Red Piranha’s threat intelligence team actively monitors ransomware groups and dark web activity. We track emerging threats and attack trends in real time. In one recent case, we investigated Sinobi ransomware group.
Sinobi ransomware is not a classic smash-and-encrypt crew. This is a data-broker extortion group that treats your environment like an inventory warehouse, not a battlefield. They move quietly, pull what they need, and only reveal themselves when the leak site goes live.
The result is a threat that is harder to spot early, messier to remediate, and far more damaging to reputation. What follows is a full breakdown of how this group operates, how their infrastructure works, and why their TTPs make them particularly dangerous for organisations that rely heavily on email, cloud identity, and unmonitored file shares.
Sinobi Ransomware: Complete Analysis, Leak Sites, IOCs, and Defence Strategy
Who is the Sinobi Ransomware Group?
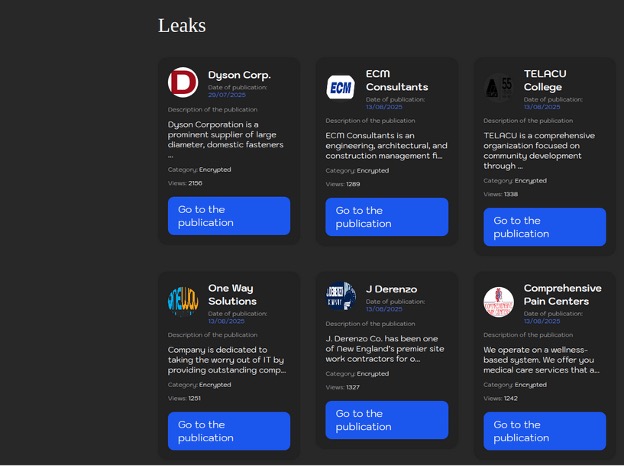
Sinobi ransomware emerged in mid-2025, positioning themselves squarely in the steal-and-leak economy. They are not as noisy or brand-driven as some of the big encrypt-first ransomware operators. Instead, their value proposition is simple: steal everything they can, bundle it, publish it on Tor, and pressure victims until payment appears worth it. During most observed intrusions, the core objective is exfiltration, not encryption.
The crew maintains several Tor-only domains for leaks, chat, and negotiation. They sometimes spin up temporary clearnet mirrors to help victims access negotiation portals, though the real operational infrastructure sits entirely on Tor. Because of this, static C2 indicators like fixed IP addresses rarely appear in telemetry. Detection tends instead to revolve around access to .onion portals, sudden spikes in archiving activity, and unusual outbound data flows.
The Sinobi Ransomware Kill Chain: Tactics, Techniques and Procedures (TTPs)
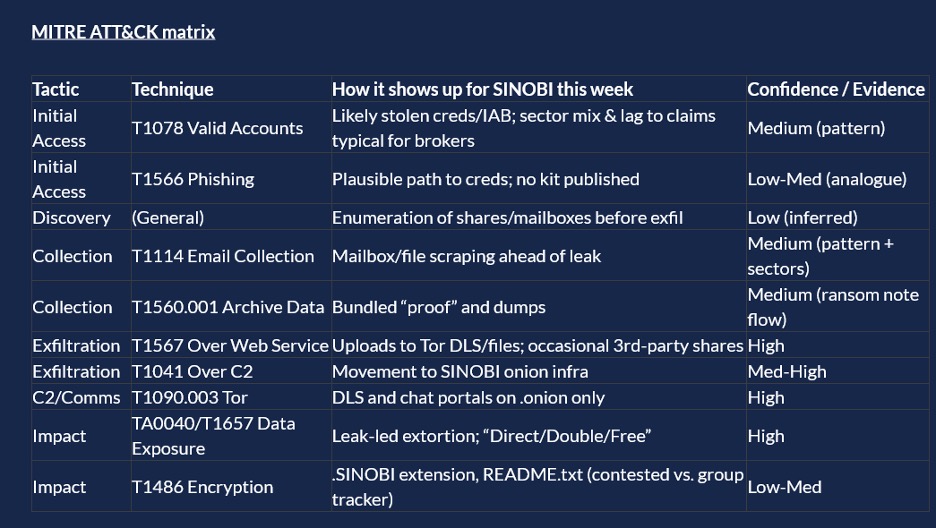
Caption: Sinobi MITRE ATT&CK matrix
Most signs point to credential abuse. The sectors they’ve hit; insurance, construction, education are the typical playground of brokers who reuse stolen VPN, O365, and SSO credentials sourced through infostealers or initial-access brokers. MITRE ATT&CK maps this cleanly to T1078 (Valid Accounts), and the pattern fits. Once inside, they behave less like a ransomware gang and more like a traditional intrusion crew hunting for mailbox access, file shares, and anything that contains sensitive personal or financial data.
