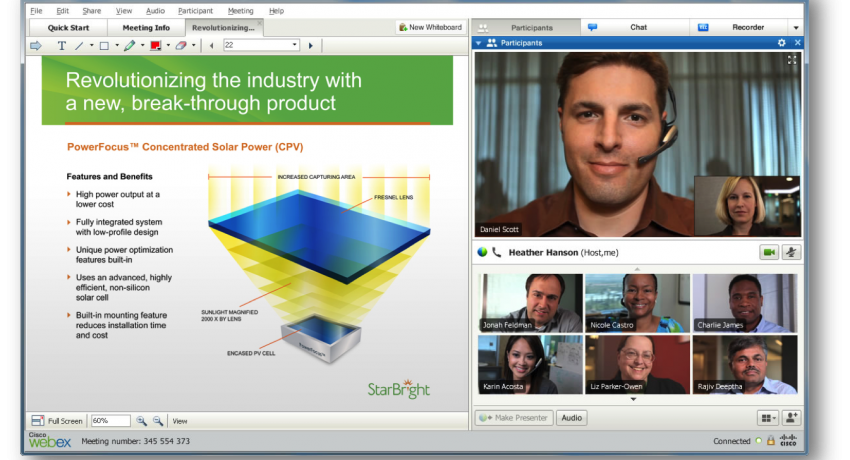
As per the security advisory issued by Cisco on May 10, 2017 it has accepted and further disclosed the fact that the widely used Cisco WebEx Meetings Server is prone to an information-disclosure vulnerability. The Cisco WebEx Meetings Server which is a fully virtualized solution for conferencing allows its users to combine audio, video, and web conferencing in one single platform.
The security advisory issued by the networking giant further states that the vulnerability may allow the attacker to obtain sensitive information that may allow them to aid further attackers. The versions of Cisco WebEx Meetings Servers have been deemed vulnerable are 2.8, 2.7, 2.6, and 2.5.
To be specific, the vulnerability allows attackers to remotely gain information that could allow them to access customer meetings that have been scheduled for a specific date and time.
On June 27, 2016 Cisco has declared in a bulletin that it would be discontinuing its support for Cisco WebEx Meetings Server 2.0, 2.5, 2.6 and 2.7. However, the versions that have been tested for not being vulnerable are Cisco WebEx Meetings Server 2.8 Patch 1, Cisco WebEx Meetings Server 2.7MR2 Patch 6,
Cisco WebEx Meetings Server 2.6MR3 Patch 4 and Cisco WebEx Meetings Server 2.5MR6 Patch 6.
Cisco has clearly mentioned its latest security advisory that, ‘’The vulnerability is due to an incomplete configuration of the robots.txt file on customer-hosted WebEx solutions and occurs when the Short URL functionality is not activated. All releases of Cisco WebEx Meetings Server later than release 2.5MR4 provide this functionality’’.
An indexed meeting can be searched by the attacker by using an exposed parameter and if the exploit is executed successfully the meeting details can be obtained. Once these details are procured the information can further be used by the attacker to break-into a scheduled customer meeting.
The vulnerability was discovered and reported by Mohammed Adel. The fixed releases can be downloaded from the official downloads page of the Cisco website.