Phishing is another plausible entry point. While no Sinobi-specific phishing kit has been documented, their tradecraft suggests opportunistic mailbox compromise that later provides a foothold for deeper network access. This aligns with T1566 (Phishing), though confidence here remains moderate.
Sinobi’s behaviour is consistent with a disciplined data-theft operation. They enumerate shares and mailboxes, then begin scraping emails and documents. The discovery stage isn’t always visible in logs, but collection patterns show heavy mailbox access, pulling PST files, and large file-share reads. This mirrors T1114 (Email Collection).
Once they have what they want, they prepare bundles. You’ll often see compression of large directories, creation of archives, and evidence of “proof packs” that will eventually appear on their leak portal. This is straight down the line with T1560.001 (Archive Collected Data).
From there, exfiltration begins. Everything goes through Tor or related anonymity paths. Sinobi uploads material to their own onion-hosted file servers, sometimes mixing in third-party sharing platforms when dealing with victims during negotiations. These behaviours map to both T1567 (Exfiltration Over Web Services) and T1041 (Exfiltration Over C2 Channel). The common thread is that they avoid anything that leaves clean, attributable infrastructure behind.
Since all known Sinobi operational portals reside on Tor, C2 is routed entirely through anonymity networks. You won’t see fixed IPs. You won’t see stable domains. Instead, defenders typically observe attempts to access Tor gateways, tor2web proxies, and onion endpoints. Their infrastructure list is long, with seven confirmed leak sites and seven chat portals. These serve as both staging points and extortion channels. Everything lines up with T1090.003 (Tor).
Sinobi relies on publication pressure, not operational disruption. They follow the usual “Direct leak, Double leak, Free leak” model. First they threaten, then they publish name-and-shame entries, and if no negotiation occurs, they release the data openly to prove their point. This fits squarely into TA0040/T1657 (Data Exposure & Coercion).
Encryption remains a grey area. Some victims report the .SINOBI extension and ransom notes, but the pattern is inconsistent and not backed by their leak-site messaging. If encryption does occur, it’s likely a secondary capability rather than their primary business model.
What are the Indicators of Compromise (IOCs) of Sinobi Ransomware?
Caption: Indicator of Compromise
Their onion domains for both leaks and chat are numerous, stable, and central to their operations. These include:
Leak portals (7):
sinobi6ftrg27d6g4sjdt65malds6cfptlnjyw52rskakqjda6uvb7yd.onion
sinobi6rlec6f2bgn6rd72xo7hvds4a5ajiu2if4oub2sut7fg3gomqd.onion
sinobi6ywgmmvg2gj2yygkb2hxbimaxpqkyk27wti5zjwhfcldhackid.onion
sinobi7l3wet3uqn4cagjiessuomv75aw3bvgah4jpj43od7xndb7kad.onion
sinobi7sukclb3ygtorysbtrodgdbnrmgbhov45rwzipubbzhiu5jvqd.onion
sinobi23i75c3znmqqxxyuzqvhxnjsar7actgvc4nqeuhgcn5yvz3zqd.onion
sinobia6mw6ht2wcdjphessyzpy7ph2y4dyqbd74bgobgju4ybytmkqd.onion
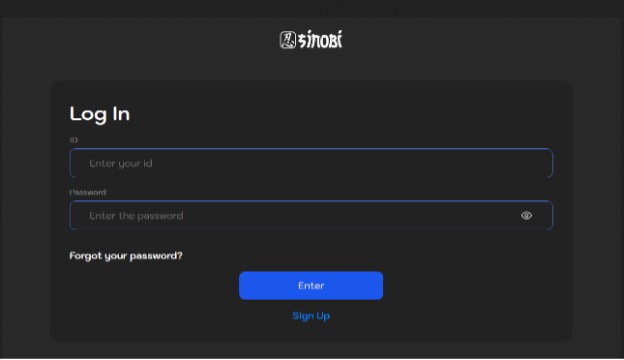
Caption: Sinobi data leak site
Negotiation portals (7):
sinobi7yuoppj76qnkwiobwfc2qve2xkv2ckvzyyjblwd7ucpptl62ad.onion/login
sinobi57mfegeov2naiufkidlkpze263jtbldokimfjqmk2mye6s4yqd.onion/login
sinobibdvzohujkliofkxiz3ueyedfh6bed2lzjz2z6pafw5jeoptsid.onion/login
sinobibjqytwqxjw24zuerqcjyd3hoow6zia7z6kzvwawivamu7nqayd.onion/login
sinobicrh73ongfuxjajmlyyhalvkhlcgttxkxaxz3gvsgdcgf76uiqd.onion/login
sinobidxodgt4jsr3tlmf2rr4okjvvwfp5gh3lrqxnowomcx62ssrhqd.onion/login
sinobiea4snfqtkc43paumapo4oi7vxcy5vjzfoalunsnvzehozfhpyd.onion/login
They have also stood up clearnet mirrors such as blog.sinobi.us.org and chat.sinobi.us.org, usually short-lived and primarily meant to guide fewer technical victims toward negotiation.
How Red Piranha’s Crystal Eye Detects and Prevents Sinobi Ransomware Attacks
Red Piranha’s Threat Detection, Investigation, and Response (TDIR) solution, particularly the Crystal Eye solution, is uniquely equipped to detect and prevent Sinobi ransomware’s Tactics, Techniques, and Procedures (TTPs) through a combination of advanced monitoring, integrated threat intelligence, and proactive defense strategies. Below is an analysis of how Crystal Eye’s capabilities can detect and prevent Sinobi ransomware’s attack stages and techniques:
Sinobi’s entire playbook depends on quiet credential abuse, mailbox scraping, bulk archiving, and Tor-based exfiltration. But Crystal Eye exposes this immediately through its unified visibility layer that offers ten-times greater insight across networks, endpoints, and cloud systems. Anomalous login attempts, unexpected OAuth grants, mailbox-rule manipulation, and access coming from untrusted regions are flagged in real time. The platform's proactive threat hunting and contextual threat intelligence identify known TTPs and trigger alerts based on patterns from its integrated TDIR and Network Detection and Response (NDR)modules.
Because Sinobi depends on silent mailbox scraping and bulk data collection, Crystal Eye’s behavioural analytics quickly detect unusual PST extractions, mass file-share reads, and unexpected archive creation, signalling the early stages of staged exfiltration. Integrated threat intelligence correlates to Tor-related metadata and onion-domain indicators, surfacing Sinobi’s infrastructure even when the group hides behind anonymity networks.
Suspicious file hashes and behavior are detected using real-time threat intel feeds, while push-button escalation to Red Piranha's SOC ensures expert intervention without delay. Crystal Eye’s multi-layered defence approach combines Network Detection and Response (NDR), machine learning-driven anomaly detection, and Zero Trust architecture to counter Sinobi ransomware’s tactics effectively.
As Sinobi transitions into exfiltration and extortion, Crystal Eye’s multi-layered detection engine blocks the core behaviours that make the group effective. Tor client execution, covert data movement, and abnormal outbound transfers are intercepted by Crystal Eye’s IDS/IPS, Secure Web Gateway, and encrypted-traffic inspection modules.
Crystal Eye Attack Surface Reduction (CEASR) app’s whitelisting prevents unauthorised compression utilities, exfiltration tools, and unknown applications from launching at all, cutting off Sinobi’s ability to package and transmit stolen data. If suspicious behaviour is detected, Crystal Eye’s SOAR automation isolates compromised endpoints, halts ongoing data theft, and deploys machine-speed response workflows without waiting for human intervention.
Long-term log retention, integrated PCAP analysis, and unified dashboards give defenders the forensic depth needed to trace attempted exfiltration back to its source, while Policy-as-Code and Zero Trust enforcement harden the environment to prevent repeat compromise. In short, Crystal Eye doesn’t just respond to Sinobi; it hunts, blocks, and neutralises the group’s tactics before any data ever reaches a leak site.
Are You Prepared to Defend Against Sinobi Ransomware?
Crystal Eye, best-in-class Threat Detection, Investigation and Response (TDIR), allows you to catch what the other products in its class missed by detecting all known malware and C2 callouts.
Improve your organisation's security posture and minimise risk to your organisation with our Network Detection and Response program alongside the Managed Detection and Response (MDR) service.
Secure your organisation against advanced ransomware threats like Sinobi. Speak with our cyber experts today to strengthen your security posture. Get in touch here.
